Added to hosts and Let’s get started.
Recon:
Nmap Scan
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-11-16 19:33 IST
Nmap scan report for greenhorn.htb (10.10.11.25)
Host is up (0.51s latency).
Not shown: 997 closed tcp ports (conn-refused)
PORT STATE SERVICE
22/tcp open ssh
| ssh-hostkey:
| 256 57:d6:92:8a:72:44:84:17:29:eb:5c:c9:63:6a:fe:fd (ECDSA)
|_ 256 40:ea:17:b1:b6:c5:3f:42:56:67:4a:3c:ee:75:23:2f (ED25519)
80/tcp open http
| http-robots.txt: 2 disallowed entries
|_/data/ /docs/
3000/tcp open ppp
Nmap done: 1 IP address (1 host up) scanned in 165.14 seconds
- We have multilpe things to explore
- API, Login, Register, Explore has Some Repo
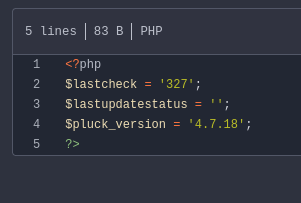
- In Admin Repo - found usage of pluck v4.7.18 : Vulnerable to RCE,
- we need creds to perform RCE
- we found password in GreenAdmin Repo, took lot of time as we were exploring to get somehting and it paid off.
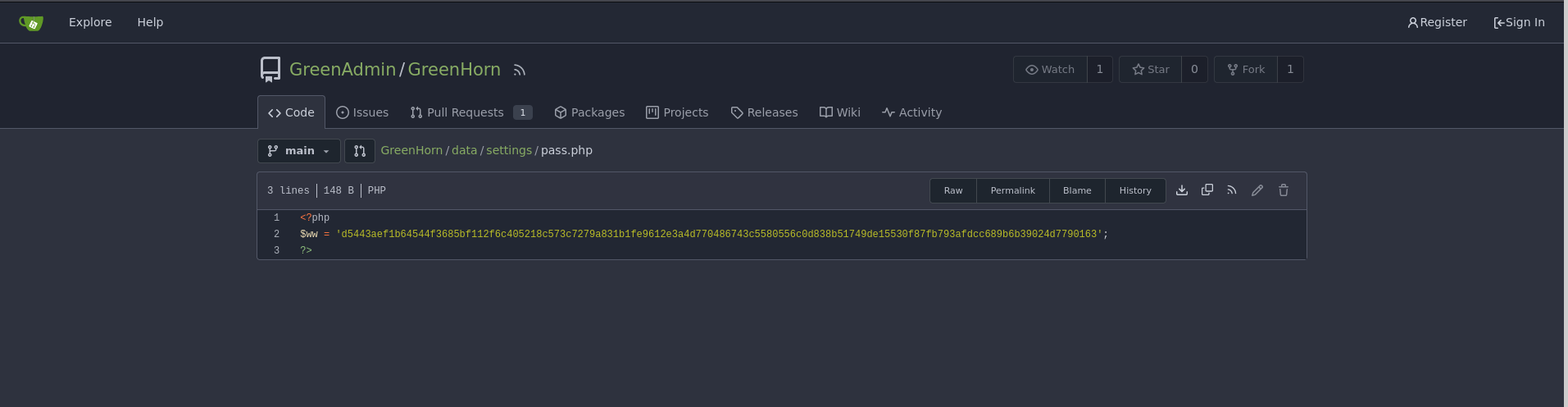
- and reading other several php files, it is encrypted with SHA512
- saved the hash to file and cracked with JohnTheRipper
- pass : iloveyou1
Exploitation - Access:
- we found RCE can be done on this pluck CMS v4.7.18 as found earlier
- Found PoC on google
- https://github.com/Rai2en/CVE-2023-50564_Pluck-v4.7.18_PoC
- going over to site open on port 80 we can use our password there to login as admin and we got option to upload.
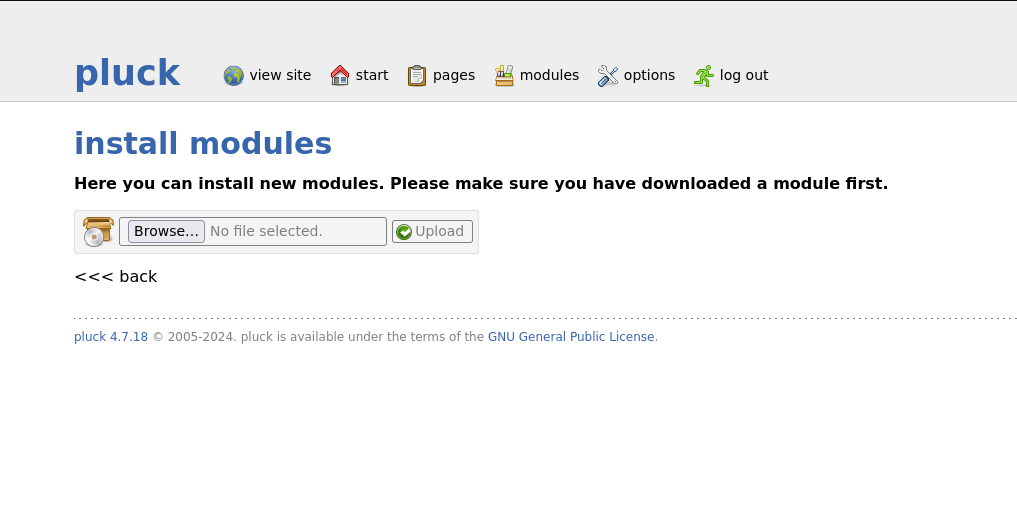
- Modules allows zip file to upload, we can install our payload here
- saved my php in zip and upload
- Note: setup netcat to ready to listen for connection
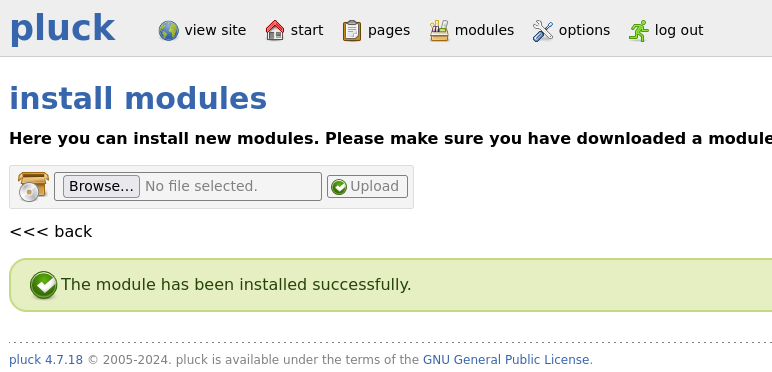
- we got the shell in the app
- /home has 2 dir
- git
- junior
- has user flag and one pdf file.
- download pdf file with setting a server on target.
- the pdf has pixelated password,
- meanwhile, try to su junior and previous worked for this user.
- therefore, that password must be for root access.
- Used online tool to extract the image as screenshot will not be precise to unpixlate the password.
https://tools.pdf24.org/en/extract-images
- Very precise
Found a tool called depix
About the tool:
- Depix exploits the fact that pixelation often averages colors over blocks of pixels. If you know the font and pixelation size, Depix can compare pixel patterns to a library of pre-generated patterns to deduce the original characters.
- we need precise screenshot of this password, as it tried multiple times with try to not get any white space in the image we need to get.python3 depix.py -p screenshot.png -s images/searchimages/debruinseq_notepad_Windows10_closeAndSpaced.png -o output.pnghttps://github.com/spipm/Depix- took few mins to get the output image
Privilege Escalation - To Root:
Escalating.....
- step 1 was to get that pixelated image password : "sidefromsidetheothersidesidefromsidetheotherside"
- tried this password to get to root
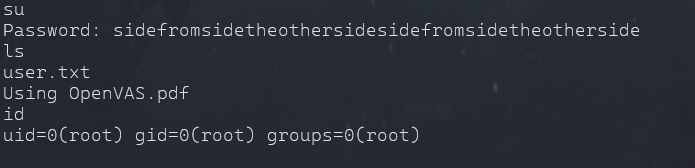
- cd /root and we have our root flag.
Notes:
- Reverse connection can be achieved without manual approach
- It can be done with the PoC.
- Faced connection error on port 80, had to reset machine.
- without manually looking for pass, we could have downloaded repo and used grep but the file could be large.
- Version enumeration, service running are important for getting an RCE and finding useful PoC and CVE.